Russell Coker: Galaxy Note 9 Droidian
Droidian Support for Note 9
Droidian only supported the version of this phone with the Exynos chipset. The GSM Arena specs page for the Note 9 shows that it s the SM-N960F part number [1]. In Australia all Note 9 phones should have the Exynos but it doesn t hurt to ask for the part number before buying.
The status of the Note9 in Droidian went from fully supported to totally unsupported in the time I was working on this blog post. Such a rapid change is disappointing, it would be good if they at least kept the old data online. It would also be good if they didn t require a hash character in the URL for each phone which breaks the archive.org mirroring.
Installing Droidian
Firstly Power+VolumeDown will reboot in some situations where Power button on it s own won t. The Note 9 hardware keys are:
- Power Right side
- Volume up/down long button top of the left side
- Bixby key for Samsung assistant that s below the volume on the left
- The doc says to start by installing Android 10 (Q) stock firmware , but apparently a version of Android 10 that s already on the phone will do for that.
- Download the rescue.img file and the Droidian s image files from the Droidian page and extract the Droidian s image zip.
- Connect your phone to your workstation by USB, preferably USB 3 because it will take a few minutes to transfer the image at USB 2 speed. Install the Debian package adb on the workstation.
- To Unlock the bootloader you can apparently use a PC and the Samsung software but the unlock option in the Android settings gives the same result without proprietary software, here s how to do it:
- Connect the phone to Wifi. Then in settings go to Software update , then click on Download and install . Refuse to install if it offers you a new version (the unlock menu item will never appear unless you do this, so you can t unlock without Internet access).
- In settings go to About phone , then Software information , then tap on Build number repeatedly until Developer mode is enabled.
- In settings go to the new menu Developer options then turn on the OEM unlocking option, this does a factory reset of the phone.
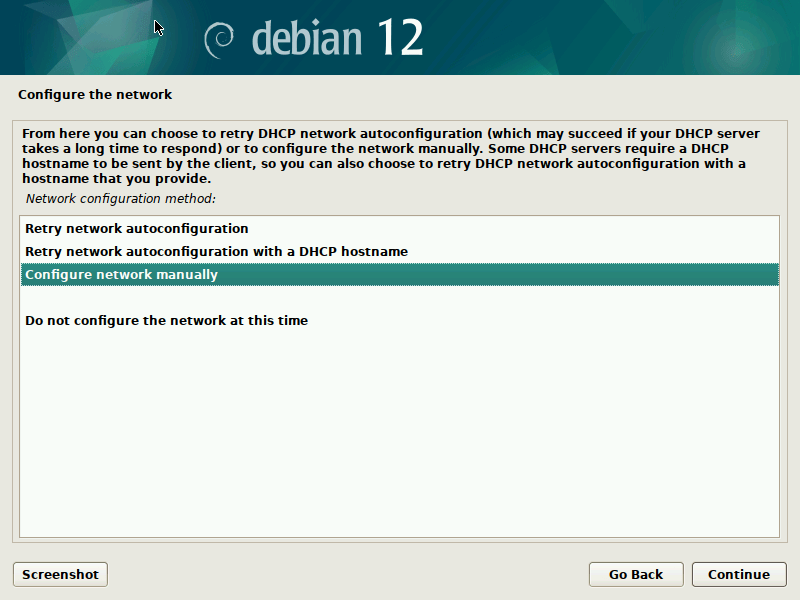
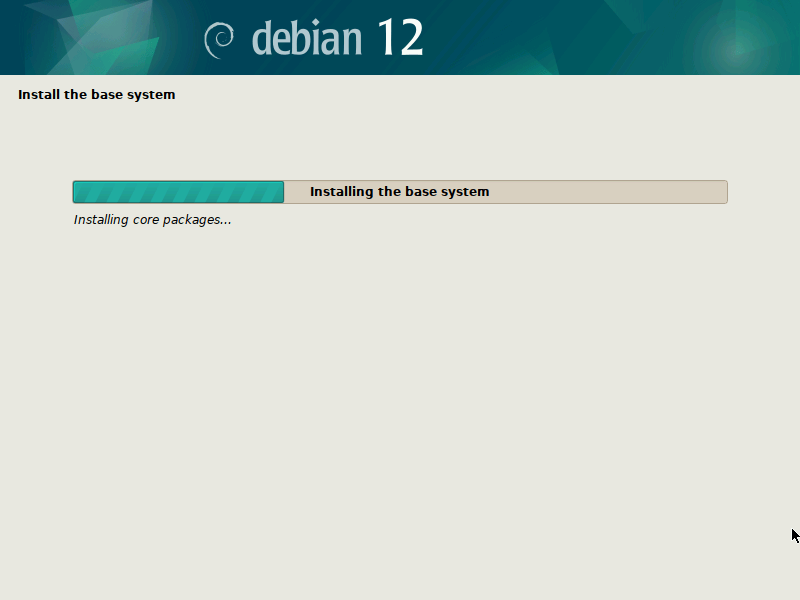
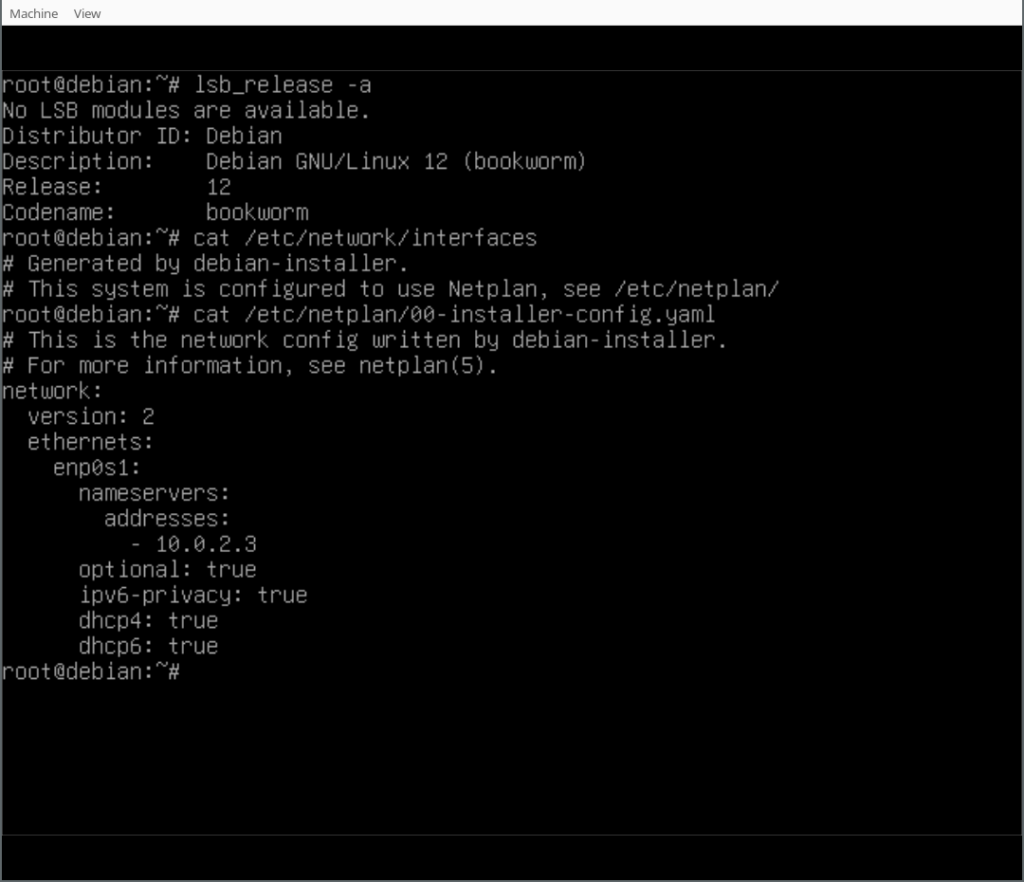
- To flash the recovery.img you apparently use Odin on Windows. I used the heimdall-flash package on Debian. On your Linux workstation run the commands:
adb reboot download heimdall flash --RECOVERY recovery.img
Then press VOLUME-UP+BIXBY+POWER as soon as it reboots to get into the recovery image. If you don t do it soon enough it will do a default Android boot which will wipe the recovery.img you installed and also do a factory reset which will disable Developer mode and you will need to go back to step 4. - If the above step works correctly you will have a RECOVERY menu where the main menu has options Reboot system now , Apply update , Factory reset , and Advanced in a large font. If you failed to install recovery.img then you would get a similar menu but with a tiny font which is the Samsung recovery image which won t work so reboot and try again.
- When at the main recovery menu select Advanced and then Enter fastboot . Note that this doesn t run a different program or do anything obviously different, just gives a menu that s OK we want it at this menu.
- Run ./flash_all.sh on your workstation.
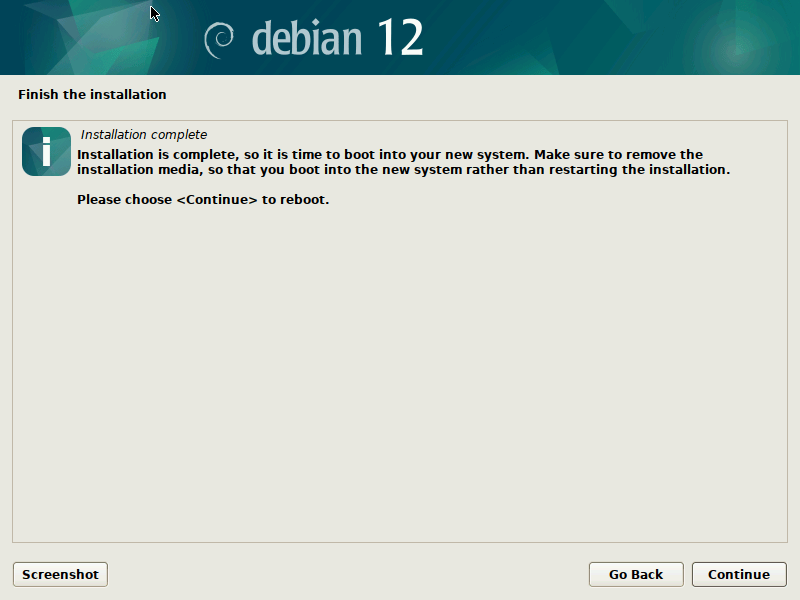
- Then it should boot Droidian! This may take a bit of time.
- Log output of ps auxf equivalent.
- Make notes on what they are doing with SE Linux.
- Test the stylus.
- Test USB networking to my workstation and my laptop.
- Make a copy of the dmesg output. Also look for D state processes and other signs of problems.
- [1] https://www.gsmarena.com/samsung_galaxy_note9-9163.php
- [2] https://etbe.coker.com.au/2023/06/06/pinephonepro-first-impression/
- [3] https://github.com/droidian/droidian/issues/36
- [4] https://github.com/droidian/droidian/issues/37
- [5] https://etbe.coker.com.au/2023/07/08/sandboxing-phone-apps/
- [6] https://tinyurl.com/236bjztz
 Version 0.0.17 of
Version 0.0.17 of  It s been around 6 months since the GNOME Foundation was joined by our new Executive Director, Holly Million, and the board and I wanted to update members on the Foundation s current status and some exciting upcoming changes.
It s been around 6 months since the GNOME Foundation was joined by our new Executive Director, Holly Million, and the board and I wanted to update members on the Foundation s current status and some exciting upcoming changes.

 Time really flies when
Time really flies when 


 Years ago, at what I think I remember was DebConf 15, I hacked for a while
on debhelper to
Years ago, at what I think I remember was DebConf 15, I hacked for a while
on debhelper to
 Those of you who haven t been in IT for far, far too long might not know that next month will be the 16th(!) anniversary of the
Those of you who haven t been in IT for far, far too long might not know that next month will be the 16th(!) anniversary of the 
 They're called The Usual Suspects for a reason, but sometimes, it really is Keyser S ze
They're called The Usual Suspects for a reason, but sometimes, it really is Keyser S ze