
We took a couple of days of for a family vacation / road trip through
the hills of Central Mexico. The overall trip does not look like
anything out of the ordinary
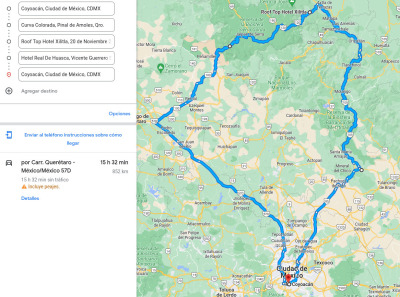
Other than the fact that Google forecasted we d take approximately
15.5 hours driving for 852Km that is, an average of almost 55
Km/h. And yes, that s what we signed up for. And that s what we
got. Of course, the exact routes are not exactly what Google suggested
(I can say we optimized a bit the route, i.e., by avoiding the
metropolitan area of Quer taro, at the extreme west, and going via San
Juan del R o / Tequisquiapan / Bernal).
The first stretch of the road is just a regular, huge highway, with
no particular insights. The highways leaving and entering Mexico City
on the North are not fun nor beautiful, only they are needed to get
nice trips going
Mexico City sits at a point of changing climates. Of course, it is a
huge city And I cannot imagine how it would be without all of the
urbanization it now sports. But anyway: On the West, South, and part
of the East, it is surrounded by high mountains, with beautiful and
dense forests. Mexico City is 2200m high, and most of the valley s
surrounding peaks are ~3000m (and at the South Eastern tip, our two
big volcanoes, Popocat petl and Iztacc huatl, get past the 5700m
mark). Towards the North, the landscape is flatter and much more
dry. Industrial compounds give way to dry grasslands. Of course,
central Mexico does not understand the true meaning of
flat, and the
landscape is full with eh-not-very-big mountains.
Then, as we entered Quer taro State, we started approaching
Bernal. And we saw a huge rock that looks like it is not supposed
to be there! It just does not fit the surroundings.

Shortly after Bernal, we entered a beautiful, although most crumpled,
mountain ridge:
Sierra Gorda de
Quer taro. Sierra Gorda
encompasses most of the North of the (quite small 11500Km total)
state of Quer taro, plus portions of the neighboring states; other
than the very abrupt and sharp orography, what strikes me most is the
habitat diversity it encompasses. We started going up an absolute
desert, harsh and beautiful; we didn t take pictures along the way as
the road is difficult enough that there are almost no points for
stopping for refreshments or for photo opportunities. But it is quite
majestic. And if you think deserts are barren, boring places well,
please do spend some time enjoying them!
Anyway At on point, the road passes by a ~3100m height, and
suddenly Pines! More pines! A beautiful forest! We reached our
first stop at the originally mining town of
Pinal de
Amoles.




After spending the night there and getting a much needed rest, we
started a quite steep descent towards
Jalpan de
Serra. While it is
only ~20Km away on the map, we descended from 2300 to 760 meters of
altitude (and the road was over 40Km long).

Being much lower, the climate drastically changed from cool and humid
to quite warm and the body attitude in the kids does not lie!

In the mid-18th century, Fray Jun pero Serra established five missions
to evangelize the population of this very harsh territory, and the
frontispiece for the church and monastery in Jalpan is quite
breathtaking.





But we were just passing by Jalpan. A short visit to the church and to
the ice-cream shop, and we were again on our way. We crossed the state
border, entering San Luis Potos , and arrived to our main destination:
Xilitla, the little town in
the beautiful
Huasteca where
the jungle meets surrealism.
Xilitla was chosen by the British poet and patron of various
surrealist artists
https://en.wikipedia.org/wiki/Edward_James. He was a British noble (an
unofficial grandson of King
Edward VII), and heir to a huge fortune. I m not going to repeat here
his very well known biography suffice to say that he got in love
with the Huasteca, and bought a >30ha piece of jungle and mountain
close to the Xilitla town, and made it his house. With very ample
economic resources, in the late 1940s he started his lifelong project
of building a surrealist garden.
And Well, that s enough blabbering for me. I m sharing some
pictures I took there. The place is plainly magic and
wonderful. Edward James died in 1984, and his will decrees that after
his death, the jungle should be allowed to reclaim the constructions
so many structures are somewhat crumbling, and it is expected they
will break down in the following decades. But for whoever comes to
Mexico This magic place is definitely worth the heavy ride to the
middle of the mountains and to the middle of the jungle.




















Xilitla now also hosts a very good museum with sculptures by Leonora
Carrington, James long-time friend, but I m not going to abuse this
space with even more pictures. And of course, we did more, and enjoyed
more, during our three days in Xilitla.
And for our way back I wanted to try a different route. We decided
to come back to Mexico City crossing Hidalgo state instead of
Quer taro. I had feared the roads would be in a worse shape or would
be more difficult to travel And I was happy to be proven wrong!

This was the longest driving stretch approximately 6:30 for
250Km. The roads are in quite decent shape, and while there are some
stretches where we were quite lonely (probably the loneliest one was
the sharp ascent from Tamazunchale to the detour before Orizatl n),
the road felt safe and well kept at all times. The sights all across
Eastern Hidalgo are breathtaking, and all furiously green (be it with
really huge fern leaves or with tall, strong pines), until
Zacualtip n.

And just as abruptly or more as when we entered Pinal de Amoles We
crossed Orizatl n, and we were in a breathtaking arid, desert-like
environment again. We crossed the
Barranca de Metztitl n natural
reserve, and arrived to spend the night at Huasca de Ocampo.
There are many more things we could have done starting at Huasca, a
region where old
haciendas thrived, full of natural formations, and
very very interesting. But we were tired and pining to be finally back
home. So we rested until mid-morning and left straight back home in
Mexico City. Three hours later, we were relaxing, preparing lunch, the
kids watching whatever-TV-like-things are called nowadays.
All in all, a very beautiful vacation!
 Now that we are back from our six month period in Argentina, we
decided to adopt a kitten, to bring more diversity into our
lives. Perhaps this little girl will teach us to think outside the
box!
Now that we are back from our six month period in Argentina, we
decided to adopt a kitten, to bring more diversity into our
lives. Perhaps this little girl will teach us to think outside the
box!
 Yesterday we witnessed a solar eclipse Mexico City was not in the
totality range (we reached ~80%), but it was a great experience to go
with the kids. A couple dozen thousand people gathered for a massive
picnic in las islas, the main area inside our university campus.
Yesterday we witnessed a solar eclipse Mexico City was not in the
totality range (we reached ~80%), but it was a great experience to go
with the kids. A couple dozen thousand people gathered for a massive
picnic in las islas, the main area inside our university campus.

 Afterwards, we went briefly back home, then crossed the city to fetch
the little kitten. Of course, the kids were unanimous: Her name is
Eclipse.
Afterwards, we went briefly back home, then crossed the city to fetch
the little kitten. Of course, the kids were unanimous: Her name is
Eclipse.




 For all interested people who are reasonably close to central Argentina, or can
be persuaded to come here in a month s time You are all welcome!
It seems I managed to convince my good friend Mart n Bayo (some Debian people
will remember him, as he was present in DebConf19 in Curitiba, Brazil) to get
some facilities for us to have a nice Debian get-together in Central Argentina.
For all interested people who are reasonably close to central Argentina, or can
be persuaded to come here in a month s time You are all welcome!
It seems I managed to convince my good friend Mart n Bayo (some Debian people
will remember him, as he was present in DebConf19 in Curitiba, Brazil) to get
some facilities for us to have a nice Debian get-together in Central Argentina.

 Over roughly the last year and a half I have been participating as a reviewer in
ACM s
Over roughly the last year and a half I have been participating as a reviewer in
ACM s 
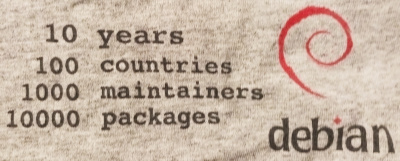
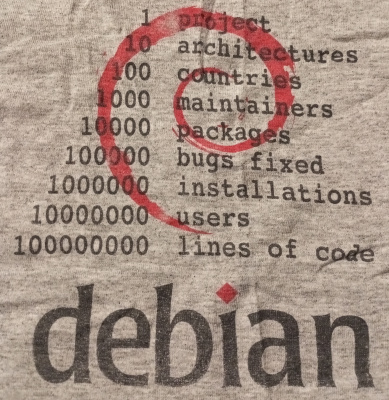
 15 years, "la ni a bonita", if you ask many of my fellow argentinians, is the amount of time I haven't been present in any Debian-related face to face activity. It was already time to fix that. Thanks to Santiago Ruano Rinc n and
15 years, "la ni a bonita", if you ask many of my fellow argentinians, is the amount of time I haven't been present in any Debian-related face to face activity. It was already time to fix that. Thanks to Santiago Ruano Rinc n and  I took the opportunity to do my first trip by ferry, which is currently one of the best options to get from Buenos Aires to Montevideo, in my case through Colonia. Living ~700km at the south west of Buenos Aires city the trip was long, it included a 10 hours bus, a ferry and yet another bus... but of course, it was worth it.
In Buenos Aires' port I met Emmanuel
I took the opportunity to do my first trip by ferry, which is currently one of the best options to get from Buenos Aires to Montevideo, in my case through Colonia. Living ~700km at the south west of Buenos Aires city the trip was long, it included a 10 hours bus, a ferry and yet another bus... but of course, it was worth it.
In Buenos Aires' port I met Emmanuel 










 So This is basically a call for adoption for the Raspberry Debian images
building service. I do intend to stick around and try to help. It s not only me
(although I m responsible for the build itself) we have a nice and healthy
group of Debian people hanging out in the
So This is basically a call for adoption for the Raspberry Debian images
building service. I do intend to stick around and try to help. It s not only me
(although I m responsible for the build itself) we have a nice and healthy
group of Debian people hanging out in the 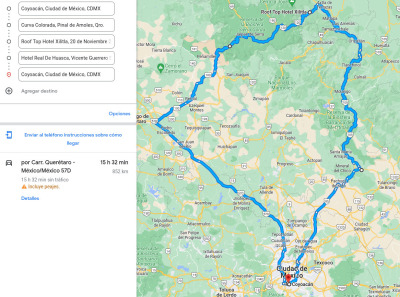





































 Way back at
Way back at  Maybe by sheer chance it was today also that we spent the evening at
Max s house I never worked directly with Max, but we both worked at
Universidad Pedag gica Nacional at the same time back then.
But Of course, a single twentyversary is not enough!
I don t have the exact date, but I guess I might be off by some two or
three months due to other things I remember from back then.
This year, I am forty years old as an Emacs and TeX user!
Back in 1983, on Friday nights, I went with my father to IIMAS (where
I m currently adscribed to as a PhD student, and where he was a
researcher between 1971 and the mid-1990s) and used the computer
one of the two big computers they had in the Institute. And what could
a seven-year-old boy do? Of course use the programs this great
Foonly F2 system had. Emacs and TeX (this is still before LaTeX).
40 years And I still use the same base tools for my daily work, day
in, day out.
Maybe by sheer chance it was today also that we spent the evening at
Max s house I never worked directly with Max, but we both worked at
Universidad Pedag gica Nacional at the same time back then.
But Of course, a single twentyversary is not enough!
I don t have the exact date, but I guess I might be off by some two or
three months due to other things I remember from back then.
This year, I am forty years old as an Emacs and TeX user!
Back in 1983, on Friday nights, I went with my father to IIMAS (where
I m currently adscribed to as a PhD student, and where he was a
researcher between 1971 and the mid-1990s) and used the computer
one of the two big computers they had in the Institute. And what could
a seven-year-old boy do? Of course use the programs this great
Foonly F2 system had. Emacs and TeX (this is still before LaTeX).
40 years And I still use the same base tools for my daily work, day
in, day out.