Russ Allbery: Review: Shattered Pillars
| Series: | Eternal Sky #2 |
| Publisher: | Tor |
| Copyright: | March 2013 |
| ISBN: | 0-7653-2755-4 |
| Format: | Hardcover |
| Pages: | 333 |
| Series: | Eternal Sky #2 |
| Publisher: | Tor |
| Copyright: | March 2013 |
| ISBN: | 0-7653-2755-4 |
| Format: | Hardcover |
| Pages: | 333 |

 Daily work, get up, have a bath, see if you got a slot on the app, sleep.
Daily work, get up, have a bath, see if you got a slot on the app, sleep.  People trying desperately to get a slot, taken from Hindi Movie Dilwale Dulhania Le Jaygenge.
People trying desperately to get a slot, taken from Hindi Movie Dilwale Dulhania Le Jaygenge.  Cowin app. sceeenshot
Cowin app. sceeenshot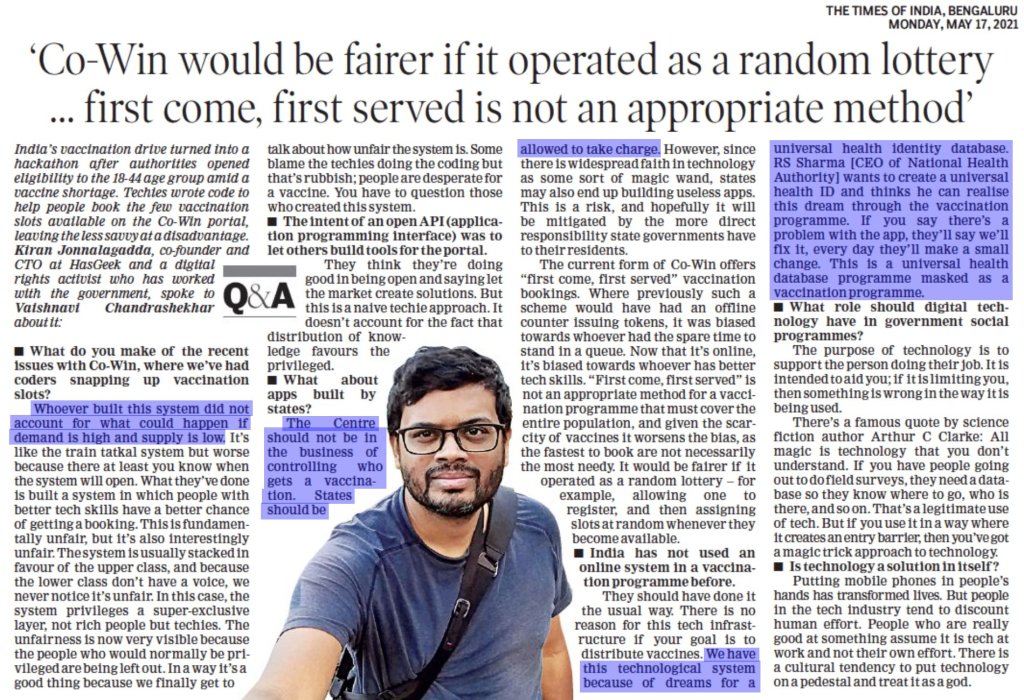
Kiran s Interview in Times of India (TOI) There isn t much to say apart from I haven t used it. I just didn t want to. It just is unethical. Hopefully, in the coming days GOI does something better. That is the only thing we are surviving on, hope.
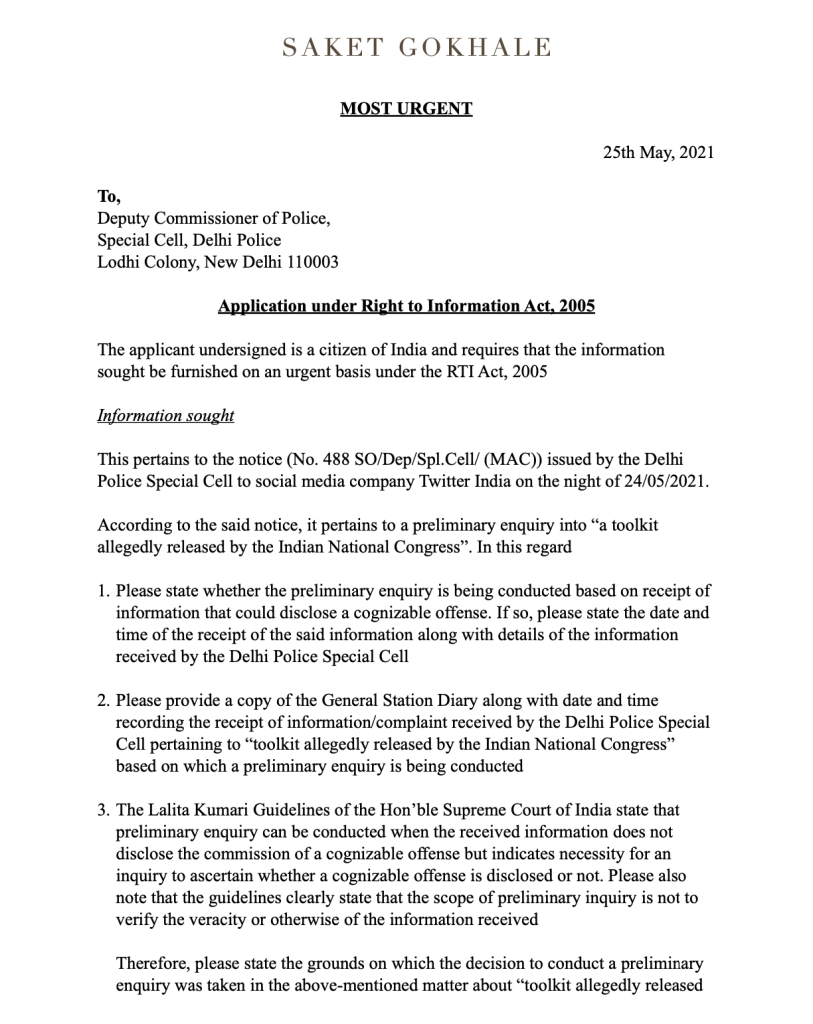 Twitter India Raid, Saket Gokhale RTI 1
Twitter India Raid, Saket Gokhale RTI 1  Saket Gokhale RTI query , Twitter India Raid 2
Saket Gokhale RTI query , Twitter India Raid 2 The Hindu also shared the whole raid on twitter saga.
The Hindu also shared the whole raid on twitter saga.
 I had a twitter fight few days back with a gentleman and the article is a result of that fight. Sadly, I do not know the name of the gentleman as he goes via a psuedo name and then again I ve not taken permission from him to quote him in either way. So I will just state the observations I was able to make from the conversations we had. As people who read this blog regularly would know, I am and have been against Railway Privatization which is happening in India. And will be sharing some of the case studies from other countries as to how it panned out for them.
I had a twitter fight few days back with a gentleman and the article is a result of that fight. Sadly, I do not know the name of the gentleman as he goes via a psuedo name and then again I ve not taken permission from him to quote him in either way. So I will just state the observations I was able to make from the conversations we had. As people who read this blog regularly would know, I am and have been against Railway Privatization which is happening in India. And will be sharing some of the case studies from other countries as to how it panned out for them.
 UK railway map with operators
UK railway map with operators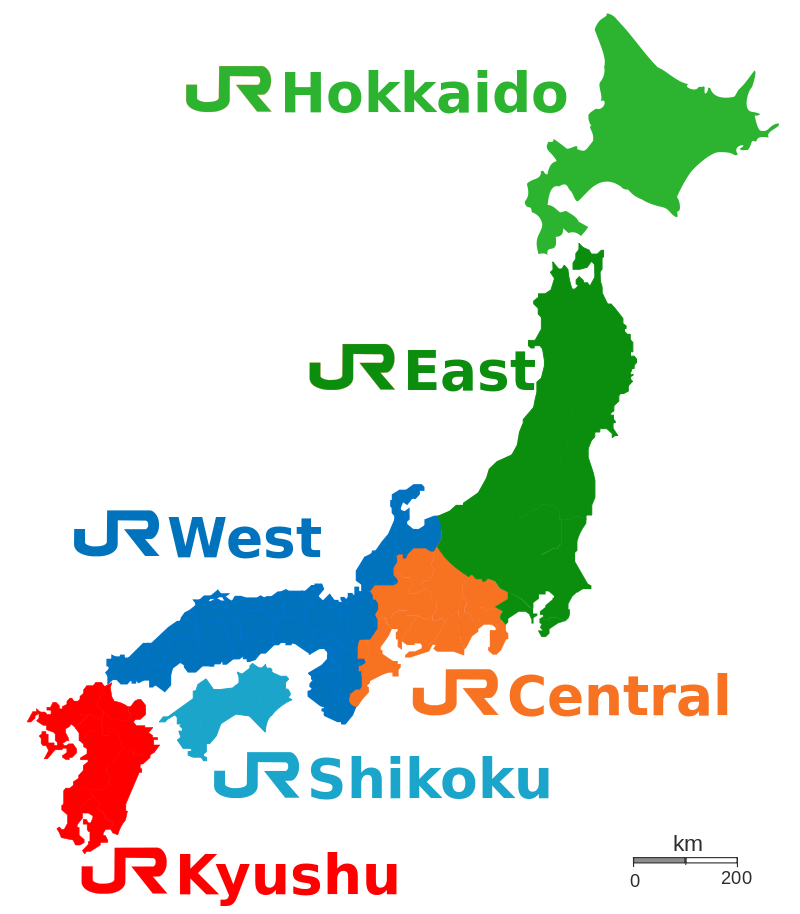 Railway map of Japan with private ownership courtesy Wikimedia commons
Railway map of Japan with private ownership courtesy Wikimedia commons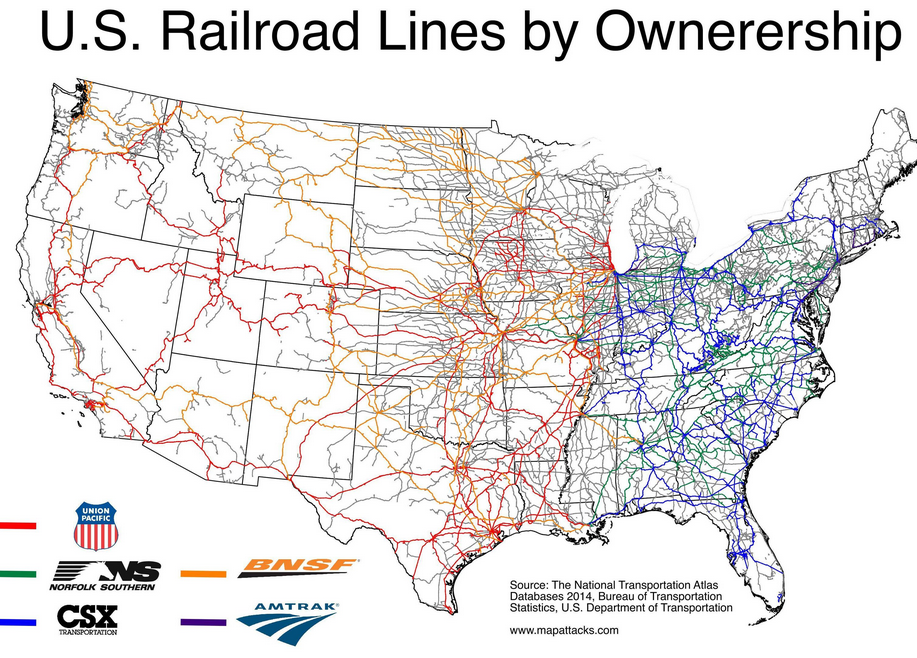 U.S. Railway lines with the different owners
U.S. Railway lines with the different owners  Vaccine issues
Currently, though the issue has been the Vaccine and the pricing of the same. A good article to get a summation of the issues outlined has been shared on Economist. Another article that goes to the heart of the issue is at scroll. To buttress the argument, the SII chairman had shared this few weeks back
Vaccine issues
Currently, though the issue has been the Vaccine and the pricing of the same. A good article to get a summation of the issues outlined has been shared on Economist. Another article that goes to the heart of the issue is at scroll. To buttress the argument, the SII chairman had shared this few weeks back
 Adar Poonawala talking to Vishnu Som on Left, right center, 7th April 2021.
Adar Poonawala talking to Vishnu Som on Left, right center, 7th April 2021.  Prices of AstraZeneca among various states and countries.
Prices of AstraZeneca among various states and countries.Internet Freedom and Aarogya Setu App.
Internet Freedom had shared the chilling effects of the Aarogya Setu App. This had also been shared by FSCI in the past, and recently had their handle being banned on Twitter. This was also apparent in a legal bail order which the high court judge gave. While I won t go into the merits and demerits of the bail order, it is astounding for the judge to say that the accused, even though he would be on bail install an app. so he can be surveilled. And this is a high court judge, such a sad state of affairs. We seem to be putting up new lows every day when it comes to judicial jurisprudence. One interesting aspect of the whole case was shared by Aishwarya Iyer. She shared a story that she and her team worked on quint which raises questions on the quality of the work done by Delhi Police. This is of course, up to Delhi Police to ascertain the truth of the matter because unless and until they are able to tie in the PMO s office in for a leak or POTUS s office it hardly seems possible. For e.g. the dates when two heads of state can meet each other would be decided by the secretaries of the two. Once the date is known, it would be shared with the press while at the same time some sort of security apparatus would kick in place. It is incumbent, especially on the host to take as much care as he can of the guest. We all remember that World War 1 (the war to end all wars) started due to the murder of Archduke Ferdinand.
As nobody wants that, the best way is to make sure that a political murder doesn t happen on your watch. Now while I won t comment on what it would be, it would be safe to assume that it would be z+ security along with higher readiness. Especially if it as somebody as important as POTUS. Now, it would be quite a reach for Delhi Police to connect the two dates. They either will have to get creative with the dates or some other way. Otherwise, with practically no knowledge in the public domain, they can t work in limbo. In either case, I do hope the case comes up for hearing soon and we see what the Delhi Police says and contends in the High Court about the same. At the very least, it would be irritating for them to talk of the dates unless they can contend some mass conspiracy which involves the PMO (and would bring into question the constant vetting done by the Intelligence dept. of all those who work in PMO). And this whole case is to kind of shelter to the Delhi riots which happened in which majorly the Muslims died but their deaths lay unaccounted till date 
Conclusion In Conclusion, I would like to share a bit of humor because right now the atmosphere is humorless, both with authoritarian tendencies of the Central Govt. and the mass mismanagement of public health which they now have left to the state to do as they fit. The peice I am sharing is from arre, one of my goto sites whenever I feel low.
exec startx so after rebooting, I ran
exec sway and to my astonishment sway started. Hooray!
However, I found that ssh-agent wasn't running so I couldn't ssh into
any servers. That's kinda a problem.
Launching ssh-agent under openbox was buried deep in
/etc/X11/Xsession.d/90x11-common_ssh-agent and clearly was not going to
happen via wayland.
Since programs using ssh-agent depend on the environment variables
SSH_AUTH_SOCK and SSH_AGENT_PID being globally available I thought I could
simply run $(eval ssh-agent) via my tty terminal before running exec sway.
And, that would have worked. Except... I like to add my keys via ssh-add -c
so that everytime my key is being used I get a ssh-askpass prompt to confirm
the use.
It seems that since ssh-add is started before a window manager is running, it
can't run the prompt.
Ok, we can fix this. After searching the web, I came upon a solution of running
ssh-agent via systemctl --user:
# This service myst be started manually after sway
# starts.
[Unit]
Description=OpenSSH private key agent
IgnoreOnIsolate=true
[Service]
Type=forking
Environment=SSH_AUTH_SOCK=%t/ssh-agent.socket
ExecStart=/usr/bin/ssh-agent -a $SSH_AUTH_SOCK
~/.bashrc file I have:
if [ -n WAYLAND_DISPLAY ]; then
export SSH_AUTH_SOCK=/run/user/1000/ssh-agent.socket
fi
$SSH_AGENT_PID is only used by ssh-agent to kill itself. Now that
is running via systemd - killing it should be do-able without a global
environment variable.
Done? Hardly.
I've been using impass (nee assword) happily for years but alas it is
tightly integrated with xdo and xclip.
So... I've switched to keepassxc which works out of the box with wayland.
My next challenge was the status bar. Farewell faithful
tint2. One of the reasons I failed on my
first two attempts to switch to Sway was the difficulty of getting the swaybar
to work how I wanted, particularly with nm-applet. Two things allowed me to move forward:
nmtui. Sigh.xclip with
wl-clipboard was a little tedious
but really not that difficult.
Getting my screen shot and screen recorder functionality was a bit harder. I
did a lot of searching before I finally found and compiled both swappy, screen
shot and
wf-recorder.
In the course of all my adventures, I came across the following helpful tips:
libreoffice-gtk3 to ensure libre office runs under waylandMOZ_ENABLE_WAYLAND to ensure firefox works properly.ssh-add command to ensure I am prompted for each use of my key seems to cause sway to crash intermittently.export XDG_CURRENT_DESKTOP=sway and export XDG_SESSION_TYPE=wayland to my .bashrc, and after hours of frustration, realize that I needed to configured firejail to allow it so that I can share my entire screen in Firefox. It doesn't yet support sharing a specific window, so I still have to keep chromium around for that (and Chromium can only share xwayland windows). Sigh. Oh, one more thing about Firefox: the option to choose what to share doesn't have "Entire Screen" as an option, you are just supposed to know that you should choose "Use operating system settings".~/.config/sway/config file I have: bindsym Mod4+e exec wtype " ". I have repeated that line for the main accent marks I need.about:config in the Firefox location window, searching for privacy.webrtc.legacyGlobalIndicator and setting it to False. The reddit thread also suggested finding privacy.webrtc.hideGlobalIndicator and setting it to True, but that setting doesn't seem to be available and setting the first one alone seems to do the trick.GDK_BACKEND=wayland,x11. First I just set it to wayland to get gtk3 apps to use wayland (like gajim). But that broke electron apps (like signal) which notice that variable but don't have a way to display via wayland (at least not yet). Setting it to "wayland,x11" shows the priority. Thank you ubuntu community.~/.config/sway/env. That seems like an official sway place to put them, but sway doesn't pay any attention to them. So I start sway via my own bash script which sources that file via [ -f "$HOME/.config/sway/env" ] && . "$HOME/.config/sway/env" before exec'ing sway. Previously: v4.13.
Linux kernel v4.14 was released this last Sunday, and there s a bunch of security things I think are interesting:
vmapped kernel stack on arm64
Previously: v4.13.
Linux kernel v4.14 was released this last Sunday, and there s a bunch of security things I think are interesting:
vmapped kernel stack on arm64CONFIG_VMAP_STACK for arm64, which moves the kernel stack to an isolated and guard-paged vmap area. With traditional stacks, there were two major risks when exhausting the stack: overwriting the thread_info structure (which contained the addr_limit field which is checked during copy_to/from_user()), and overwriting neighboring stacks (or other things allocated next to the stack). While arm64 previously moved its thread_info off the stack to deal with the former issue, this vmap change adds the last bit of protection by nature of the vmap guard pages. If the kernel tries to write past the end of the stack, it will hit the guard page and fault. (Testing for this is now possible via LKDTM s STACK_GUARD_PAGE_LEADING/TRAILING tests.)
One aspect of the guard page protection that will need further attention (on all architectures) is that if the stack grew because of a giant Variable Length Array on the stack (effectively an implicit alloca() call), it might be possible to jump over the guard page entirely (as seen in the userspace Stack Clash attacks). Thankfully the use of VLAs is rare in the kernel. In the future, hopefully we ll see the addition of PaX/grsecurity s STACKLEAK plugin which, in addition to its primary purpose of clearing the kernel stack on return to userspace, makes sure stack expansion cannot skip over guard pages. This stack probing ability will likely also become directly available from the compiler as well.
set_fs() balance checkingaddr_limit field mentioned above, another class of bug is finding a way to force the kernel into accidentally leaving addr_limit open to kernel memory through an unbalanced call to set_fs(). In some areas of the kernel, in order to reuse userspace routines (usually VFS or compat related), code will do something like: set_fs(KERNEL_DS); ...some code here...; set_fs(USER_DS);. When the USER_DS call goes missing (usually due to a buggy error path or exception), subsequent system calls can suddenly start writing into kernel memory via copy_to_user (where the to user really means within the addr_limit range ).
Thomas Garnier implemented USER_DS checking at syscall exit time for x86, arm, and arm64. This means that a broken set_fs() setting will not extend beyond the buggy syscall that fails to set it back to USER_DS. Additionally, as part of the discussion on the best way to deal with this feature, Christoph Hellwig and Al Viro (and others) have been making extensive changes to avoid the need for set_fs() being used at all, which should greatly reduce the number of places where it might be possible to introduce such a bug in the future.
SLUB freelist hardeningCONFIG_SLAB_FREELIST_HARDENED, makes freelist pointer overwrites very hard to exploit unless an attacker has found a way to expose both the random value and the pointer location. This should render blind heap overflow bugs much more difficult to exploit.
Additionally, Alexander Popov implemented a simple double-free defense, similar to the fasttop check in the GNU C library, which will catch sequential free()s of the same pointer. (And has already uncovered a bug.)
Future work would be to provide similar metadata protections to the SLAB allocator (though SLAB doesn t store its freelist within the individual unused objects, so it has a different set of exposures compared to SLUB).
setuid-exec stack limitationCONFIG_GCC_PLUGIN_RANDSTRUCT, now includes one of the major targets of exploits: function pointer structures. Without knowing the build-randomized location of a callback pointer an attacker needs to overwrite in a structure, exploits become much less reliable.
structleak passed-by-reference variable initializationCONFIG_GCC_PLUGIN_STRUCTLEAK_BYREF_ALL. Normally the compiler will yell if a variable is used before being initialized, but it silences this warning if the variable s address is passed into a function call first, as it has no way to tell if the function did actually initialize the contents. So the plugin now zero-initializes such variables (if they hadn t already been initialized) before the function call that takes their address. Enabling this feature has a small performance impact, but solves many stack content exposure flaws. (In fact at least one such flaw reported during the v4.15 development cycle was mitigated by this plugin.)
improved boot entropySECCOMP_FILTER_FLAG_LOG, he added a new action result, SECCOMP_RET_LOG. With these changes in place, it should be much easier for developers to inspect the results of seccomp filters, and for process launchers to generate logs for their child processes operating under a seccomp filter.
Additionally, I finally found a way to implement an often-requested feature for seccomp, which was to kill an entire process instead of just the offending thread. This was done by creating the SECCOMP_RET_ACTION_FULL mask (n e SECCOMP_RET_ACTION) and implementing SECCOMP_RET_KILL_PROCESS.
That s it for now; please let me know if I missed anything. The v4.15 merge window is now open!
2017, Kees Cook. This work is licensed under a Creative Commons Attribution-ShareAlike 3.0 License.
 I'm currently trying to make sense of some still image coding
(more details to come at a much later stage!), and for a variety
of reasons, I've chosen to use rANS as the entropy coder. However,
there's an interesting little detail that I haven't actually seen
covered anywhere; maybe it's just because I've missed something,
or maybe because it's too blindingly obvious, but I thought I would
document what I ended up with anyway. (I had hoped for something
even more elegant, but I guess the obvious would have to do.)
For those that don't know rANS coding, let me try to handwave it
as much as possible. Your state is typically a single word
(in my case, a 32-bit word), which is refilled from the input stream
as needed. The encoder and decoder works in reverse order;
let's just talk about the decoder. Basically it works by looking
at the lowest 12 (or whatever) bits of the decoder state, mapping
each of those 2^12 slots to a decoded symbol. More common symbols
are given more slots, proportionally to the frequency. Let me just
write a tiny, tiny example with 2 bits and three symbols instead,
giving four slots:
I'm currently trying to make sense of some still image coding
(more details to come at a much later stage!), and for a variety
of reasons, I've chosen to use rANS as the entropy coder. However,
there's an interesting little detail that I haven't actually seen
covered anywhere; maybe it's just because I've missed something,
or maybe because it's too blindingly obvious, but I thought I would
document what I ended up with anyway. (I had hoped for something
even more elegant, but I guess the obvious would have to do.)
For those that don't know rANS coding, let me try to handwave it
as much as possible. Your state is typically a single word
(in my case, a 32-bit word), which is refilled from the input stream
as needed. The encoder and decoder works in reverse order;
let's just talk about the decoder. Basically it works by looking
at the lowest 12 (or whatever) bits of the decoder state, mapping
each of those 2^12 slots to a decoded symbol. More common symbols
are given more slots, proportionally to the frequency. Let me just
write a tiny, tiny example with 2 bits and three symbols instead,
giving four slots:
| Lowest bits | Symbol |
|---|---|
| 00 | 0 |
| 01 | 0 |
| 10 | 1 |
| 11 | 2 |
| Lowest bits | Symbol |
|---|---|
| 000 | 1 |
| 001 | 2 |
| 010 | 0 |
| 011 | 0 |
| 100 | 0 |
| 101 | 0 |
| 110 | -1 |
| 111 | -2 |

 I was in two minds when I read Ritesh s blog post about the Indian Economy. I was angry with Ritesh as he seemed to selectively take facts and present it rather than taking it whole. Even if he had searched even a little bit, he would have got much more better material and everybody would have been the gainer.
I have to also admit, I feel very much like a hypocrite as I have never slaved in a farm so my understanding and conclusions are a mix of media and limited interaction with farmers some years ago. There is also lots of local customs and politics that come into the picture and it s not as straight-forward as Ritesh thinks. What he has failed to share/account for is the far worse bad and stressed debts for the industry so just saying farm loan waivers are bad without sharing any of the context makes it seem much more worse. This is when our Current Chief Economic Adviser states about loan waivers to corporates You need to be able to forgive those debts because this is how capitalism works. People make mistakes, those have to be forgiven to some extent
Let me start though with words from a book I read sometime back
On a peasant uprising erupted in . The farmers were angry with high interest rates, high taxes, high inflation and low-government prices for their crops. The system had let them into debt, and debt had meant foreclosure and loss of their fields to the land barons.
I intentionally have made a fill in the blanks as both the dates and places was true in India 100 years back and even today, the only difference between the two is the absence of taxes. Many people would think I m talking about Champaran whose tale while well-known in India is sadly a stub-class article in wikipedia
I was in two minds when I read Ritesh s blog post about the Indian Economy. I was angry with Ritesh as he seemed to selectively take facts and present it rather than taking it whole. Even if he had searched even a little bit, he would have got much more better material and everybody would have been the gainer.
I have to also admit, I feel very much like a hypocrite as I have never slaved in a farm so my understanding and conclusions are a mix of media and limited interaction with farmers some years ago. There is also lots of local customs and politics that come into the picture and it s not as straight-forward as Ritesh thinks. What he has failed to share/account for is the far worse bad and stressed debts for the industry so just saying farm loan waivers are bad without sharing any of the context makes it seem much more worse. This is when our Current Chief Economic Adviser states about loan waivers to corporates You need to be able to forgive those debts because this is how capitalism works. People make mistakes, those have to be forgiven to some extent
Let me start though with words from a book I read sometime back
On a peasant uprising erupted in . The farmers were angry with high interest rates, high taxes, high inflation and low-government prices for their crops. The system had let them into debt, and debt had meant foreclosure and loss of their fields to the land barons.
I intentionally have made a fill in the blanks as both the dates and places was true in India 100 years back and even today, the only difference between the two is the absence of taxes. Many people would think I m talking about Champaran whose tale while well-known in India is sadly a stub-class article in wikipedia  with quite a few citation needed tags as well
with quite a few citation needed tags as well  but is also true today as will be seen below.
Interestingly, there is/was a remark by some unknown person who said gora sahab gays, bhura sahab aaya meaning the white officer has gone, in his place the brown officer has come. The evidence of this is very much in the Telegraph Act and the story about its usage and its place in Indian politics
Surprisingly, sadly and coincidentally, the quote minus the dates and place didn t happen in India but also in Cambodia. The above quote has been taken from for the sake of all living things by John M. Del Vecchio. The quote itself appears in the first 10 odd pages (historical summation) of the somewhat 1200 odd pages book. I actually got an old edition which tops out at 900 pages so probably some more updated input/news isn t available but it still packs a powerful wallop. I want to dedicate a separate blog post for the book itself so will not say more on that book and what it shares.
Sadly and coincidentally, there were news reports yesterday itself of farmers agitating for better prices just yesterday.
Some of the interesting work if you want to understand the farmer s indebtedness is to study the Income, Expenditure, Productive Assets and Indebtedness of Agricultural Households in India done by NSSO.
Again, one does not need to read the whole report, there were some of the analysis shared by the Hindu here and here. This was also echoed by Logical Indian
It really boggles the mind to know than an average farming household earns around INR 200 per day. Even if you take a family of four people that comes to INR 50/- per person. Most rural joint families at the very least have 3-4 kids at the very least. Sadly Agricultural incomes do not keep sync even with the inflation index as there is no fair minimum age and wage for the Indian farmer, the concept does not exist for her(im)
but is also true today as will be seen below.
Interestingly, there is/was a remark by some unknown person who said gora sahab gays, bhura sahab aaya meaning the white officer has gone, in his place the brown officer has come. The evidence of this is very much in the Telegraph Act and the story about its usage and its place in Indian politics
Surprisingly, sadly and coincidentally, the quote minus the dates and place didn t happen in India but also in Cambodia. The above quote has been taken from for the sake of all living things by John M. Del Vecchio. The quote itself appears in the first 10 odd pages (historical summation) of the somewhat 1200 odd pages book. I actually got an old edition which tops out at 900 pages so probably some more updated input/news isn t available but it still packs a powerful wallop. I want to dedicate a separate blog post for the book itself so will not say more on that book and what it shares.
Sadly and coincidentally, there were news reports yesterday itself of farmers agitating for better prices just yesterday.
Some of the interesting work if you want to understand the farmer s indebtedness is to study the Income, Expenditure, Productive Assets and Indebtedness of Agricultural Households in India done by NSSO.
Again, one does not need to read the whole report, there were some of the analysis shared by the Hindu here and here. This was also echoed by Logical Indian
It really boggles the mind to know than an average farming household earns around INR 200 per day. Even if you take a family of four people that comes to INR 50/- per person. Most rural joint families at the very least have 3-4 kids at the very least. Sadly Agricultural incomes do not keep sync even with the inflation index as there is no fair minimum age and wage for the Indian farmer, the concept does not exist for her(im)  . Just me and mum going onto a restaurant and having one dish each easily can run anywhere between INR 200~250 easily . Cooking in the house is the same if you add/input the labor (which is usually not calculated) used to make lunch/dinner.
There was the idea that contract farming might be a solution but even that was corrupted by Multi-national companies such as Pepsi and others that the Government is showing movement to have a model contracting law . There are loads of stories on downtoearth magazine which deals with the above and all sorts of issues the farmer faces.
I should talk about Maharashtra and even here there was/has been an irrigation scam with figures given from 35k to 70k crores or 350 to 700 billion INR . The latest finding by the PAC has been shared here.
I will cut the blog post short as I find the whole thing personally very depressing. As far as local customs go this was from one of the farmers interaction some years ago where me and some other friends had gone across a village and came to know that all of them grew the same crop with some minor variances. When asked why is it so, while many said its fate, one of the elderly gentleman shared an experience where a farmer had planted some other thing. The gentleman prospered while the other villagers were suffering from glut of whatever they produced. Knowing he prospered, the other villagers damaged his crops and all sorts of unlucky things started happening for the farmer. In the end he realized his best bet is to follow the ways of the other villagers, at least they would be in peace.
What I have shared isn t either unique or even unknown, even Toronto Star of Canada reported on the issue some years ago.
At the end of it all, the story is one of no education and limited skill-set and I don t see it changing any time soon. There are some who are earning big figures, but majority of the farmers will always be in the red
. Just me and mum going onto a restaurant and having one dish each easily can run anywhere between INR 200~250 easily . Cooking in the house is the same if you add/input the labor (which is usually not calculated) used to make lunch/dinner.
There was the idea that contract farming might be a solution but even that was corrupted by Multi-national companies such as Pepsi and others that the Government is showing movement to have a model contracting law . There are loads of stories on downtoearth magazine which deals with the above and all sorts of issues the farmer faces.
I should talk about Maharashtra and even here there was/has been an irrigation scam with figures given from 35k to 70k crores or 350 to 700 billion INR . The latest finding by the PAC has been shared here.
I will cut the blog post short as I find the whole thing personally very depressing. As far as local customs go this was from one of the farmers interaction some years ago where me and some other friends had gone across a village and came to know that all of them grew the same crop with some minor variances. When asked why is it so, while many said its fate, one of the elderly gentleman shared an experience where a farmer had planted some other thing. The gentleman prospered while the other villagers were suffering from glut of whatever they produced. Knowing he prospered, the other villagers damaged his crops and all sorts of unlucky things started happening for the farmer. In the end he realized his best bet is to follow the ways of the other villagers, at least they would be in peace.
What I have shared isn t either unique or even unknown, even Toronto Star of Canada reported on the issue some years ago.
At the end of it all, the story is one of no education and limited skill-set and I don t see it changing any time soon. There are some who are earning big figures, but majority of the farmers will always be in the red
Lenovo-ThinkPad-T500 Source Wikimedia commons
 What probably pissed me is the condensing note in the comment, how does he know what pressures an another individual might be in. It s almost like saying You are refugee because you made a wrong life choice or something to that effect which again is stupid.
I actually feel/felt embarrassed to bring this up as I truly am lucky to be safe, secure, have food on the table, am able to sleep on a bed at night, have a workstation AND a laptop, have somewhat of a sound mind
What probably pissed me is the condensing note in the comment, how does he know what pressures an another individual might be in. It s almost like saying You are refugee because you made a wrong life choice or something to that effect which again is stupid.
I actually feel/felt embarrassed to bring this up as I truly am lucky to be safe, secure, have food on the table, am able to sleep on a bed at night, have a workstation AND a laptop, have somewhat of a sound mind  and a body which is able to move around without any hassles. Add to that, incredibly as it may sound, was also able to see another country for a few days
In relation to people being persecuted and having to run off to save their own lives or even people living on the streets, I am actually living in luxury. While I can t go through life feeling guilty for all the good things that have happened with me, I do feel disgusted when I see some people put blinding statements like that.
One of the biggest reasons that GNU/Linux and Debian in particular gelled with me was that it s incredibly flexible and generous. Nobody tells me which packages I should or shouldn t have. I do right things, good, I do something wrong, an opportunity to learn and hopefully learn from my mistakes. In either case, one of the most forgiving kind of system to learn and hack on.
While speaking of mistakes, could somebody look at #849684 . It almost feels like a tennis match going between the maintainers concerned. While I don t have the technical skills to ascertain who s right and who is not, it would be nice if some cooler heads can make sense and see if a way could be found out. Can somebody help ?
and a body which is able to move around without any hassles. Add to that, incredibly as it may sound, was also able to see another country for a few days
In relation to people being persecuted and having to run off to save their own lives or even people living on the streets, I am actually living in luxury. While I can t go through life feeling guilty for all the good things that have happened with me, I do feel disgusted when I see some people put blinding statements like that.
One of the biggest reasons that GNU/Linux and Debian in particular gelled with me was that it s incredibly flexible and generous. Nobody tells me which packages I should or shouldn t have. I do right things, good, I do something wrong, an opportunity to learn and hopefully learn from my mistakes. In either case, one of the most forgiving kind of system to learn and hack on.
While speaking of mistakes, could somebody look at #849684 . It almost feels like a tennis match going between the maintainers concerned. While I don t have the technical skills to ascertain who s right and who is not, it would be nice if some cooler heads can make sense and see if a way could be found out. Can somebody help ? The Budget
The story which I wanted to share is there are few friends (from Debian as well as elsewhere) who shared that they didn t get the whole demonetisation play or what the Government is/was trying to do. As budget is just round the corner (India will be presenting its yearly budget on 1st of February), thought it is prudent to share at least some basics, ideas and theories of what goals the Finance Minister would be looking at when presenting his budget. I would NOT talk of Inflation targeting or some such exotica as those topics would require their own blog-posts altogether. I would mainly be talking a bit about Taxation and in that Personal Income Tax. I would also not use words like Receivables and like which thought bit more accurate are not used in everyday language.
Just like Private Companies and increasingly public utilities, The Government of the day has two-three different aims when it is presenting a budget
a. The first is to give an update about how things went last year. Did all the incomes that were projected, did it happen or was there a short-fall ? If there was a short-fall what were the reasons for the shortfall.
Similarly, did all the budgeted expenditure earmarked for the year was spent and were it spent under the heads they were supposed to ? If not what went wrong there ? There is usually a tussle between Planned and Unplanned expenditure and one of the hallmarks of good governance is that unplanned expenditure is kept at minimum, while planned expenditure and projects completion or/and assets coming on-line were within the estimated time-frames.
So these updates are given to the Parliament and hence public at large.
The second and the more interesting part are the plans for the immediate future, 1 year down-the-line. Based on the performance last year, a bit of crystal-ball gazing of external and internal conditions of the country, the Finance Minister along with her/his colleagues of Finance Ministry.
Trivia There hasn t been a female finance minister till date in India.
The Finance Ministry as a whole also holds consultations with most sections of the society before sharing/putting his Fiscal Policy (Planned Expenditure) for debate and passage in form of the Budget. While the budget itself is a technical exercise, it is also a Political exercise as both the budget and the finance bill (which contains the taxation proposals) need to be passed in Lok Sabha (Lower house).
After passing scrutiny of Lok Sabha (Lower House having people s representatives directly elected) and Rajya Sabha (Upper House, indirectly elected), the taxation proposals becomes the law. It isn t that simple but for our understanding, keeping it simple. This Political model of governance with two houses is modeled under the British (Westminister) model since 1947.
The Government, just like any other Organization gives a similar Profit and Loss Account and a Balance Sheet.
The Budget
The story which I wanted to share is there are few friends (from Debian as well as elsewhere) who shared that they didn t get the whole demonetisation play or what the Government is/was trying to do. As budget is just round the corner (India will be presenting its yearly budget on 1st of February), thought it is prudent to share at least some basics, ideas and theories of what goals the Finance Minister would be looking at when presenting his budget. I would NOT talk of Inflation targeting or some such exotica as those topics would require their own blog-posts altogether. I would mainly be talking a bit about Taxation and in that Personal Income Tax. I would also not use words like Receivables and like which thought bit more accurate are not used in everyday language.
Just like Private Companies and increasingly public utilities, The Government of the day has two-three different aims when it is presenting a budget
a. The first is to give an update about how things went last year. Did all the incomes that were projected, did it happen or was there a short-fall ? If there was a short-fall what were the reasons for the shortfall.
Similarly, did all the budgeted expenditure earmarked for the year was spent and were it spent under the heads they were supposed to ? If not what went wrong there ? There is usually a tussle between Planned and Unplanned expenditure and one of the hallmarks of good governance is that unplanned expenditure is kept at minimum, while planned expenditure and projects completion or/and assets coming on-line were within the estimated time-frames.
So these updates are given to the Parliament and hence public at large.
The second and the more interesting part are the plans for the immediate future, 1 year down-the-line. Based on the performance last year, a bit of crystal-ball gazing of external and internal conditions of the country, the Finance Minister along with her/his colleagues of Finance Ministry.
Trivia There hasn t been a female finance minister till date in India.
The Finance Ministry as a whole also holds consultations with most sections of the society before sharing/putting his Fiscal Policy (Planned Expenditure) for debate and passage in form of the Budget. While the budget itself is a technical exercise, it is also a Political exercise as both the budget and the finance bill (which contains the taxation proposals) need to be passed in Lok Sabha (Lower house).
After passing scrutiny of Lok Sabha (Lower House having people s representatives directly elected) and Rajya Sabha (Upper House, indirectly elected), the taxation proposals becomes the law. It isn t that simple but for our understanding, keeping it simple. This Political model of governance with two houses is modeled under the British (Westminister) model since 1947.
The Government, just like any other Organization gives a similar Profit and Loss Account and a Balance Sheet.
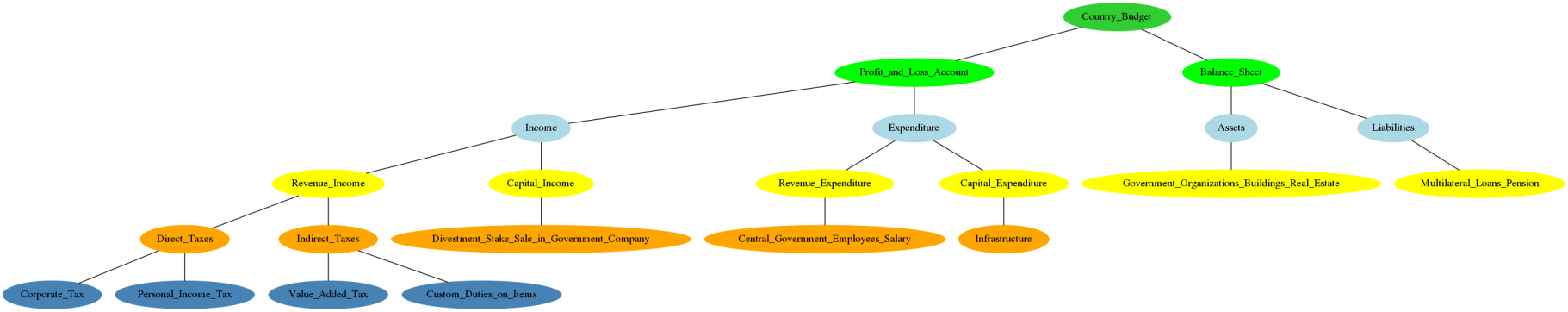
How A country s budget is made. A representational and simplified version of how things flow was made using Graphviz. Click on it to see image in detail.
graph Budget
subgraph tier1
node [color="limegreen",style="filled",group="tier1"]
Country_Budget
......
Country_Budget -- Profit_and_Loss_Account [type=s];

Indian Railways EMU local train

INR 2000 Rupees
 Previously: v4.6. Onward to security things I found interesting in Linux v4.7:
KASLR text base offset for MIPS
Matt Redfearn added text base address KASLR to MIPS, similar to what s available on x86 and arm64. As done with x86, MIPS attempts to gather entropy from various build-time, run-time, and CPU locations in an effort to find reasonable sources during early-boot. MIPS doesn t yet have anything as strong as x86 s
Previously: v4.6. Onward to security things I found interesting in Linux v4.7:
KASLR text base offset for MIPS
Matt Redfearn added text base address KASLR to MIPS, similar to what s available on x86 and arm64. As done with x86, MIPS attempts to gather entropy from various build-time, run-time, and CPU locations in an effort to find reasonable sources during early-boot. MIPS doesn t yet have anything as strong as x86 s RDRAND (though most have an instruction counter like x86 s RDTSC), but it does have the benefit of being able to use Device Tree (i.e. the /chosen/kaslr-seed property) like arm64 does. By my understanding, even without Device Tree, MIPS KASLR entropy should be as strong as pre-RDRAND x86 entropy, which is more than sufficient for what is, similar to x86, not a huge KASLR range anyway: default 8 bits (a span of 16MB with 64KB alignment), though CONFIG_RANDOMIZE_BASE_MAX_OFFSET can be tuned to the device s memory, giving a maximum of 11 bits on 32-bit, and 15 bits on EVA or 64-bit.
SLAB freelist ASLR
Thomas Garnier added CONFIG_SLAB_FREELIST_RANDOM to make slab allocation layouts less deterministic with a per-boot randomized freelist order. This raises the bar for successful kernel slab attacks. Attackers will need to either find additional bugs to help leak slab layout information or will need to perform more complex grooming during an attack. Thomas wrote a post describing the feature in more detail here: Randomizing the Linux kernel heap freelists. (SLAB is done in v4.7, and SLUB in v4.8.)
eBPF JIT constant blinding
Daniel Borkmann implemented constant blinding in the eBPF JIT subsystem. With strong kernel memory protections (CONFIG_DEBUG_RODATA) in place, and with the segregation of user-space memory execution from kernel (i.e SMEP, PXN, CONFIG_CPU_SW_DOMAIN_PAN), having a place where user-space can inject content into an executable area of kernel memory becomes very high-value to an attacker. The eBPF JIT was exactly such a thing: the use of BPF constants could result in the JIT producing instruction flows that could include attacker-controlled instructions (e.g. by directing execution into the middle of an instruction with a constant that would be interpreted as a native instruction). The eBPF JIT already uses a number of other defensive tricks (e.g. random starting position), but this added randomized blinding to any BPF constants, which makes building a malicious execution path in the eBPF JIT memory much more difficult (and helps block attempts at JIT spraying to bypass other protections).
Elena Reshetova updated a 2012 proof-of-concept attack to succeed against modern kernels to help provide a working example of what needed fixing in the JIT. This serves as a thorough regression test for the protection.
The cBPF JITs that exist in ARM, MIPS, PowerPC, and Sparc still need to be updated to eBPF, but when they do, they ll gain all these protections immediatley.
Bottom line is that if you enable the (disabled-by-default) bpf_jit_enable sysctl, be sure to set the bpf_jit_harden sysctl to 2 (to perform blinding even for root).
fix brk ASLR weakness on arm64 compat
There have been a few ASLR fixes recently (e.g. ET_DYN, x86 32-bit unlimited stack), and while reviewing some suggested fixes to arm64 brk ASLR code from Jon Medhurst, I noticed that arm64 s brk ASLR entropy was slightly too low (less than 1 bit) for 64-bit and noticeably lower (by 2 bits) for 32-bit compat processes when compared to native 32-bit arm. I simplified the code by using literals for the entropy. Maybe we can add a sysctl some day to control brk ASLR entropy like was done for mmap ASLR entropy.
LoadPin LSM
LSM stacking is well-defined since v4.2, so I finally upstreamed a small LSM that implements a protection I wrote for Chrome OS several years back. On systems with a static root of trust that extends to the filesystem level (e.g. Chrome OS s coreboot+depthcharge boot firmware chaining to dm-verity, or a system booting from read-only media), it s redundant to sign kernel modules (you ve already got the modules on read-only media: they can t change). The kernel just needs to know they re all coming from the correct location. (And this solves loading known-good firmware too, since there is no convention for signed firmware in the kernel yet.) LoadPin requires that all modules, firmware, etc come from the same mount (and assumes that the first loaded file defines which mount is correct , hence load pinning ).
That s it for v4.7. Prepare yourself for v4.8 next!
2016, Kees Cook. This work is licensed under a Creative Commons Attribution-ShareAlike 3.0 License.
 I have always loved Drum and Bass.
In 2013 I rediscovered my love for
Darkstep and
Neurofunk, and found
that these genres have developed quite a lot in the recent years.
Some labels like
Black Sun Empire and
Evol Intent
produce mixes/sets on a regular basis as podcasts these days.
This article aggregates some neurofunk podcasts I like a lot, most recent first.
Enjoy 33 hours and 57 minutes of fun with dark and energizing beats.
Thanks to BSE Contrax and Evol Intent for providing such high quality sets.
I have always loved Drum and Bass.
In 2013 I rediscovered my love for
Darkstep and
Neurofunk, and found
that these genres have developed quite a lot in the recent years.
Some labels like
Black Sun Empire and
Evol Intent
produce mixes/sets on a regular basis as podcasts these days.
This article aggregates some neurofunk podcasts I like a lot, most recent first.
Enjoy 33 hours and 57 minutes of fun with dark and energizing beats.
Thanks to BSE Contrax and Evol Intent for providing such high quality sets.
Only ONE of us is the kind of person that goes up to guys with machine guns to ask what s happening. Me to Terah todayThey told me that it was the preparations for the opening ceremony for a global shooting contest, and also gave me directions to the bus stop.
 It is a fundamental part of my belief structure that computers should be
silent, unless told otherwise. A default install of
the operating system should not make any sounds, unless there is a
really good reason to. Thus, I object to the following:
It is a fundamental part of my belief structure that computers should be
silent, unless told otherwise. A default install of
the operating system should not make any sounds, unless there is a
really good reason to. Thus, I object to the following:
/etc/gdm3/greeter.gconf-defaults to set
/desktop/gnome/sound/event_sounds to falseamixer -q sset Beep off to shut up wall and other such
tools. (I made an init.d script to make that happen automatically,
and to make sure I don't forget it when I install new machines for myself.)NP237, noshadow, lindi-, flightplan, and others on
#debian-devel with help on shutting up wall.
 I ogled with an OpenMoko FreeRunner since Harald K nig (of X.org
fame) s OpenMoko talk at LinuxDay.at last year. I knew that a team
around Luca Capello and
Joachim
Breitner managed to get Debian running on it.
So when Venty told me that harzi wants to sell his nearly unused FreeRunner, I
couldn t resist and bought it just a few days later.
I played around a little bit with the two distributions which were
already installed, AFAIK the original 2007.2 and a version of Qtopia.
Called Venty with the Qtopia to prove him that you indeed can make
phone calls with this phone, but he wasn t pleased by the echo he
heard of his own voice.
Since the included 512 MB microSD card surely is too small for a large
Debian installation, I bought an additional 8 GB microSDHC card at
digitec and then installed Debian on it.
The installation mostly went smooth: Partitioning threw a timeout
error which didn t cause any further harm than aborting once. A bigger
problem was that the hint that you need to update the U-Boot bootloader itself and
not only its configuration (called environement) to get it booting
from ext2 partitions. lindi (Timo Lindfors) on #openmoko-debian (on
Freenode) was of great help spotting the small details hidden in
continuous text.
After having Debian booting I installed all software I wanted to play
around on a mobile phone including a bunch of web browsers. But since
I ran into a bug which occurs after a non-deterministic amount of data
is written to a big microSD card, I quickly got annoyed by the
fact that I had to wait for the 8 GB fsck each time this bug was
triggered.
So I converted the root file system to ext3 by adding a journal. But
whatever I did (reinstalling U-Boot, the U-Boot environement,
regenerating the U-Boot environement from scratch, trying to load it
as ext2 again, etc.) I didn t get it to work anymore.
On #openmoko
on Freenode, PaulFertser was trying to convince me that Qi is the
better choice of a bootloader. Although its description didn t appeal
to me at all, I understand that U-Boot seems a maintainability hell
and that a more simplicistic approach can have its advantages. But
there was feature listed on the Qi wiki page which made me try it:
explicit ext3 support.
After creating the appropriate configuration files and symbolic links
in /boot/boot and flashing Qi over the U-Boot in the NAND flash,
Debian booted again without problems and with a journaling file
system. :-)
In the meanwhile I found a setup which suites my tastes:
I ogled with an OpenMoko FreeRunner since Harald K nig (of X.org
fame) s OpenMoko talk at LinuxDay.at last year. I knew that a team
around Luca Capello and
Joachim
Breitner managed to get Debian running on it.
So when Venty told me that harzi wants to sell his nearly unused FreeRunner, I
couldn t resist and bought it just a few days later.
I played around a little bit with the two distributions which were
already installed, AFAIK the original 2007.2 and a version of Qtopia.
Called Venty with the Qtopia to prove him that you indeed can make
phone calls with this phone, but he wasn t pleased by the echo he
heard of his own voice.
Since the included 512 MB microSD card surely is too small for a large
Debian installation, I bought an additional 8 GB microSDHC card at
digitec and then installed Debian on it.
The installation mostly went smooth: Partitioning threw a timeout
error which didn t cause any further harm than aborting once. A bigger
problem was that the hint that you need to update the U-Boot bootloader itself and
not only its configuration (called environement) to get it booting
from ext2 partitions. lindi (Timo Lindfors) on #openmoko-debian (on
Freenode) was of great help spotting the small details hidden in
continuous text.
After having Debian booting I installed all software I wanted to play
around on a mobile phone including a bunch of web browsers. But since
I ran into a bug which occurs after a non-deterministic amount of data
is written to a big microSD card, I quickly got annoyed by the
fact that I had to wait for the 8 GB fsck each time this bug was
triggered.
So I converted the root file system to ext3 by adding a journal. But
whatever I did (reinstalling U-Boot, the U-Boot environement,
regenerating the U-Boot environement from scratch, trying to load it
as ext2 again, etc.) I didn t get it to work anymore.
On #openmoko
on Freenode, PaulFertser was trying to convince me that Qi is the
better choice of a bootloader. Although its description didn t appeal
to me at all, I understand that U-Boot seems a maintainability hell
and that a more simplicistic approach can have its advantages. But
there was feature listed on the Qi wiki page which made me try it:
explicit ext3 support.
After creating the appropriate configuration files and symbolic links
in /boot/boot and flashing Qi over the U-Boot in the NAND flash,
Debian booted again without problems and with a journaling file
system. :-)
In the meanwhile I found a setup which suites my tastes:
 Good times. (Though, I have to admit it was considerably more interesting when it got dark and the torches were lit and we tried to avoid melting the beach ball.)
Good times. (Though, I have to admit it was considerably more interesting when it got dark and the torches were lit and we tried to avoid melting the beach ball.)
 Helpfully labelled drinks.
Helpfully labelled drinks.
 Saturday - The Graduation
Good music.
Saturday - The Graduation
Good music.
 Good speeches. (<plug> yes, this is me </plug>)
Good speeches. (<plug> yes, this is me </plug>)
 Saturday - After We Are Graduated
In which I pose with the superintendant.
Saturday - After We Are Graduated
In which I pose with the superintendant.
 In which I pose with my brother outside in the blinding sunshine and blazing heat, while thinking about the cool water that happens to be behind us.
In which I pose with my brother outside in the blinding sunshine and blazing heat, while thinking about the cool water that happens to be behind us.
 In which I pose with my parents and brother in a moderately more forgiving environment at home.
In which I pose with my parents and brother in a moderately more forgiving environment at home.
 In which I pose with my brother and grandparents, who could probably stand in for an alternate Matrix cast, and kick your [posterior]. At least in this picture.
In which I pose with my brother and grandparents, who could probably stand in for an alternate Matrix cast, and kick your [posterior]. At least in this picture.
 In which my cousin Mark discovers that my stole is kinda fun.
In which my cousin Mark discovers that my stole is kinda fun.
 In which a good friend of mine gives me a freaking awesome shirt.
In which a good friend of mine gives me a freaking awesome shirt.
 I will now proceed to summarily disappear off the face of the ‘net from sometime tomorrow until late Monday or so, in which I Move To Cambridge.
I will now proceed to summarily disappear off the face of the ‘net from sometime tomorrow until late Monday or so, in which I Move To Cambridge.
Next.