Alan Turing's name and his work are well known to anybody with a theoretical grounding in computer science. Turing developed his theories well before anybody invented file sharing, overclocking or mass surveillance. In fact, Turing was largely working in the absence of any computers at all: the transistor was only invented in 1947 and the microchip, the critical innovation that has made computing both affordable and portable, only came in 1960, four years after Turing's death. To this day, the
Turing Test remains a well known challenge in the field of Artificial Intelligence. The most prestigious prize in computing, the
A.M. Turing Award from the ACM, equivalent to the Nobel Prize in other fields of endeavour, is named in Turing's honour. (This year's award is another British scientist, Sir Tim Berners-Lee, inventor of the World Wide Web).

Potentially far more people know of Alan Turing for his groundbreaking work at Bletchley Park and the impact it had on cracking the Nazi's Enigma machines during World War 2, giving the allies an advantage against Hitler.
While in his lifetime, Turing exposed the secret communications of the Nazis, in his death, he exposed something manifestly repugnant about his own society. Turing's challenges with his sexuality (or Britain's challenge with it) are just as well documented as his greatest scientific achievements. The 2014 movie
The Imitation Game tells Turing's story, bringing together the themes from his professional and personal life.
Had Turing chosen to flee British persecution by going abroad, he would be a refugee in the same sense as any person who crossed the seas to reach Europe today to avoid persecution elsewhere.
Please prove me wrong
In March, I blogged about the
problem of racism that plagues Britain today. While some may have felt the tone of the blog was quite strong, I was in no way pleased to find my position affirmed by the events that occurred in the two days after the blog appeared.
Two days and two more human beings (both immigrants and both refugees) subjected to abhorrent and unnecessary acts of abuse in Great Britain. Both cases appear to be fuelled directly by the evil that has been oozing out of number 10 Downing Street since they decided to have a referendum on "Brexit".
What stands out about these latest crimes is not that they occurred (this type of thing has been going on for months now) but certain contrasts between their circumstances and to a lesser extent, the fact they occurred immediately after Theresa May formalized Britain's departure from the EU. One of the victims was almost beaten to death by a street gang, while the other was abused by men wearing uniforms. One was only a child, while the other is a mature adult who has been in the UK almost three decades, completely assimilated into British life, working and paying taxes. Both were doing nothing out of the ordinary at the time the abuse occurred: one had engaged in a conversation at a bus stop, the other was on a routine visit to a Government office. There is no evidence that either of them had done anything to provoke or invite the abhorrent treatment meted out to them by the followers of Theresa May and Nigel Farage.
The first victim, on 30 March, was
Stojan Jankovic, a refugee from Yugoslavia who has been in the UK for 26 years. He had a routine meeting at an immigration department office where he was ambushed, thrown in the back of a van and sent to rot in a prison cell by Theresa May's gestapo. On Friday, 31 March, it was
Reker Ahmed, a 17 year old Kurdish-Iranian beaten to the brink of death by a crowd in south London.
One of the more remarkable facts to emerge about these two cases is that while Stojan Jankovic was basically locked up for no reason at all, the street thugs who the police apprehended for the assault on Ahmed were kept in a cell for less than 48 hours and
released again on bail. While the harmless and innocent Jankovic was eventually released after a massive public outcry, he spent more time locked up than that gang of violent criminals who beat Reker Ahmed.
In other words, Theresa May and Nigel Farage's Britain has more concern for the liberty of violent criminals than somebody like Jankovic who has been working and paying taxes in the UK since before any of those street thugs were born.
A deeper insight into Turing's fate
With gay marriage having been legal in the UK for a number of years now,
the rainbow flag flying at the Tate and
Sir Elton John achieving a knighthood, it becomes difficult for people to relate to the world in which Turing and many other victims were collectively classified by their sexuality, systematically persecuted by the state and ultimately died far sooner than they should have. (Turing was only 41 when he died).
In fact, the cruel and brutal forces that ripped Turing apart (and
countless other victims too) haven't dissipated at all, they have simply shifted their target. The slanderous comments insinuating that immigrants "steal" jobs or that Islam is about terrorism are eerily reminiscent of suggestions that gay men abduct young boys or work as Soviet spies. None of these lies has any basis in fact, but repeat them often enough in certain types of newspaper and these ideas spread like weeds.
In an ironic twist, Turing's groundbreaking work at Bletchley Park was founded
on the contributions of Polish mathematicians, their own country having been the first casualty to Hitler, they were also both immigrants and refugees in Britain. Today, under the Theresa May/Nigel Farage leadership, Polish citizens have been subjected to regular vilification by the media and
some have even been killed in the street.
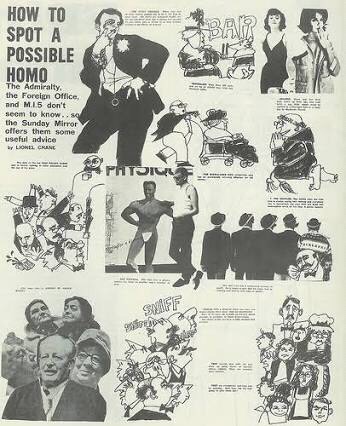
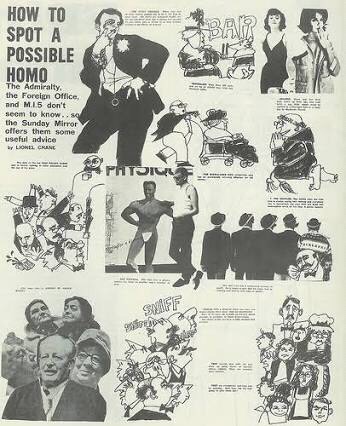
It is said that a picture is worth a thousand words. When you compare these two pieces of propaganda: a
1963 article in the Sunday Mirror advising people "How to spot a possible homo" and a UK Government billboard encouraging people to be on the lookout for people who look different, could you imagine the same type of small-minded and power-hungry tyrants crafting them, singling out a minority so as to keep the public's attention in the wrong place?

Many people have noticed that these latest UK Government posters portray foreigners, Muslims and basically anybody who is not white
using a range of characteristics found in anti-semetic propaganda from the Third Reich:

Do the people who create such propaganda appear to have any concern whatsoever for the people they hurt? How would Alan Turing have felt when he encountered propaganda like that from the Sunday Mirror? Do posters like these encourage us to judge people by their gifts in science, the arts or sporting prowess or do they encourage us to lump them all together based on their physical appearance?
It is a basic expectation of scientific methodology that when you repeat the same experiment, you should get the same result. What type of experiment are Theresa May and Nigel Farage conducting and what type of result would you expect?
Playing ping-pong with children
If anybody has any doubt that this evil comes from the top, take a moment to contemplate the 3,000 children who were baited with the promise of resettlement from the Calais "jungle" camp into the UK under the
Dubs amendment.
When French authorities closed the "jungle" in 2016,
the children were lured out of the camp and left with nowhere to go as Theresa May and French authorities played ping-pong with them. Given that the UK parliament had already agreed they should be accepted, was there any reason for Theresa May to dig her heels in and make these children suffer? Or was she just trying to prove her credentials as somebody who can bastardize migrants just the way Nigel Farage would do it?
How do British politicians really view migrants?
Parliamentarian Keith Vaz, former chair of the Home Affairs Select Committee (responsible for security, crime, prostitution and similar things) was exposed with young men from eastern Europe, encouraging them to take drugs before he ordered them
"Take your shirt off. I'm going to attack you.". How many British MP's see foreigners this way? Next time you are groped at an airport security checkpoint, remember it was people like Keith Vaz and his committee who oversee those abuses, writing among other things
that "The wider introduction of full-body scanners is a welcome development". No need to "take your shirt off" when these machines can look through it as easily as they can look through your children's underwear.
According to the World Health Organization,
HIV/AIDS kills as many people as the September 11 attacks every single day. Keith Vaz apparently had no concern for the possibility he might spread this disease any further: the media reported he doesn't use any protection in his extra-marital relationships.
While Britain's new management continue to round up foreigners like Stojan Jankovic who have done nothing wrong,
they chose not to prosecute Keith Vaz for his antics with drugs and prostitution.
Who is Britain's next Alan Turing?
Britain's next Alan Turing may not be a homosexual. He or she may have been a child turned away by Theresa May's spat with the French at Calais, a migrant bundled into a deportation van by the gestapo (who are just following orders) or perhaps somebody of Muslim appearance who is set upon by thugs in the street who have been energized by Nigel Farage. If you still have any uncertainty about what Brexit really means, this is it. A country that denies itself the opportunity to be great by subjecting itself to be ruled under the "divide and conquer" mantra of the colonial era.
Throughout the centuries, Britain has produced some of the most brilliant scientists of their time. Newton, Darwin and Hawking are just some of those who are even more prominent than Turing, household names around the world. One can only wonder what the history books will have to say about Theresa May and Nigel Farage however.
Next time you see a British policeman accosting a Muslim, whether it is at an airport, in a shopping centre,
keeping Manchester United souvenirs or
simply taking a photograph, spare a thought for Alan Turing and the era when homosexuals were their target of choice.
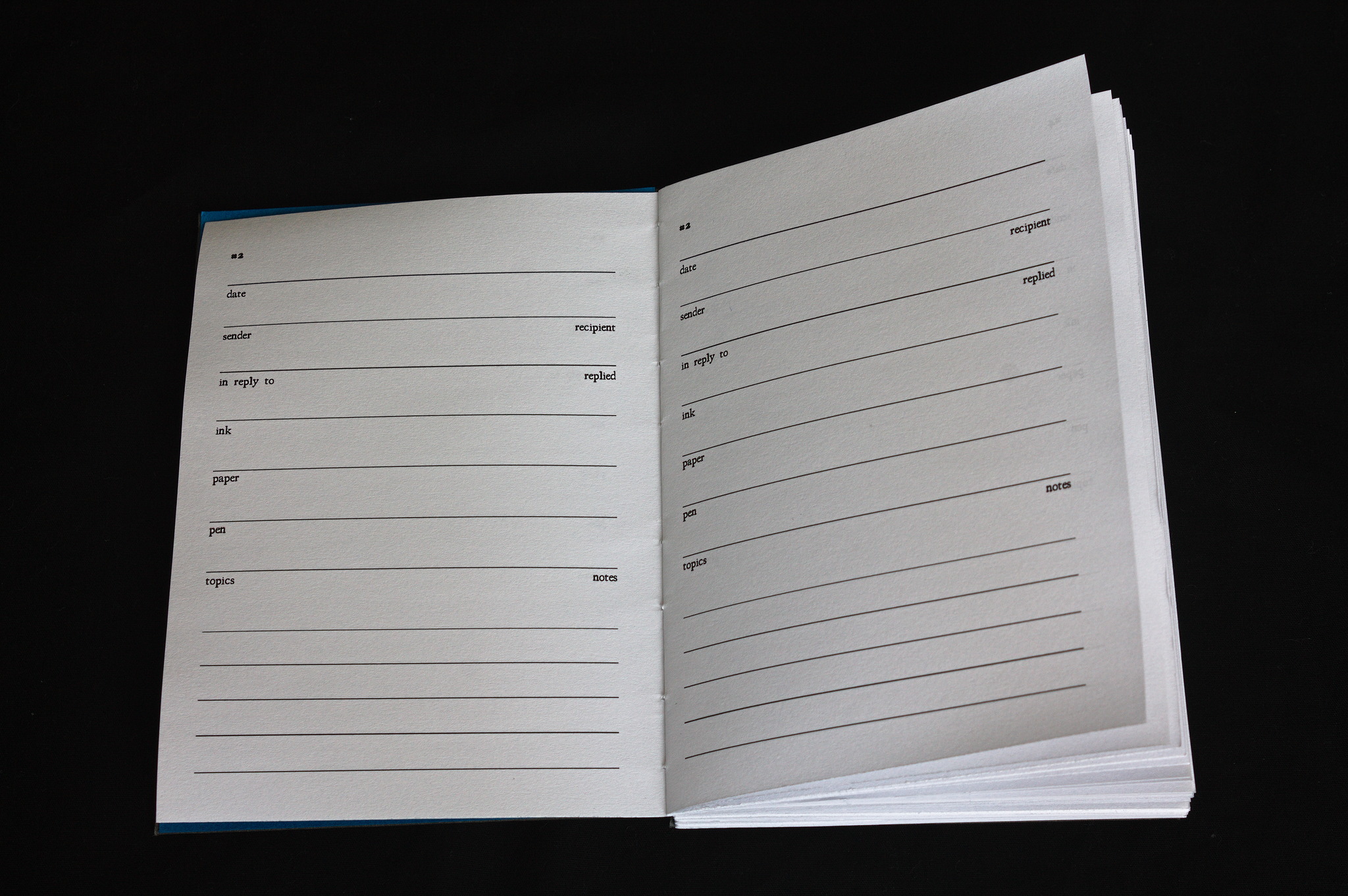
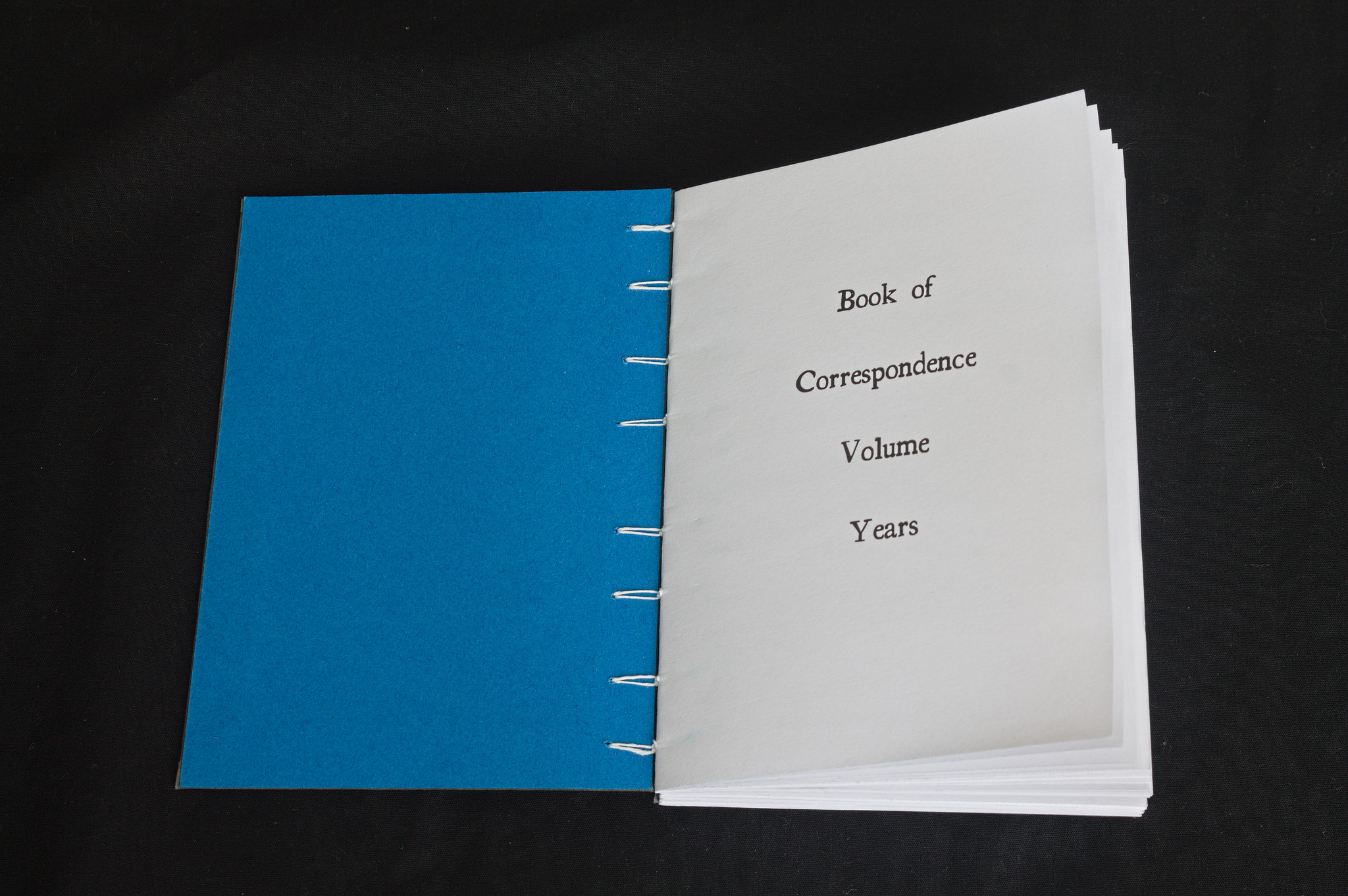 I write letters. The kind that are written on paper with a dip pen 1 and ink, stamped and sent through the post, spend a few days or weeks maturing like good wine in a depot somewhere2, and then get delivered to the recipient.
Some of them (mostly cards) are to people who will receive them and thank me via xmpp (that sounds odd, but actually works out nicely), but others are proper letters with long texts that I exchange with penpals.
Most of those are fountain pen frea^Wenthusiasts, so I usually use a different ink each time, and try to vary the paper, and I need to keep track of what I ve used.
Some time ago, I ve read a Victorian book3 which recommended keeping a correspondence book to register all mail received and sent, the topics and whether it had been replied or otherwise acted upon. I don t have the mail traffic of a Victorian lady (or even middle class woman), but this looked like something fun to do, and if I added fields for the inks and paper used it would also have useful side effect.
I write letters. The kind that are written on paper with a dip pen 1 and ink, stamped and sent through the post, spend a few days or weeks maturing like good wine in a depot somewhere2, and then get delivered to the recipient.
Some of them (mostly cards) are to people who will receive them and thank me via xmpp (that sounds odd, but actually works out nicely), but others are proper letters with long texts that I exchange with penpals.
Most of those are fountain pen frea^Wenthusiasts, so I usually use a different ink each time, and try to vary the paper, and I need to keep track of what I ve used.
Some time ago, I ve read a Victorian book3 which recommended keeping a correspondence book to register all mail received and sent, the topics and whether it had been replied or otherwise acted upon. I don t have the mail traffic of a Victorian lady (or even middle class woman), but this looked like something fun to do, and if I added fields for the inks and paper used it would also have useful side effect.
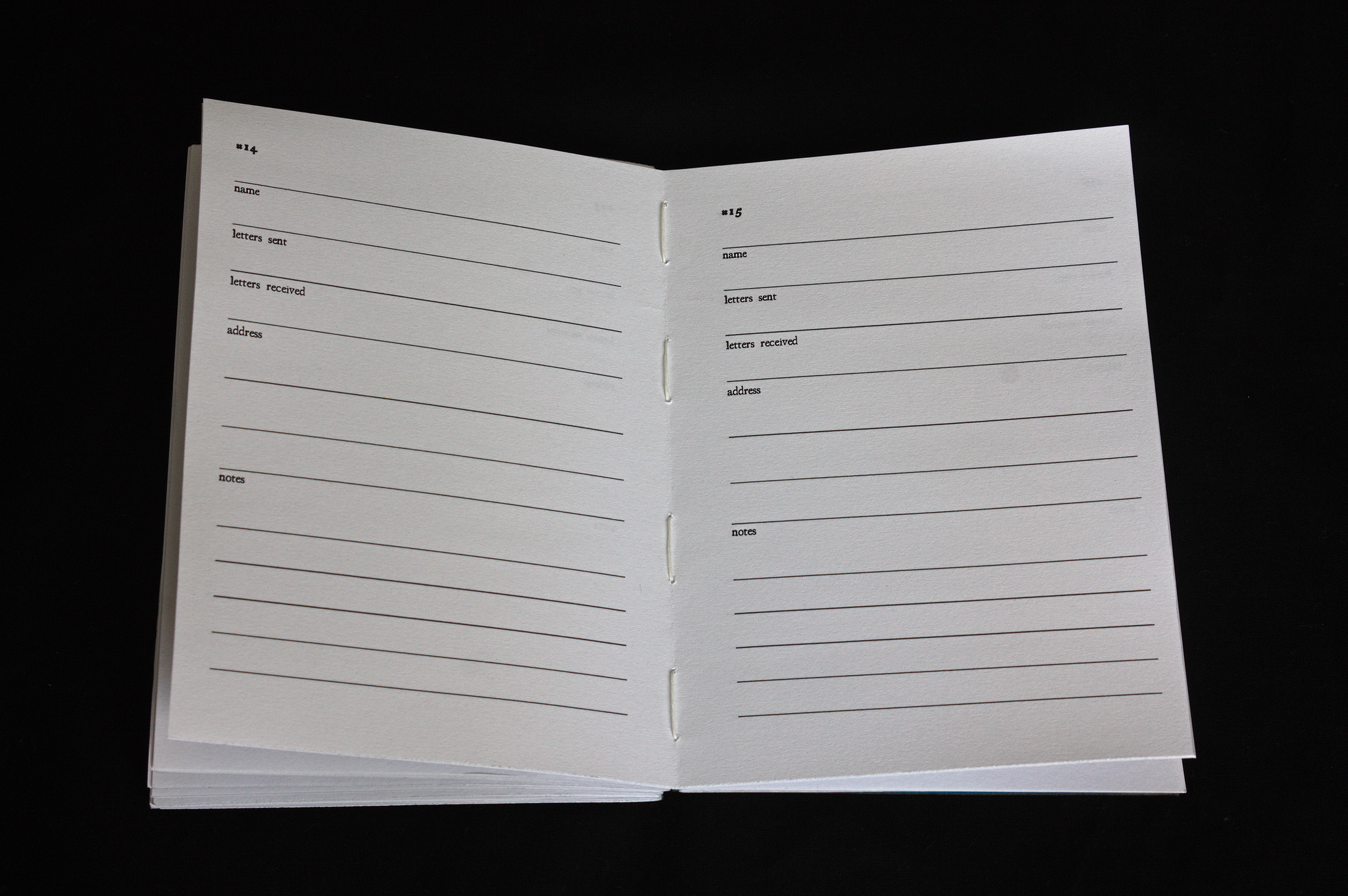 I ve also added a few pages for the addresses of my correspondents (and an index of the letters I ve exchanged with them), and a few empty pages for other notes.
Then I ve used my a6_book.py script to rearrange the A6 pages into signatures and impress them on A4; to reduce later effort I ve added an option to order the pages in such a way that if I then cut four A4 sheet in half at a time (the limit of my rotary cutter) the signatures are ready to be folded. It s not the default because it requires that the pages are a multiple of 32 rather than just 16 (and they are padded up with empty pages if they aren t).
If you re also interested in making one, here are the files:
I ve also added a few pages for the addresses of my correspondents (and an index of the letters I ve exchanged with them), and a few empty pages for other notes.
Then I ve used my a6_book.py script to rearrange the A6 pages into signatures and impress them on A4; to reduce later effort I ve added an option to order the pages in such a way that if I then cut four A4 sheet in half at a time (the limit of my rotary cutter) the signatures are ready to be folded. It s not the default because it requires that the pages are a multiple of 32 rather than just 16 (and they are padded up with empty pages if they aren t).
If you re also interested in making one, here are the files:
 After printing (an older version where some of the pages are repeated. whoops, but it only happened 4 times, and it s not a big deal), it was time for binding this into a book.
I ve opted for Coptic stitch, so that the book will open completely flat and writing on it will be easier and the covers are 2 mm cardboard covered in linen-look bookbinding paper (sadly I no longer have a source for bookbinding cloth made from actual cloth).
After printing (an older version where some of the pages are repeated. whoops, but it only happened 4 times, and it s not a big deal), it was time for binding this into a book.
I ve opted for Coptic stitch, so that the book will open completely flat and writing on it will be easier and the covers are 2 mm cardboard covered in linen-look bookbinding paper (sadly I no longer have a source for bookbinding cloth made from actual cloth).
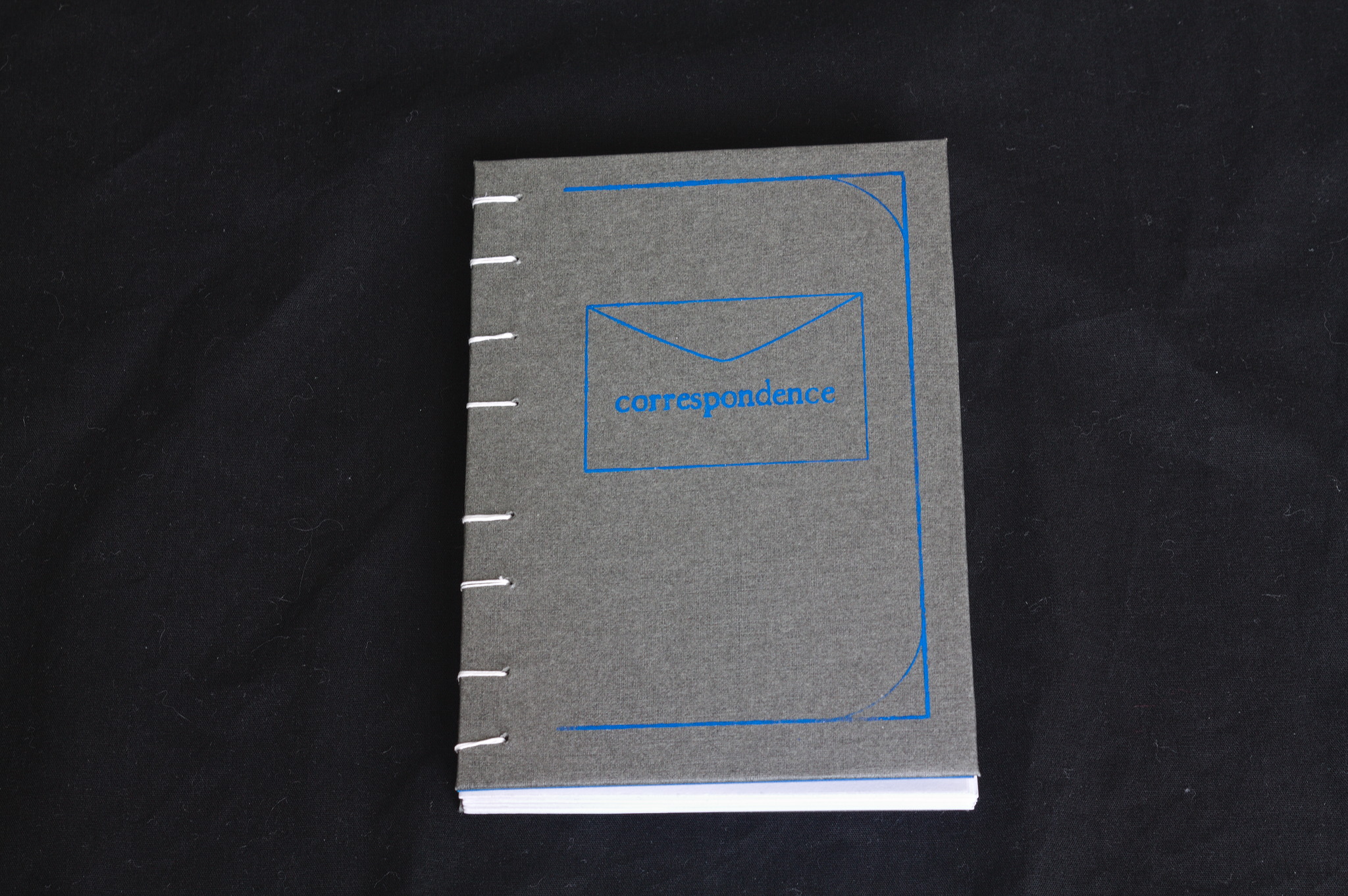 I tried to screenprint a simple design on the cover: the first attempt was unusable (the paper was smaller than the screen, so I couldn t keep it in the right place and moved as I was screenprinting); on the second attempt I used some masking tape to keep the paper in place, and they were a bit better, but I need more practice with the technique.
Finally, I decided that for such a Victorian thing I will use an Iron-gall ink, but it s Rohrer & Knlingner Scabiosa, with a purple undertone, because life s too short to use blue-black ink :D
And now, I m off to write an actual letter, rather than writing online about things that are related to letter writing.
I tried to screenprint a simple design on the cover: the first attempt was unusable (the paper was smaller than the screen, so I couldn t keep it in the right place and moved as I was screenprinting); on the second attempt I used some masking tape to keep the paper in place, and they were a bit better, but I need more practice with the technique.
Finally, I decided that for such a Victorian thing I will use an Iron-gall ink, but it s Rohrer & Knlingner Scabiosa, with a purple undertone, because life s too short to use blue-black ink :D
And now, I m off to write an actual letter, rather than writing online about things that are related to letter writing.












 Many people have noticed that these latest UK Government posters portray foreigners, Muslims and basically anybody who is not white
Many people have noticed that these latest UK Government posters portray foreigners, Muslims and basically anybody who is not white  Do the people who create such propaganda appear to have any concern whatsoever for the people they hurt? How would Alan Turing have felt when he encountered propaganda like that from the Sunday Mirror? Do posters like these encourage us to judge people by their gifts in science, the arts or sporting prowess or do they encourage us to lump them all together based on their physical appearance?
It is a basic expectation of scientific methodology that when you repeat the same experiment, you should get the same result. What type of experiment are Theresa May and Nigel Farage conducting and what type of result would you expect?
Playing ping-pong with children
If anybody has any doubt that this evil comes from the top, take a moment to contemplate the 3,000 children who were baited with the promise of resettlement from the Calais "jungle" camp into the UK under the
Do the people who create such propaganda appear to have any concern whatsoever for the people they hurt? How would Alan Turing have felt when he encountered propaganda like that from the Sunday Mirror? Do posters like these encourage us to judge people by their gifts in science, the arts or sporting prowess or do they encourage us to lump them all together based on their physical appearance?
It is a basic expectation of scientific methodology that when you repeat the same experiment, you should get the same result. What type of experiment are Theresa May and Nigel Farage conducting and what type of result would you expect?
Playing ping-pong with children
If anybody has any doubt that this evil comes from the top, take a moment to contemplate the 3,000 children who were baited with the promise of resettlement from the Calais "jungle" camp into the UK under the _-_Museo_scienza_e_tecnologia_Milano.jpg)
 The other interesting part of the hotel was the wide range of
activities. Again, this being a family hotel, I thought the organised
activities would be pretty mild; but at least for our group, they
weren't. The
The other interesting part of the hotel was the wide range of
activities. Again, this being a family hotel, I thought the organised
activities would be pretty mild; but at least for our group, they
weren't. The
 The
"hike" they organised for another sub-group was also interesting,
involving going through old tunnels and something with broken water
pipes that caused people to either get their feet wet or
monkey-spidering along the walls. Fun!
After the bike ride, on the same afternoon, while walking around the
hotel, we found the Ecole de Trap ze volant open, which looked way
to exciting not to try it. Try and fail to do things right, but
nevertheless it was excellent and unexpected fun. I'll have to do that
again some day when I'll be more fit!
Plus that the hotel itself had a very nice location and olive garden,
so short runs in the morning were very pleasant. Only one cookie
though each
Back home
and then it was over; short, but quite good. The Provence area is
nice, and I'd like to be back again someday, for a proper
vacation longer and more relaxed. And do the trap ze thing again,
properly this time.
The
"hike" they organised for another sub-group was also interesting,
involving going through old tunnels and something with broken water
pipes that caused people to either get their feet wet or
monkey-spidering along the walls. Fun!
After the bike ride, on the same afternoon, while walking around the
hotel, we found the Ecole de Trap ze volant open, which looked way
to exciting not to try it. Try and fail to do things right, but
nevertheless it was excellent and unexpected fun. I'll have to do that
again some day when I'll be more fit!
Plus that the hotel itself had a very nice location and olive garden,
so short runs in the morning were very pleasant. Only one cookie
though each
Back home
and then it was over; short, but quite good. The Provence area is
nice, and I'd like to be back again someday, for a proper
vacation longer and more relaxed. And do the trap ze thing again,
properly this time.
 What happened in the
What happened in the  I published the slides of my talk "
I published the slides of my talk " If traveling in Switzerland to see the mountains, then it works out cheaper to fly into Milan, Italy, which is very close to the Swiss border. Most of the journey from Milan to Vaumarcus can be covered using one of the Swiss railway travel passes, with stops for sight-seeing on the way, and the other days on the pass used for sight-seeing.
Now imagine people arriving in a group: the rail ticket prices quickly add up. For a family of four, 4 * 315 = CHF 1,260. Car rental may be a better option. Hiring a car in Switzerland is expensive, hiring in Italy is much cheaper, the plane tickets to Italy are cheaper too, so there is a lot of money to be saved.
If traveling in Switzerland to see the mountains, then it works out cheaper to fly into Milan, Italy, which is very close to the Swiss border. Most of the journey from Milan to Vaumarcus can be covered using one of the Swiss railway travel passes, with stops for sight-seeing on the way, and the other days on the pass used for sight-seeing.
Now imagine people arriving in a group: the rail ticket prices quickly add up. For a family of four, 4 * 315 = CHF 1,260. Car rental may be a better option. Hiring a car in Switzerland is expensive, hiring in Italy is much cheaper, the plane tickets to Italy are cheaper too, so there is a lot of money to be saved.
 But who wants the hassle of travelling to Switzerland via Italy?
Of course that is the silliest rhetorical question you are going to see this week: visiting Italy is not a hassle at all. Even the Swiss enjoy going there so much that they just built the world's longest rail tunnel under the Alps to bring Como and Milan that little bit closer, the
But who wants the hassle of travelling to Switzerland via Italy?
Of course that is the silliest rhetorical question you are going to see this week: visiting Italy is not a hassle at all. Even the Swiss enjoy going there so much that they just built the world's longest rail tunnel under the Alps to bring Como and Milan that little bit closer, the