Melissa Wen: Get Ready to 2024 Linux Display Next Hackfest in A Coru a!
Who s Joining the Fun?
We re excited to welcome participants from various backgrounds, including:
- GPU hardware vendors;
- Linux distributions;
- Linux desktop environments and compositors;
- Color experts, researchers and enthusiasts;
This diverse mix of backgrounds are represented by developers from several
companies working on the Linux display stack: AMD, Arm, BlueSystems, Bootlin,
Collabora, Google, GravityXR, Igalia, Intel, LittleCMS, Qualcomm, Raspberry Pi,
RedHat, SUSE, and System76. It ll ensure a dynamic exchange of perspectives and
foster collaboration across the Linux Display community.
Please take a look at the
list of participants
for more info.
What s on the Agenda?
The beauty of the hackfest is that the agenda is driven by participants! As
this is a hybrid event, we decided to improve the experience for remote
participants by creating a dedicated space for them to propose topics and some
introductory talks in advance. From those inputs, we defined a schedule that
reflects the collective interests of the group, but is still open for
amendments and new proposals. Find the schedule details in the official event
webpage.
Expect discussions on:
KMS Color/HDR
- Proposal with new DRM object type:
- Brief presentation of GPU-vendor features;
- Status update of plane color management pipeline per vendor on Linux;
- HDR/Color Use-cases:
- HDR gainmap images and how should we think about HDR;
- Google/ChromeOS GFX view about HDR/per-plane color management, VKMS and lessons learned;
- Post-blending Color Pipeline.
- Color/HDR testing/CI
- VKMS status update;
- Chamelium boards, video capture.
- Wayland protocols
- color-management protocol status update;
- color-representation and video playback.
Display control
- HDR signalling status update;
- backlight status update;
- EDID and DDC/CI.
Strategy for video and gaming use-cases
- Multi-plane support in compositors
- Underlay, overlay, or mixed strategy for video and gaming use-cases;
- KMS Plane UAPI to simplify the plane arrangement problem;
- Shared plane arrangement algorithm desired.
- HDR video and hardware overlay
Frame timing and VRR
- Frame timing:
- Limitations of uAPI;
- Current user space solutions;
- Brainstorm better uAPI;
- Cursor/overlay plane updates with VRR;
- KMS commit and buffer-readiness deadlines;
Power Saving vs Color/Latency
- ABM (adaptive backlight management);
- PSR1 latencies;
- Power optimization vs color accuracy/latency requirements.
Content-Adaptive Scaling & Sharpening
- Content-Adaptive Scalers on display hardware;
- New drm_colorop for content adaptive scaling;
- Proprietary algorithms.
Display Mux
- Laptop muxes for switching of the embedded panel between the integrated GPU and the discrete GPU;
- Seamless/atomic hand-off between drivers on Linux desktops.
Real time scheduling & async KMS API
- Potential benefits: lower latency input feedback, better VRR handling, buffer synchronization, etc.
- Issues around async uAPI usage and async-call handling.
In-person, but also geographically-distributed event
This year Linux Display Next hackfest is a hybrid event, hosted onsite at the
Igalia offices and available for remote attendance. In-person participants will
find an environment for networking and brainstorming in our inspiring and
collaborative office space. Additionally, A Coru a itself is a gem waiting to
be explored, with stunning beaches, good food, and historical sites.

Semi-structured structure: how the 2024 Linux Display Next Hackfest will work
- Agenda: Participants proposed the topics and talks for discussing in
sessions.
- Interactive Sessions: Discussions, workshops, introductory talks and
brainstorming sessions lasting around 1h30. There is always a starting point
for discussions and new ideas will emerge in real time.
- Immersive experience: We will have coffee-breaks between sessions and
lunch time at the office for all in-person participants. Lunches and
coffee-breaks are sponsored by Igalia. This will keep us sharing knowledge and
in continuous interaction.
- Spaces for all group sizes: In-person participants will find different
room sizes that match various group sizes at Igalia HQ. Besides that, there
will be some devices for showcasing and real-time demonstrations.
Social Activities: building connections beyond the sessions
To make the most of your time in A Coru a, we ll be organizing some social activities:
- First-day Dinner: In-person participants will enjoy a Galician dinner on
Tuesday, after a first day of intensive discussions in the hackfest.
- Getting to know a little of A Coru a: Finding out a little about A Coru a
and current local habits.

- On Thursday afternoon, we will close the 2024 Linux Display Next hackfest
with a guided tour of the Museum of Galicia s favorite beer brand, Estrella
Galicia. The guided tour covers the eight sectors of the museum and ends with
beer pouring and tasting. After this experience, a transfer bus will take us to
the Maria Pita square.
- At Maria Pita square we will see the charm of some historical landmarks of
A Coru a, explore the casual and vibrant style of the city center and taste
local foods while chatting with friends.
Sponsorship
Igalia sponsors lunches and coffee-breaks on hackfest days, Tuesday s dinner,
and the social event on Thursday afternoon for in-person participants.
 We can t wait to welcome hackfest attendees to A Coru a! Stay tuned for further
details and outcomes of this unconventional and unique experience.
We can t wait to welcome hackfest attendees to A Coru a! Stay tuned for further
details and outcomes of this unconventional and unique experience.
KMS Color/HDR
- Proposal with new DRM object type:
- Brief presentation of GPU-vendor features;
- Status update of plane color management pipeline per vendor on Linux;
- HDR/Color Use-cases:
- HDR gainmap images and how should we think about HDR;
- Google/ChromeOS GFX view about HDR/per-plane color management, VKMS and lessons learned;
- Post-blending Color Pipeline.
- Color/HDR testing/CI
- VKMS status update;
- Chamelium boards, video capture.
- Wayland protocols
- color-management protocol status update;
- color-representation and video playback.
Display control
- HDR signalling status update;
- backlight status update;
- EDID and DDC/CI.
Strategy for video and gaming use-cases
- Multi-plane support in compositors
- Underlay, overlay, or mixed strategy for video and gaming use-cases;
- KMS Plane UAPI to simplify the plane arrangement problem;
- Shared plane arrangement algorithm desired.
- HDR video and hardware overlay
Frame timing and VRR
- Frame timing:
- Limitations of uAPI;
- Current user space solutions;
- Brainstorm better uAPI;
- Cursor/overlay plane updates with VRR;
- KMS commit and buffer-readiness deadlines;
Power Saving vs Color/Latency
- ABM (adaptive backlight management);
- PSR1 latencies;
- Power optimization vs color accuracy/latency requirements.
Content-Adaptive Scaling & Sharpening
- Content-Adaptive Scalers on display hardware;
- New drm_colorop for content adaptive scaling;
- Proprietary algorithms.
Display Mux
- Laptop muxes for switching of the embedded panel between the integrated GPU and the discrete GPU;
- Seamless/atomic hand-off between drivers on Linux desktops.
Real time scheduling & async KMS API
- Potential benefits: lower latency input feedback, better VRR handling, buffer synchronization, etc.
- Issues around async uAPI usage and async-call handling.
In-person, but also geographically-distributed event
This year Linux Display Next hackfest is a hybrid event, hosted onsite at the
Igalia offices and available for remote attendance. In-person participants will
find an environment for networking and brainstorming in our inspiring and
collaborative office space. Additionally, A Coru a itself is a gem waiting to
be explored, with stunning beaches, good food, and historical sites.

Semi-structured structure: how the 2024 Linux Display Next Hackfest will work
- Agenda: Participants proposed the topics and talks for discussing in
sessions.
- Interactive Sessions: Discussions, workshops, introductory talks and
brainstorming sessions lasting around 1h30. There is always a starting point
for discussions and new ideas will emerge in real time.
- Immersive experience: We will have coffee-breaks between sessions and
lunch time at the office for all in-person participants. Lunches and
coffee-breaks are sponsored by Igalia. This will keep us sharing knowledge and
in continuous interaction.
- Spaces for all group sizes: In-person participants will find different
room sizes that match various group sizes at Igalia HQ. Besides that, there
will be some devices for showcasing and real-time demonstrations.
Social Activities: building connections beyond the sessions
To make the most of your time in A Coru a, we ll be organizing some social activities:
- First-day Dinner: In-person participants will enjoy a Galician dinner on
Tuesday, after a first day of intensive discussions in the hackfest.
- Getting to know a little of A Coru a: Finding out a little about A Coru a
and current local habits.

- On Thursday afternoon, we will close the 2024 Linux Display Next hackfest
with a guided tour of the Museum of Galicia s favorite beer brand, Estrella
Galicia. The guided tour covers the eight sectors of the museum and ends with
beer pouring and tasting. After this experience, a transfer bus will take us to
the Maria Pita square.
- At Maria Pita square we will see the charm of some historical landmarks of
A Coru a, explore the casual and vibrant style of the city center and taste
local foods while chatting with friends.
Sponsorship
Igalia sponsors lunches and coffee-breaks on hackfest days, Tuesday s dinner,
and the social event on Thursday afternoon for in-person participants.
 We can t wait to welcome hackfest attendees to A Coru a! Stay tuned for further
details and outcomes of this unconventional and unique experience.
We can t wait to welcome hackfest attendees to A Coru a! Stay tuned for further
details and outcomes of this unconventional and unique experience.
- Brief presentation of GPU-vendor features;
- Status update of plane color management pipeline per vendor on Linux;
- HDR gainmap images and how should we think about HDR;
- Google/ChromeOS GFX view about HDR/per-plane color management, VKMS and lessons learned;
- VKMS status update;
- Chamelium boards, video capture.
- color-management protocol status update;
- color-representation and video playback.
- HDR signalling status update;
- backlight status update;
- EDID and DDC/CI.
Strategy for video and gaming use-cases
- Multi-plane support in compositors
- Underlay, overlay, or mixed strategy for video and gaming use-cases;
- KMS Plane UAPI to simplify the plane arrangement problem;
- Shared plane arrangement algorithm desired.
- HDR video and hardware overlay
Frame timing and VRR
- Frame timing:
- Limitations of uAPI;
- Current user space solutions;
- Brainstorm better uAPI;
- Cursor/overlay plane updates with VRR;
- KMS commit and buffer-readiness deadlines;
Power Saving vs Color/Latency
- ABM (adaptive backlight management);
- PSR1 latencies;
- Power optimization vs color accuracy/latency requirements.
Content-Adaptive Scaling & Sharpening
- Content-Adaptive Scalers on display hardware;
- New drm_colorop for content adaptive scaling;
- Proprietary algorithms.
Display Mux
- Laptop muxes for switching of the embedded panel between the integrated GPU and the discrete GPU;
- Seamless/atomic hand-off between drivers on Linux desktops.
Real time scheduling & async KMS API
- Potential benefits: lower latency input feedback, better VRR handling, buffer synchronization, etc.
- Issues around async uAPI usage and async-call handling.
In-person, but also geographically-distributed event
This year Linux Display Next hackfest is a hybrid event, hosted onsite at the
Igalia offices and available for remote attendance. In-person participants will
find an environment for networking and brainstorming in our inspiring and
collaborative office space. Additionally, A Coru a itself is a gem waiting to
be explored, with stunning beaches, good food, and historical sites.

Semi-structured structure: how the 2024 Linux Display Next Hackfest will work
- Agenda: Participants proposed the topics and talks for discussing in
sessions.
- Interactive Sessions: Discussions, workshops, introductory talks and
brainstorming sessions lasting around 1h30. There is always a starting point
for discussions and new ideas will emerge in real time.
- Immersive experience: We will have coffee-breaks between sessions and
lunch time at the office for all in-person participants. Lunches and
coffee-breaks are sponsored by Igalia. This will keep us sharing knowledge and
in continuous interaction.
- Spaces for all group sizes: In-person participants will find different
room sizes that match various group sizes at Igalia HQ. Besides that, there
will be some devices for showcasing and real-time demonstrations.
Social Activities: building connections beyond the sessions
To make the most of your time in A Coru a, we ll be organizing some social activities:
- First-day Dinner: In-person participants will enjoy a Galician dinner on
Tuesday, after a first day of intensive discussions in the hackfest.
- Getting to know a little of A Coru a: Finding out a little about A Coru a
and current local habits.

- On Thursday afternoon, we will close the 2024 Linux Display Next hackfest
with a guided tour of the Museum of Galicia s favorite beer brand, Estrella
Galicia. The guided tour covers the eight sectors of the museum and ends with
beer pouring and tasting. After this experience, a transfer bus will take us to
the Maria Pita square.
- At Maria Pita square we will see the charm of some historical landmarks of
A Coru a, explore the casual and vibrant style of the city center and taste
local foods while chatting with friends.
Sponsorship
Igalia sponsors lunches and coffee-breaks on hackfest days, Tuesday s dinner,
and the social event on Thursday afternoon for in-person participants.
 We can t wait to welcome hackfest attendees to A Coru a! Stay tuned for further
details and outcomes of this unconventional and unique experience.
We can t wait to welcome hackfest attendees to A Coru a! Stay tuned for further
details and outcomes of this unconventional and unique experience.
- Underlay, overlay, or mixed strategy for video and gaming use-cases;
- KMS Plane UAPI to simplify the plane arrangement problem;
- Shared plane arrangement algorithm desired.
- Frame timing:
- Limitations of uAPI;
- Current user space solutions;
- Brainstorm better uAPI;
- Cursor/overlay plane updates with VRR;
- KMS commit and buffer-readiness deadlines;
Power Saving vs Color/Latency
- ABM (adaptive backlight management);
- PSR1 latencies;
- Power optimization vs color accuracy/latency requirements.
Content-Adaptive Scaling & Sharpening
- Content-Adaptive Scalers on display hardware;
- New drm_colorop for content adaptive scaling;
- Proprietary algorithms.
Display Mux
- Laptop muxes for switching of the embedded panel between the integrated GPU and the discrete GPU;
- Seamless/atomic hand-off between drivers on Linux desktops.
Real time scheduling & async KMS API
- Potential benefits: lower latency input feedback, better VRR handling, buffer synchronization, etc.
- Issues around async uAPI usage and async-call handling.
In-person, but also geographically-distributed event
This year Linux Display Next hackfest is a hybrid event, hosted onsite at the
Igalia offices and available for remote attendance. In-person participants will
find an environment for networking and brainstorming in our inspiring and
collaborative office space. Additionally, A Coru a itself is a gem waiting to
be explored, with stunning beaches, good food, and historical sites.

Semi-structured structure: how the 2024 Linux Display Next Hackfest will work
- Agenda: Participants proposed the topics and talks for discussing in
sessions.
- Interactive Sessions: Discussions, workshops, introductory talks and
brainstorming sessions lasting around 1h30. There is always a starting point
for discussions and new ideas will emerge in real time.
- Immersive experience: We will have coffee-breaks between sessions and
lunch time at the office for all in-person participants. Lunches and
coffee-breaks are sponsored by Igalia. This will keep us sharing knowledge and
in continuous interaction.
- Spaces for all group sizes: In-person participants will find different
room sizes that match various group sizes at Igalia HQ. Besides that, there
will be some devices for showcasing and real-time demonstrations.
Social Activities: building connections beyond the sessions
To make the most of your time in A Coru a, we ll be organizing some social activities:
- First-day Dinner: In-person participants will enjoy a Galician dinner on
Tuesday, after a first day of intensive discussions in the hackfest.
- Getting to know a little of A Coru a: Finding out a little about A Coru a
and current local habits.

- On Thursday afternoon, we will close the 2024 Linux Display Next hackfest
with a guided tour of the Museum of Galicia s favorite beer brand, Estrella
Galicia. The guided tour covers the eight sectors of the museum and ends with
beer pouring and tasting. After this experience, a transfer bus will take us to
the Maria Pita square.
- At Maria Pita square we will see the charm of some historical landmarks of
A Coru a, explore the casual and vibrant style of the city center and taste
local foods while chatting with friends.
Sponsorship
Igalia sponsors lunches and coffee-breaks on hackfest days, Tuesday s dinner,
and the social event on Thursday afternoon for in-person participants.
 We can t wait to welcome hackfest attendees to A Coru a! Stay tuned for further
details and outcomes of this unconventional and unique experience.
We can t wait to welcome hackfest attendees to A Coru a! Stay tuned for further
details and outcomes of this unconventional and unique experience.
- Content-Adaptive Scalers on display hardware;
- New drm_colorop for content adaptive scaling;
- Proprietary algorithms.
Display Mux
- Laptop muxes for switching of the embedded panel between the integrated GPU and the discrete GPU;
- Seamless/atomic hand-off between drivers on Linux desktops.
Real time scheduling & async KMS API
- Potential benefits: lower latency input feedback, better VRR handling, buffer synchronization, etc.
- Issues around async uAPI usage and async-call handling.
In-person, but also geographically-distributed event
This year Linux Display Next hackfest is a hybrid event, hosted onsite at the
Igalia offices and available for remote attendance. In-person participants will
find an environment for networking and brainstorming in our inspiring and
collaborative office space. Additionally, A Coru a itself is a gem waiting to
be explored, with stunning beaches, good food, and historical sites.

Semi-structured structure: how the 2024 Linux Display Next Hackfest will work
- Agenda: Participants proposed the topics and talks for discussing in
sessions.
- Interactive Sessions: Discussions, workshops, introductory talks and
brainstorming sessions lasting around 1h30. There is always a starting point
for discussions and new ideas will emerge in real time.
- Immersive experience: We will have coffee-breaks between sessions and
lunch time at the office for all in-person participants. Lunches and
coffee-breaks are sponsored by Igalia. This will keep us sharing knowledge and
in continuous interaction.
- Spaces for all group sizes: In-person participants will find different
room sizes that match various group sizes at Igalia HQ. Besides that, there
will be some devices for showcasing and real-time demonstrations.
Social Activities: building connections beyond the sessions
To make the most of your time in A Coru a, we ll be organizing some social activities:
- First-day Dinner: In-person participants will enjoy a Galician dinner on
Tuesday, after a first day of intensive discussions in the hackfest.
- Getting to know a little of A Coru a: Finding out a little about A Coru a
and current local habits.

- On Thursday afternoon, we will close the 2024 Linux Display Next hackfest
with a guided tour of the Museum of Galicia s favorite beer brand, Estrella
Galicia. The guided tour covers the eight sectors of the museum and ends with
beer pouring and tasting. After this experience, a transfer bus will take us to
the Maria Pita square.
- At Maria Pita square we will see the charm of some historical landmarks of
A Coru a, explore the casual and vibrant style of the city center and taste
local foods while chatting with friends.
Sponsorship
Igalia sponsors lunches and coffee-breaks on hackfest days, Tuesday s dinner,
and the social event on Thursday afternoon for in-person participants.
 We can t wait to welcome hackfest attendees to A Coru a! Stay tuned for further
details and outcomes of this unconventional and unique experience.
We can t wait to welcome hackfest attendees to A Coru a! Stay tuned for further
details and outcomes of this unconventional and unique experience.
- Potential benefits: lower latency input feedback, better VRR handling, buffer synchronization, etc.
- Issues around async uAPI usage and async-call handling.
In-person, but also geographically-distributed event
This year Linux Display Next hackfest is a hybrid event, hosted onsite at the
Igalia offices and available for remote attendance. In-person participants will
find an environment for networking and brainstorming in our inspiring and
collaborative office space. Additionally, A Coru a itself is a gem waiting to
be explored, with stunning beaches, good food, and historical sites.

Semi-structured structure: how the 2024 Linux Display Next Hackfest will work
- Agenda: Participants proposed the topics and talks for discussing in
sessions.
- Interactive Sessions: Discussions, workshops, introductory talks and
brainstorming sessions lasting around 1h30. There is always a starting point
for discussions and new ideas will emerge in real time.
- Immersive experience: We will have coffee-breaks between sessions and
lunch time at the office for all in-person participants. Lunches and
coffee-breaks are sponsored by Igalia. This will keep us sharing knowledge and
in continuous interaction.
- Spaces for all group sizes: In-person participants will find different
room sizes that match various group sizes at Igalia HQ. Besides that, there
will be some devices for showcasing and real-time demonstrations.
Social Activities: building connections beyond the sessions
To make the most of your time in A Coru a, we ll be organizing some social activities:
- First-day Dinner: In-person participants will enjoy a Galician dinner on
Tuesday, after a first day of intensive discussions in the hackfest.
- Getting to know a little of A Coru a: Finding out a little about A Coru a
and current local habits.

- On Thursday afternoon, we will close the 2024 Linux Display Next hackfest
with a guided tour of the Museum of Galicia s favorite beer brand, Estrella
Galicia. The guided tour covers the eight sectors of the museum and ends with
beer pouring and tasting. After this experience, a transfer bus will take us to
the Maria Pita square.
- At Maria Pita square we will see the charm of some historical landmarks of
A Coru a, explore the casual and vibrant style of the city center and taste
local foods while chatting with friends.
Sponsorship
Igalia sponsors lunches and coffee-breaks on hackfest days, Tuesday s dinner,
and the social event on Thursday afternoon for in-person participants.
 We can t wait to welcome hackfest attendees to A Coru a! Stay tuned for further
details and outcomes of this unconventional and unique experience.
We can t wait to welcome hackfest attendees to A Coru a! Stay tuned for further
details and outcomes of this unconventional and unique experience.
- Agenda: Participants proposed the topics and talks for discussing in sessions.
- Interactive Sessions: Discussions, workshops, introductory talks and brainstorming sessions lasting around 1h30. There is always a starting point for discussions and new ideas will emerge in real time.
- Immersive experience: We will have coffee-breaks between sessions and lunch time at the office for all in-person participants. Lunches and coffee-breaks are sponsored by Igalia. This will keep us sharing knowledge and in continuous interaction.
- Spaces for all group sizes: In-person participants will find different room sizes that match various group sizes at Igalia HQ. Besides that, there will be some devices for showcasing and real-time demonstrations.
Social Activities: building connections beyond the sessions
To make the most of your time in A Coru a, we ll be organizing some social activities:
- First-day Dinner: In-person participants will enjoy a Galician dinner on
Tuesday, after a first day of intensive discussions in the hackfest.
- Getting to know a little of A Coru a: Finding out a little about A Coru a
and current local habits.

- On Thursday afternoon, we will close the 2024 Linux Display Next hackfest
with a guided tour of the Museum of Galicia s favorite beer brand, Estrella
Galicia. The guided tour covers the eight sectors of the museum and ends with
beer pouring and tasting. After this experience, a transfer bus will take us to
the Maria Pita square.
- At Maria Pita square we will see the charm of some historical landmarks of
A Coru a, explore the casual and vibrant style of the city center and taste
local foods while chatting with friends.
Sponsorship
Igalia sponsors lunches and coffee-breaks on hackfest days, Tuesday s dinner,
and the social event on Thursday afternoon for in-person participants.
 We can t wait to welcome hackfest attendees to A Coru a! Stay tuned for further
details and outcomes of this unconventional and unique experience.
We can t wait to welcome hackfest attendees to A Coru a! Stay tuned for further
details and outcomes of this unconventional and unique experience.
 We can t wait to welcome hackfest attendees to A Coru a! Stay tuned for further
details and outcomes of this unconventional and unique experience.
We can t wait to welcome hackfest attendees to A Coru a! Stay tuned for further
details and outcomes of this unconventional and unique experience.
 The eleventh release of the
The eleventh release of the 
 Years ago, at what I think I remember was DebConf 15, I hacked for a while
on debhelper to
Years ago, at what I think I remember was DebConf 15, I hacked for a while
on debhelper to

 Like each month, have a look at the work funded by
Like each month, have a look at the work funded by 










 Getting the
Getting the 
 Debian is running a "
Debian is running a "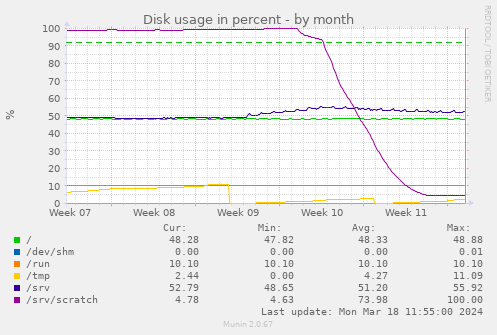 The initial dip from 100% to 95% is my first "what happens if we block repos
> 500 MB" attempt. Over the week after that, the git filter clones reduce the
overall disk consumption from almost 300 GB to 15 GB, a 1/20. Some
repos shrank from GBs to below a MB.
Perhaps I should make all my git clones use one of the filters.
The initial dip from 100% to 95% is my first "what happens if we block repos
> 500 MB" attempt. Over the week after that, the git filter clones reduce the
overall disk consumption from almost 300 GB to 15 GB, a 1/20. Some
repos shrank from GBs to below a MB.
Perhaps I should make all my git clones use one of the filters.
 Closing arguments in the trial between various people and
Closing arguments in the trial between various people and 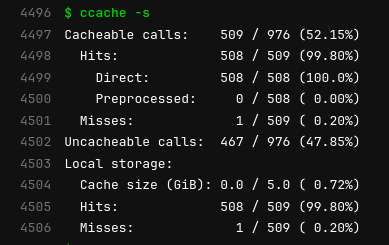 The image here comes from an example of building
The image here comes from an example of building 











