Russ Allbery: Review: Sweep of the Heart
| Series: | Innkeeper Chronicles #6 |
| Publisher: | NYLA Publishing |
| Copyright: | 2022 |
| ISBN: | 1-64197-239-4 |
| Format: | Kindle |
| Pages: | 440 |
| Series: | Innkeeper Chronicles #6 |
| Publisher: | NYLA Publishing |
| Copyright: | 2022 |
| ISBN: | 1-64197-239-4 |
| Format: | Kindle |
| Pages: | 440 |
 I have been a bearded subject since I was 18, back in 1994. Yes,
during 1999-2000, I shaved for my military service, and I briefly tried the
goatee look in 2008 Few people nowadays can imagine my face without
a forest of hair.
But sometimes, life happens. And, unlike my good friend
Bdale, I didn t get Linus to do the
honors But, all in all, here I am:
I have been a bearded subject since I was 18, back in 1994. Yes,
during 1999-2000, I shaved for my military service, and I briefly tried the
goatee look in 2008 Few people nowadays can imagine my face without
a forest of hair.
But sometimes, life happens. And, unlike my good friend
Bdale, I didn t get Linus to do the
honors But, all in all, here I am:
 Turns out, I have been suffering from quite bad skin infections for a
couple of years already. Last Friday, I checked in to the hospital,
with an ugly, swollen face (I won t put you through that), and the
hospital staff decided it was in my best interests to trim my
beard. And then some more. And then shave me. I sat in the hospital
for four days, getting soaked (medical term) with antibiotics and
otherstuff, got my recipes for the next few days, and well, I
really hope that s the end of the infections. We shall see!
So, this is the result of the loving and caring work of three
different nurses. Yes, not clean-shaven (I should not trim it
further, as shaving blades are a risk of reinfection).
Anyway I guess the bits of hair you see over the place will not
take too long to become a beard again, even get somewhat
respectable. But I thought some of you would like to see the real me
PS- Thanks to all who have reached out with good wishes. All is fine!
Turns out, I have been suffering from quite bad skin infections for a
couple of years already. Last Friday, I checked in to the hospital,
with an ugly, swollen face (I won t put you through that), and the
hospital staff decided it was in my best interests to trim my
beard. And then some more. And then shave me. I sat in the hospital
for four days, getting soaked (medical term) with antibiotics and
otherstuff, got my recipes for the next few days, and well, I
really hope that s the end of the infections. We shall see!
So, this is the result of the loving and caring work of three
different nurses. Yes, not clean-shaven (I should not trim it
further, as shaving blades are a risk of reinfection).
Anyway I guess the bits of hair you see over the place will not
take too long to become a beard again, even get somewhat
respectable. But I thought some of you would like to see the real me
PS- Thanks to all who have reached out with good wishes. All is fine!
 Mechanical keyboards the big fat rabbit hole you can disappear I started using mechanical keyboards about a year ago, with a Drevo Blademaster Pro (review coming up), but recently got a Pulsar PCML TKL keyboard in a build-it-yourself order.
Mechanical keyboards the big fat rabbit hole you can disappear I started using mechanical keyboards about a year ago, with a Drevo Blademaster Pro (review coming up), but recently got a Pulsar PCML TKL keyboard in a build-it-yourself order. The Drevo Blademaster Pro I am using is great, but doesn t allow changing switches at all. So I was contemplating getting a mechanical keyboard that allows for arbitrary switches. My biggest problem here is that I am used to the Japanese JIS layout which gives you a lot more keys which come in extremely handy in Emacs or when typing various languages. Fortunately, APlusX a Korean company manufactures a lot of gear under the Pulsar name, and supports also JIS layout. In addition, they have a great web site to customize your keyboard (layout, color, switch, keycaps) and send you a build-yourself kit for a very reasonable prize at least in Japan.
So I got my first keyboard to put together myself . how was I nervous getting all the stuff out! Despite being a DIY keyboard, it is very easy (and they offer also pre-assembly options, too!). You don t need to solder the PCB or similar, the steps are more or less: (i) put in the switches, and (ii) add the key caps. I started with the first, putting the switches (I went with Kailh Box Brown tactile ones) into the PCB board
The Drevo Blademaster Pro I am using is great, but doesn t allow changing switches at all. So I was contemplating getting a mechanical keyboard that allows for arbitrary switches. My biggest problem here is that I am used to the Japanese JIS layout which gives you a lot more keys which come in extremely handy in Emacs or when typing various languages. Fortunately, APlusX a Korean company manufactures a lot of gear under the Pulsar name, and supports also JIS layout. In addition, they have a great web site to customize your keyboard (layout, color, switch, keycaps) and send you a build-yourself kit for a very reasonable prize at least in Japan.
So I got my first keyboard to put together myself . how was I nervous getting all the stuff out! Despite being a DIY keyboard, it is very easy (and they offer also pre-assembly options, too!). You don t need to solder the PCB or similar, the steps are more or less: (i) put in the switches, and (ii) add the key caps. I started with the first, putting the switches (I went with Kailh Box Brown tactile ones) into the PCB board  Well, that was easy at least I thought until I started testing the keys and realized that about 20 of them didn t work!! Pulling out the switches again I saw that I twisted a pin on each of them. One by one I straightened the pins and reinserted them very carefully. Lesson learned! At the end all the switches were on the board and reacted to key presses.
Next step was adding the key caps. Again, those are not really special key caps, but simply style and sufficient for me. Of course I messed up 0 and O (which have different heights) and at first were confused about different arrow options etc, but since plugging in and pulling out key caps is very easy, at the end all the caps were in place.
Well, that was easy at least I thought until I started testing the keys and realized that about 20 of them didn t work!! Pulling out the switches again I saw that I twisted a pin on each of them. One by one I straightened the pins and reinserted them very carefully. Lesson learned! At the end all the switches were on the board and reacted to key presses.
Next step was adding the key caps. Again, those are not really special key caps, but simply style and sufficient for me. Of course I messed up 0 and O (which have different heights) and at first were confused about different arrow options etc, but since plugging in and pulling out key caps is very easy, at the end all the caps were in place. With the final keyboard assembled (see top photo), I connected it to my Linux system and started typing around. And first of all, the typing experience was nice. The Kailh Box Brown switches have a bit stronger actuation point then the switches I have in the Blademaster Pro (which are Cherry MX Brown ones), but above all the sound is a bit deeper and thumbier , which really gives a nice feeling.
The keyboard also allows changing the RGB lightening via the keyboard (color, pattern, speed, brightness etc). There is a configuration software for macros etc, unfortunately it only works on Windows (and I couldn t get it to work with Wine, either), a sour point One more negative point is that the LED backlight doesn t have a timeout, that is, it stays on all the time. The Drevo I have turns off after a configured number of seconds, and turns completely black something I really like and miss on the Pulsar.
Another difference to the Blademaster is connectivity: While the Blademaster offers cable, bluetooth, and wireless (with dongle), the Pulsar only offers cable (USB-C). Not a real deal-breaker for me, since I use it at my desktop and really don t need wireless/bluetooth capabilities, but still.
I have been using the Pulsar now for a few days without even touching the Drevo (besides comparing typing sounds and actuation points), and really like the Pulsar. I think it is hard to get a fully configurable and changeable mechanical keyboard for a similar prize.
There is one last thing that I really really miss an ergonomic mechanical keyboard. Of course there are some, like the ErgoDox EZ or the Kinesis Advantage 2, but they don t offer JIS layout (and are very expensive). Then there is the Truly Ergonomic CLEAVE keyboard, which is really great, but quite expensive. I guess I have to dive down the rabbit hole even more and make my own PCB and ergonomic keyboard!
With the final keyboard assembled (see top photo), I connected it to my Linux system and started typing around. And first of all, the typing experience was nice. The Kailh Box Brown switches have a bit stronger actuation point then the switches I have in the Blademaster Pro (which are Cherry MX Brown ones), but above all the sound is a bit deeper and thumbier , which really gives a nice feeling.
The keyboard also allows changing the RGB lightening via the keyboard (color, pattern, speed, brightness etc). There is a configuration software for macros etc, unfortunately it only works on Windows (and I couldn t get it to work with Wine, either), a sour point One more negative point is that the LED backlight doesn t have a timeout, that is, it stays on all the time. The Drevo I have turns off after a configured number of seconds, and turns completely black something I really like and miss on the Pulsar.
Another difference to the Blademaster is connectivity: While the Blademaster offers cable, bluetooth, and wireless (with dongle), the Pulsar only offers cable (USB-C). Not a real deal-breaker for me, since I use it at my desktop and really don t need wireless/bluetooth capabilities, but still.
I have been using the Pulsar now for a few days without even touching the Drevo (besides comparing typing sounds and actuation points), and really like the Pulsar. I think it is hard to get a fully configurable and changeable mechanical keyboard for a similar prize.
There is one last thing that I really really miss an ergonomic mechanical keyboard. Of course there are some, like the ErgoDox EZ or the Kinesis Advantage 2, but they don t offer JIS layout (and are very expensive). Then there is the Truly Ergonomic CLEAVE keyboard, which is really great, but quite expensive. I guess I have to dive down the rabbit hole even more and make my own PCB and ergonomic keyboard!

devices.yaml. It contains the
device list. The second file is classifier.yaml.
It defines a scope for each device. A scope is a set of keys and
values. It is used in templates and to look up data associated with a
device.
$ ./run-jerikan scope to1-p1.sk1.blade-group.net continent: apac environment: prod groups: - tor - tor-bgp - tor-bgp-compute host: to1-p1.sk1 location: sk1 member: '1' model: dell-s4048 os: cumulus pod: '1' shorthost: to1-p1
to1-p1.sk1.blade-group.net, the following subset of
classifier.yaml defines its scope:
matchers: - '^(([^.]*)\..*)\.blade-group\.net': environment: prod host: '\1' shorthost: '\2' - '\.(sk1)\.': location: '\1' continent: apac - '^to([12])-[as]?p(\d+)\.': member: '\1' pod: '\2' - '^to[12]-p\d+\.': groups: - tor - tor-bgp - tor-bgp-compute - '^to[12]-(p ap)\d+\.sk1\.': os: cumulus model: dell-s4048
searchpaths.py. It describes
which directories to search for a variable. A Python function provides
a list of paths to look up in data/ for a given scope. Here
is a simplified version:2
def searchpaths(scope): paths = [ "host/ scope[location] / scope[shorthost] ", "location/ scope[location] ", "os/ scope[os] - scope[model] ", "os/ scope[os] ", 'common' ] for idx in range(len(paths)): try: paths[idx] = paths[idx].format(scope=scope) except KeyError: paths[idx] = None return [path for path in paths if path]
to1-p1.sk1.blade-group.net is
looked up in the following paths:
$ ./run-jerikan scope to1-p1.sk1.blade-group.net [ ] Search paths: host/sk1/to1-p1 location/sk1 os/cumulus-dell-s4048 os/cumulus common
system for accounts, DNS, syslog servers, topology for ports, interfaces, IP addresses, subnets, bgp for BGP configurationbuild for templates and validation scriptsapps for application variablesto1-p1.sk1.blade-group.net in the bgp namespace, the following
YAML files are processed: host/sk1/to1-p1/bgp.yaml,
location/sk1/bgp.yaml, os/cumulus-dell-s4048/bgp.yaml,
os/cumulus/bgp.yaml, and common/bgp.yaml. The search stops at the
first match.
The schema.yaml file allows us to override this
behavior by asking to merge dictionaries and arrays across all
matching files. Here is an excerpt of this file for the topology
namespace:
system: users: merge: hash sampling: merge: hash ansible-vars: merge: hash netbox: merge: hash
~ :
# In data/os/junos/system.yaml netbox: manufacturer: Juniper model: "~ model upper " # In data/groups/tor-bgp-compute/system.yaml netbox: role: net_tor_gpu_switch
netbox in the system namespace for
to1-p2.ussfo03.blade-group.net yields the following result:
$ ./run-jerikan scope to1-p2.ussfo03.blade-group.net continent: us environment: prod groups: - tor - tor-bgp - tor-bgp-compute host: to1-p2.ussfo03 location: ussfo03 member: '1' model: qfx5110-48s os: junos pod: '2' shorthost: to1-p2 [ ] Search paths: [ ] groups/tor-bgp-compute [ ] os/junos common $ ./run-jerikan lookup to1-p2.ussfo03.blade-group.net system netbox manufacturer: Juniper model: QFX5110-48S role: net_tor_gpu_switch
# In groups/adm-gateway/topology.yaml interface-rescue: address: "~ lookup('topology', 'addresses').rescue " up: - "~ip route add default via lookup('topology', 'addresses').rescue ipaddr('first_usable') table rescue" - "~ip rule add from lookup('topology', 'addresses').rescue ipaddr('address') table rescue priority 10" # In groups/adm-gateway-sk1/topology.yaml interfaces: ens1f0: "~ lookup('topology', 'interface-rescue') "
$ ./run-jerikan lookup gateway1.sk1.blade-group.net topology interfaces [ ] ens1f0: address: 121.78.242.10/29 up: - ip route add default via 121.78.242.9 table rescue - ip rule add from 121.78.242.10 table rescue priority 10
peers: transit: cogent: asn: 174 remote: - 38.140.30.233 - 2001:550:2:B::1F9:1 specific-import: - name: ATT-US as-path: ".*7018$" lp-delta: 50 ix-sfmix: rs-sfmix: monitored: true asn: 63055 remote: - 206.197.187.253 - 206.197.187.254 - 2001:504:30::ba06:3055:1 - 2001:504:30::ba06:3055:2 blizzard: asn: 57976 remote: - 206.197.187.42 - 2001:504:30::ba05:7976:1 irr: AS-BLIZZARD
build namespace:
$ ./run-jerikan lookup edge1.ussfo03.blade-group.net build templates data.yaml: data.j2 config.txt: junos/main.j2 config-base.txt: junos/base.j2 config-irr.txt: junos/irr.j2 $ ./run-jerikan lookup to1-p1.ussfo03.blade-group.net build templates data.yaml: data.j2 config.txt: cumulus/main.j2 frr.conf: cumulus/frr.j2 interfaces.conf: cumulus/interfaces.j2 ports.conf: cumulus/ports.j2 dhcpd.conf: cumulus/dhcp.j2 default-isc-dhcp: cumulus/default-isc-dhcp.j2 authorized_keys: cumulus/authorized-keys.j2 motd: linux/motd.j2 acl.rules: cumulus/acl.j2 rsyslog.conf: cumulus/rsyslog.conf.j2
ipaddr. Here is an excerpt of
templates/junos/base.j2 to configure DNS
and NTP servers on Juniper devices:
system ntp % for ntp in lookup("system", "ntp") % server ntp ; % endfor % name-server % for dns in lookup("system", "dns") % dns ; % endfor %
% for dns in lookup('system', 'dns') % domain vrf VRF-MANAGEMENT name-server dns % endfor % ! % for syslog in lookup('system', 'syslog') % logging syslog vrf VRF-MANAGEMENT % endfor % !
devices() returns the list of devices matching a set of
conditions on the scope. For example, devices("location==ussfo03",
"groups==tor-bgp") returns the list of devices in San Francisco in
the tor-bgp group. You can also omit the operator if you want the
specified value to be equal to the one in the local scope. For
example, devices("location") returns devices in the current
location.lookup() does a key lookup. It takes the namespace, the key, and
optionally, a device name. If not provided, the current device
is assumed.scope() returns the scope of the provided device.% for neighbor in devices("location", "groups==edge") if neighbor != device % % for address in lookup("topology", "addresses", neighbor).loopback tolist % protocols bgp group IPV address ipv -EDGES-IBGP neighbor address description "IPv address ipv : iBGP to neighbor "; % endfor % % endfor %
store() as a filter:
interface Loopback0 description 'Loopback:' % for address in lookup('topology', 'addresses').loopback tolist % ipv address ipv address address store('addresses', 'Loopback0') ipaddr('cidr') % endfor % !
store():4
% for device, ip, interface in store('addresses') % % set interface = interface replace('/', '-') replace('.', '-') replace(':', '-') % % set name = ' . '.format(interface lower, device) % name . IN 'A' if ip ipv4 else 'AAAA' ip ipaddr('address') % endfor %
./run-jerikan build. The
--limit argument restricts the devices to generate configuration
files for. Build is not done in parallel because a template may depend
on the data collected by another template. Currently, it takes 1
minute to compile around 3000 files spanning over 800 devices.

templates/opengear/config.j2:15: in top-level template code config.interfaces. interface .netmask adddress ipaddr("netmask") continent = 'us' device = 'con1-ag2.ussfo03.blade-group.net' environment = 'prod' host = 'con1-ag2.ussfo03' infos = 'address': '172.30.24.19/21' interface = 'wan' location = 'ussfo03' loop = <LoopContext 1/2> member = '2' model = 'cm7132-2-dac' os = 'opengear' shorthost = 'con1-ag2' _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ value = JerkianUndefined, query = 'netmask', version = False, alias = 'ipaddr' [ ] # Check if value is a list and parse each element if isinstance(value, (list, tuple, types.GeneratorType)): _ret = [ipaddr(element, str(query), version) for element in value] return [item for item in _ret if item] > elif not value or value is True: E jinja2.exceptions.UndefinedError: 'dict object' has no attribute 'adddress'
jerikan/jinja.py. Mastering
Jinja2 is a good investment. Take time to browse through our
templates as some of them show interesting features.
checks/ directory. Jerikan looks up the key checks
in the build namespace to know which checks to run:
$ ./run-jerikan lookup edge1.ussfo03.blade-group.net build checks - description: Juniper configuration file syntax check script: checks/junoser cache: input: config.txt output: config-set.txt - description: check YAML data script: checks/data.yaml cache: data.yaml
checks/junoser is executed if there is a
change to the generated config.txt file. It also outputs a
transformed version of the configuration file which is easier to
understand when using diff. Junoser checks a Junos configuration
file using Juniper s XML schema definition for Netconf.5 On
error, Jerikan displays:
jerikan/build.py:127: RuntimeError -------------- Captured syntax check with Junoser call -------------- P: checks/junoser edge2.ussfo03.blade-group.net C: /app/jerikan O: E: Invalid syntax: set system syslog archive size 10m files 10 word-readable S: 1
.gitlab-ci.yml
file. When we need to make a change, we create a dedicated branch and
a merge request. GitLab compiles the templates using the same
environment we use on our laptops and store them as an artifact.


ob1-n1.sk1.blade-group.net ansible_host=172.29.15.12 ansible_user=blade ansible_connection=network_cli ansible_network_os=ios ob2-n1.sk1.blade-group.net ansible_host=172.29.15.13 ansible_user=blade ansible_connection=network_cli ansible_network_os=ios ob1-n1.ussfo03.blade-group.net ansible_host=172.29.15.12 ansible_user=blade ansible_connection=network_cli ansible_network_os=ios none ansible_connection=local [oob] ob1-n1.sk1.blade-group.net ob2-n1.sk1.blade-group.net ob1-n1.ussfo03.blade-group.net [os-ios] ob1-n1.sk1.blade-group.net ob2-n1.sk1.blade-group.net ob1-n1.ussfo03.blade-group.net [model-c2960s] ob1-n1.sk1.blade-group.net ob2-n1.sk1.blade-group.net ob1-n1.ussfo03.blade-group.net [location-sk1] ob1-n1.sk1.blade-group.net ob2-n1.sk1.blade-group.net [location-ussfo03] ob1-n1.ussfo03.blade-group.net [in-sync] ob1-n1.sk1.blade-group.net ob2-n1.sk1.blade-group.net ob1-n1.ussfo03.blade-group.net none
in-sync is a special group for devices which configuration should
match the golden configuration. Daily and unattended, Ansible should
be able to push configurations to this group. The mid-term goal is to
cover all devices.
none is a special device for tasks not related to a specific host.
This includes synchronizing NetBox, IRR objects, and the DNS,
updating the RPKI, and building the geofeed files.
ansible/playbooks/site.yaml file.
Here is a shortened version:
- hosts: adm-gateway:!done strategy: mitogen_linear roles: - blade.linux - blade.adm-gateway - done - hosts: os-linux:!done strategy: mitogen_linear roles: - blade.linux - done - hosts: os-junos:!done gather_facts: false roles: - blade.junos - done - hosts: os-opengear:!done gather_facts: false roles: - blade.opengear - done - hosts: none:!done gather_facts: false roles: - blade.none - done
blade.junos role. Once a play has been executed, the
device is added to the done group and the other plays are skipped.
The playbook can be executed with the configuration files generated by
the GitLab CI using the ./run-ansible-gitlab command. This is a
wrapper around Docker and the ansible-playbook command and it
accepts the same arguments. To deploy the configuration on the edge
devices for the SK1 datacenter in check mode, we use:
$ ./run-ansible-gitlab playbooks/site.yaml --limit='edge:&location-sk1' --diff --check [ ] PLAY RECAP ************************************************************* edge1.sk1.blade-group.net : ok=6 changed=0 unreachable=0 failed=0 skipped=3 rescued=0 ignored=0 edge2.sk1.blade-group.net : ok=5 changed=0 unreachable=0 failed=0 skipped=1 rescued=0 ignored=0
--check must detect if a change is needed;--diff must provide a visualization of the planned changes;--check and --diff must not display anything if there is nothing to change;cisco.iosxr collection. The quality of Ansible
Galaxy collections is quite random and it is an additional
maintenance burden. It seems better to write roles tailored to our
needs. The collections we use are in
ci/ansible/ansible-galaxy.yaml. We use
Mitogen to get a 10 speedup on Ansible executions on Linux
hosts.
We also have a few playbooks for operational purpose: upgrading the OS
version, isolate an edge router, etc. We were also planning on how to
add operational checks in roles: are all the BGP sessions up? They
could have been used to validate a deployment and rollback if there is
an issue.
Currently, our playbooks are run from our laptops. To keep tabs, we
are using ARA. A weekly dry-run on devices in the in-sync group
also provides a dashboard on which devices we need to run Ansible
on.

$ ansible --version ansible 2.10.8 [ ] $ cat test.j2 Hello name ! $ ansible all -i localhost, \ > --connection=local \ > -m template \ > -a "src=test.j2 dest=test.txt" localhost FAILED! => "changed": false, "msg": "AnsibleUndefinedVariable: 'name' is undefined"
jerikan/jinja.py. This is a remain of the
fact we do not maintain Jerikan as a standalone software.
store() filter and a
store() function. With Jinja2, filters and functions live in
two different namespaces.
ansible/roles/blade.linux/tasks/firewall.yaml
and
ansible/roles/blade.linux/tasks/interfaces.yaml.
They are meant to be called when needed, using import_role.
remotes/private/attic/novena 822ca2bb add letter i sent to novena, never published
remotes/private/attic/secureboot de09d82b quick review, add note and graph
remotes/private/attic/wireguard 5c5340d1 wireguard review, tutorial and comparison with alternatives
remotes/private/backlog/dat 914c5edf Merge branch 'master' into backlog/dat
remotes/private/backlog/packet 9b2c6d1a ham radio packet innovations and primer
remotes/private/backlog/performance-tweaks dcf02676 config notes for http2
remotes/private/backlog/serverless 9fce6484 postponed until kubecon europe
remotes/private/fin/cost-of-hosting 00d8e499 cost-of-hosting article online
remotes/private/fin/kubecon f4fd7df2 remove published or spun off articles
remotes/private/fin/kubecon-overview 21fae984 publish kubecon overview article
remotes/private/fin/kubecon2018 1edc5ec8 add series
remotes/private/fin/netconf 3f4b7ece publish the netconf articles
remotes/private/fin/netdev 6ee66559 publish articles from netdev 2.2
remotes/private/fin/pgp-offline f841deed pgp offline branch ready for publication
remotes/private/fin/primes c7e5b912 publish the ROCA paper
remotes/private/fin/runtimes 4bee1d70 prepare publication of runtimes articles
remotes/private/fin/token-benchmarks 5a363992 regenerate timestamp automatically
remotes/private/ideas/astropy 95d53152 astropy or python in astronomy
remotes/private/ideas/avaneya 20a6d149 crowdfunded blade-runner-themed GPLv3 simcity-like simulator
remotes/private/ideas/backups-benchmarks fe2f1f13 review of backup software through performance and features
remotes/private/ideas/cumin 7bed3945 review of the cumin automation tool from WM foundation
remotes/private/ideas/future-of-distros d086ca0d modern packaging problems and complex apps
remotes/private/ideas/on-dying a92ad23f another dying thing
remotes/private/ideas/openpgp-discovery 8f2782f0 openpgp discovery mechanisms (WKD, etc), thanks to jonas meurer
remotes/private/ideas/password-bench 451602c0 bruteforce estimates for various password patterns compared with RSA key sizes
remotes/private/ideas/prometheus-openmetrics 2568dbd6 openmetrics standardizing prom metrics enpoints
remotes/private/ideas/telling-time f3c24a53 another way of telling time
remotes/private/ideas/wallabako 4f44c5da talk about wallabako, read-it-later + kobo hacking
remotes/private/stalled/bench-bench-bench 8cef0504 benchmarking http benchmarking tools
remotes/private/stalled/debian-survey-democracy 909bdc98 free software surveys and debian democracy, volunteer vs paid work
novena: the project is ooold now, didn't seem to fit a LWN
article. it was basically "how can i build my novena now" and "you
guys rock!" it seems like the MNT Reform is the brain child of
the Novena now, and I dare say it's even cooler!secureboot: my LWN editors were critical of my approach, and
probably rightly so - it's a really complex subject and I was
probably out of my depth... it's also out of date now, we did
manage secureboot in Debianwireguard: LWN ended up writing extensive coverage, and
I was biased against Donenfeld because of conflicts in a previous
projectdat: I already had written Sharing and archiving data sets with
Dat, but
it seems I had more to say... mostly performance issues, beaker, no
streaming, limited adoption... to be investigated, I guess?packet: a primer on data communications over ham radio, and the
cool new tech that has emerged in the free software world. those
are mainly notes about Pat, Direwolf, APRS and so
on... just never got around to making sense of it or really using
the tech...performance-tweaks: "optimizing websites at the age of http2",
the unwritten story of the optimization of this website with HTTP/2
and friendsserverless: god. one of the leftover topics at Kubecon, my notes
on this were thin, and the actual subject, possibly even
thinner... the only lie worse than the cloud is that there's no
server at all! concretely, that's a pile of notes about
Kubecon which I wanted to sort
through. Probably belongs in the attic now.astropy: "Python in astronomy" - had a chat with saimn
while writing about sigal, and it
turns out he actually works on free software in astronomy, in
Python... I actually expect LWN to cover this sooner than
later, after Lee Phillips's introduction to SciPyavaneya: crowdfunded blade-runner-themed GPLv3 simcity-like
simulator, i just have that link so farbackups-benchmarks: review of backup software through performance
and features, possibly based on those benchmarks, maybe based
on this list from restic although they refused
casync. benchmark articles are hard though, especially when
you want to "cover them all"... I did write a silly Attic vs
Bup back when those programs existed (2014), in a related
note...ideas/cumin: review of the Cumin automation tool from
WikiMedia Foundation... I ended up using the tool at work and
writing service documentation for itideas/future-of-distros: modern packaging problems and complex
apps, starting from this discussion about the removal of
Dolibarr from Debian, a summary of the thread from liw,
and ideas from joeyh (now from the outside of Debian), then
debates over the power of FTP masters - ugh, glad I
didn't step in that rat's nestideas/on-dying: "what happens when a hacker dies?" rather grim
subject, but a more and more important one... joeyh has ideas
again, phk as well, then there's a protocol for dying
(really grim)... then there are site policies like GitHub,
Facebook, etc... more in the branch, but that one I can't help but
think about now that family has taken a bigger place in my life...ideas/openpgp-discovery: OpenPGP discovery mechanisms (WKD, etc),
suggested by Jonas Meurer (somewhere?), only links to
Mailveloppe, LEAP, WKD (or is it WKS?), another
standard, probably would need to talk about OpenPGP CA now
and how Debian and Tor manage their keyrings... pain in the back.ideas/password-bench: bruteforce estimates for various password
patterns compared with RSA key sizes, spinoff of my smartcard
article, in
the crypto-bench, look at this shiny graph, surely that
must mean an article, right?ideas/prometheus-openmetrics: "Evolving the Prometheus exposition
format into a standard", seems like this happenedideas/telling-time: telling time to users is hard. xclock vs
ttyclock, etc. maybe gameclock and undertime as well? syncing time
is hard, but it turns out showing it is non trivial as
well... basically turning this bug report into an article. for
some reason I linked to this meme, derived from this
meme, presumably a premonition of my stupid idea of writing
undertime TIMEZONES!ideas/wallabako: "talk about wallabako, read-it-later + kobo
hacking", that's it, not even a link to the project!stalled/bench-bench-bench benchmarking http benchmarking tools, a
horrible mess of links, copy-paste from terminals, and ideas about
benchmarking... some of this trickled out into this benchmarking
guide at Tor, but not much more than the list of toolsstalled/debian-survey-democracy: "free software surveys and
Debian democracy, volunteer vs paid work"... A long standing
concern of mine is that all Debian work is supposed to be
volunteer, and paying explicitly for work inside Debian has
traditionally been frowned upon, even leading to serious drama and
dissent (remember Dunc-Tank)? back when I was writing for LWN,
I was also doing paid work for Debian LTS. I also learned
that a lot (most?) Debian Developers were actually being paid by
their job to work on Debian. So I was confused by this apparent
contradiction, especially given how the LTS project has been mostly
accepted, while Dunc-Tank was not... See also this talk at Debconf
16. I had hopes that this study would show the "hunch"
people have offered (that most DDs are paid to work on Debian) but
it seems to show the reverse (only 36% of DDs, and 18% of all
respondents paid). So I am still confused and worried about the
sustainability of Debian.
| Publisher: | Red Wombat Tea Company |
| Copyright: | 2013 |
| ASIN: | B00G9GSEXO |
| Format: | Kindle |
| Pages: | 140 |
Sings-to-Trees had hair the color of sunlight and ashes, delicately pointed ears, and eyes the translucent green of new leaves. His shirt was off, he had the sort of tanned muscle acquired from years of healthy outdoor living, and you could have sharpened a sword on his cheekbones. He was saved from being a young maiden's fantasy unless she was a very peculiar young maiden by the fact that he was buried up to the shoulder in the unpleasant end of a heavily pregnant unicorn.Sings-to-Trees is the sort of elf who lives by himself, has a healthy appreciation for what nursing wild animals involves, and does it anyway because he truly loves animals. Despite that, he was not entirely prepared to deal with a skeleton deer with a broken limb, or at least with the implications of injured skeleton deer who are attracted by magical disturbances showing up in his yard. As one might expect, Sings-to-Trees and the goblins run into each other while having to sort out some problems that are even more dangerous than the war the goblins were unexpectedly removed from. But the point of this novella is not a deep or complex plot. It pushes together a bunch of delightfully weird and occasionally grumpy characters, throws a challenge at them, and gives them space to act like fundamentally decent people working within their constraints and preconceptions. It is, in other words, an excellent vehicle for Ursula Vernon (writing as T. Kingfisher) to describe exasperated good-heartedness and stubbornly determined decency.
Sings-to-Trees gazed off in the middle distance with a vague, pleasant expression, the way that most people do when present at other people's minor domestic disputes, and after a moment, the stag had stopped rattling, and the doe had turned back and rested her chin trustingly on Sings-to-Trees' shoulder. This would have been a touching gesture, if her chin hadn't been made of painfully pointy blades of bone. It was like being snuggled by an affectionate plow.It's not a book you read for the twists and revelations (the resolution is a bit of an anti-climax). It's strength is in the side moments of characterization, in the author's light-hearted style, and in descriptions like the above. Sings-to-Trees is among my favorite characters in all of Vernon's books, surpassed only by gnoles and a few characters in Digger. The Kingfisher books I've read recently have involved humans and magic and romance and more standard fantasy plots. This book is from seven years ago and reminds me more of Digger. There is less expected plot machinery, more random asides, more narrator presence, inhuman characters, no romance, and a lot more focus on characters deciding moment to moment how to tackle the problem directly in front of them. I wouldn't call it a children's book (all of the characters are adults), but it has a bit of that simplicity and descriptive focus. If you like Kingfisher in descriptive mode, or enjoy Vernon's descriptions of D&D campaigns on Twitter, you are probably going to like this. If you don't, you may not. I thought it was slight but perfect for my mood at the time. Rating: 7 out of 10
rr.ntt.net or whois.radb.net can be a bottleneck. Updating many
filters may take several tens of minutes, depending on the load:
$ time bgpq4 -h whois.radb.net AS-HURRICANE wc -l 909869 1.96s user 0.15s system 2% cpu 1:17.64 total $ time bgpq4 -h rr.ntt.net AS-HURRICANE wc -l 927865 1.86s user 0.08s system 12% cpu 14.098 total
$ git clone https://github.com/vincentbernat/irrd-legacy.git -b blade/master $ cd irrd-legacy $ docker build . -t irrd-snapshot:latest [ ] Successfully built 58c3e83a1d18 Successfully tagged irrd-snapshot:latest $ docker container run --rm --detach --publish=43:43 irrd-snapshot 4879cfe7413075a0c217089dcac91ed356424c6b88808d8fcb01dc00eafcc8c7 $ time bgpq4 -h localhost AS-HURRICANE wc -l 904137 1.72s user 0.11s system 96% cpu 1.881 total
rr.ntt.net:
NTTCOM, RADB, RIPE, ALTDB, BELL, LEVEL3, RGNET, APNIC, JPIRR, ARIN,
BBOI, TC, AFRINIC, ARIN-WHOIS, and REGISTROBR. However, it misses
RPKI.2 Feel free to adapt!
The image can be scheduled to be rebuilt daily or weekly, depending on
your needs. The repository includes a .gitlab-ci.yaml
file automating the build and triggering the compilation
of all filters by your CI/CD upon success.
rpki-client and
transformed into RPSL objects to be imported in IRRd.
whois and
bgpq4. The first one allows you to do a query with the WHOIS
protocol:
$ whois -BrG 2a0a:e805:400::/40 [ ] inet6num: 2a0a:e805:400::/40 netname: FR-BLADE-CUSTOMERS-DE country: DE geoloc: 50.1109 8.6821 admin-c: BN2763-RIPE tech-c: BN2763-RIPE status: ASSIGNED mnt-by: fr-blade-1-mnt remarks: synced with cmdb created: 2020-05-19T08:04:58Z last-modified: 2020-05-19T08:04:58Z source: RIPE route6: 2a0a:e805:400::/40 descr: Blade IPv6 - AMS1 origin: AS64476 mnt-by: fr-blade-1-mnt remarks: synced with cmdb created: 2019-10-01T08:19:34Z last-modified: 2020-05-19T08:05:00Z source: RIPE
$ bgpq4 -6 -S RIPE -b AS64476 NN = [ 2a0a:e805::/40, 2a0a:e805:100::/40, 2a0a:e805:300::/40, 2a0a:e805:400::/40, 2a0a:e805:500::/40 ];
Notice I recommend that you read Writing a custom Ansible module as an introduction, as well as Syncing MySQL tables for a more instructive example.
- name: prepare RIPE objects irr_sync: irr: RIPE mntner: fr-blade-1-mnt source: whois-ripe.txt register: irr
- name: sign RIPE objects shell: cmd: gpg --batch --user noc@example.com --clearsign stdin: " irr.objects " register: signed check_mode: false changed_when: false - name: update RIPE objects by email mail: subject: "NEW: update for RIPE" from: noc@example.com to: "auto-dbm@ripe.net" cc: noc@example.com host: smtp.example.com port: 25 charset: us-ascii body: " signed.stdout "
key-cert object and adding it as a valid authentication
method for the corresponding mntner object:
key-cert: PGPKEY-A791AAAB certif: -----BEGIN PGP PUBLIC KEY BLOCK----- certif: certif: mQGNBF8TLY8BDADEwP3a6/vRhEERBIaPUAFnr23zKCNt5YhWRZyt50mKq1RmQBBY [ ] certif: -----END PGP PUBLIC KEY BLOCK----- mnt-by: fr-blade-1-mnt source: RIPE mntner: fr-blade-1-mnt [ ] auth: PGPKEY-A791AAAB mnt-by: fr-blade-1-mnt source: RIPE
module_args = dict( irr=dict(type='str', required=True), mntner=dict(type='str', required=True), source=dict(type='path', required=True), ) result = dict( changed=False, ) module = AnsibleModule( argument_spec=module_args, supports_check_mode=True )
whois command to retrieve all
the objects from the provided maintainer.
# Per-IRR variations: # - whois server whois = 'ARIN': 'rr.arin.net', 'RIPE': 'whois.ripe.net', 'APNIC': 'whois.apnic.net' # - whois options options = 'ARIN': ['-r'], 'RIPE': ['-BrG'], 'APNIC': ['-BrG'] # - objects excluded from synchronization excluded = ["domain"] if irr == "ARIN": # ARIN does not return these objects excluded.extend([ "key-cert", "mntner", ]) # Grab existing objects args = ["-h", whois[irr], "-s", irr, *options[irr], "-i", "mnt-by", module.params['mntner']] proc = subprocess.run("whois", *args, capture_output=True) if proc.returncode != 0: raise AnsibleError( f"unable to query whois: args ") output = proc.stdout.decode('ascii') got = extract(output, excluded)
whois command and the
objects to exclude from synchronization. The second part invokes the
whois command, requesting all objects whose mnt-by field is the
provided maintainer. Here is an example of output:
$ whois -h whois.ripe.net -s RIPE -BrG -i mnt-by fr-blade-1-mnt [ ] inet6num: 2a0a:e805:300::/40 netname: FR-BLADE-CUSTOMERS-FR country: FR geoloc: 48.8566 2.3522 admin-c: BN2763-RIPE tech-c: BN2763-RIPE status: ASSIGNED mnt-by: fr-blade-1-mnt remarks: synced with cmdb created: 2020-05-19T08:04:59Z last-modified: 2020-05-19T08:04:59Z source: RIPE [ ] route6: 2a0a:e805:300::/40 descr: Blade IPv6 - PA1 origin: AS64476 mnt-by: fr-blade-1-mnt remarks: synced with cmdb created: 2019-10-01T08:19:34Z last-modified: 2020-05-19T08:05:00Z source: RIPE [ ]
extract() function. It parses and
normalizes the results into a dictionary mapping object names to
objects. We store the result in the got variable.
def extract(raw, excluded): """Extract objects.""" # First step, remove comments and unwanted lines objects = "\n".join([obj for obj in raw.split("\n") if not obj.startswith(( "#", "%", ))]) # Second step, split objects objects = [RPSLObject(obj.strip()) for obj in re.split(r"\n\n+", objects) if obj.strip() and not obj.startswith( tuple(f" x :" for x in excluded))] # Last step, put objects in a dict objects = repr(obj): obj for obj in objects return objects
RPSLObject() is a class enabling normalization and comparison of
objects. Look at the module code for more details.
>>> output=""" ... inet6num: 2a0a:e805:300::/40 ... [ ] ... """ >>> pprint( k: str(v) for k,v in extract(output, excluded=[]) ) '<Object:inet6num:2a0a:e805:300::/40>': 'inet6num: 2a0a:e805:300::/40\n' 'netname: FR-BLADE-CUSTOMERS-FR\n' 'country: FR\n' 'geoloc: 48.8566 2.3522\n' 'admin-c: BN2763-RIPE\n' 'tech-c: BN2763-RIPE\n' 'status: ASSIGNED\n' 'mnt-by: fr-blade-1-mnt\n' 'remarks: synced with cmdb\n' 'source: RIPE', '<Object:route6:2a0a:e805:300::/40>': 'route6: 2a0a:e805:300::/40\n' 'descr: Blade IPv6 - PA1\n' 'origin: AS64476\n' 'mnt-by: fr-blade-1-mnt\n' 'remarks: synced with cmdb\n' 'source: RIPE'
wanted dictionary using the same structure, thanks
to the extract() function we can use verbatim:
with open(module.params['source']) as f: source = f.read() wanted = extract(source, excluded)
got and wanted to build the diff
object:
if got != wanted: result['changed'] = True if module._diff: result['diff'] = [ dict(before_header=k, after_header=k, before=str(got.get(k, "")), after=str(wanted.get(k, ""))) for k in set((*wanted.keys(), *got.keys())) if k not in wanted or k not in got or wanted[k] != got[k]]
source variable) and let
the IRR ignore unmodified objects. We also append the objects to be
deleted by adding a delete: attribute to each them them.
# We send all source objects and deleted objects. deleted_mark = f" 'delete:':16 deleted by CMDB" deleted = "\n\n".join([f" got[k].raw \n deleted_mark " for k in got if k not in wanted]) result['objects'] = f" source \n\n deleted " module.exit_json(**result)
--diff and --check flags. It does not return
anything if no change is detected. It can work with APNIC, RIPE and
ARIN. It is not perfect: it may not detect some changes,3 it
is not able to modify objects not owned by the provided
maintainer4 and some attributes cannot be modified, requiring
to manually delete and recreate the updated object.5 However,
this module should automate 95% of your needs.
key-cert and mntner objects
and therefore we cannot detect changes in them. It is also not
possible to detect changes to the auth mechanisms of a mntner
object.
inetnum object requires
deleting and recreating the object.

](http://jmtd.net/log/coil/400x-coil.jpg) Peter Christopherson and Jhonn Balance, from Santa Sangre
Peter Christopherson and Jhonn Balance, from Santa Sangre
 At Collabora one of the
many things we do is build Debian
derivatives/overlays for customers on a variety of architectures
including 32 bit and 64 bit ARM systems. And just as Debian does,
our OBS system builds on
native systems rather than emulators.
Luckily with the advent of ARM server systems some years ago
building natively for those systems has been a lot less painful
than it used to be. For 32 bit ARM we've been relying on Calxeda blade servers,
however Calxeda unfortunately tanked ages ago and the hardware is
starting to show its age (though luckily Debian Stretch does
support it properly, so at least the software is still fresh).
On the 64 bit ARM side, we're running on Gigabyte MP30-AR1 based
servers which can run 32 bit arm code (As opposed to e.g. ThunderX
based servers which can only run 64 bit code). As such running
armhf VMs on them to act as build slaves seems a good choice, but
setting that up is a bit more involved than it might appear.
The first pitfall is that there is no standard bootloader or
boot firmware available in Debian to boot on the "virt" machine
emulated by qemu (I didn't want to use an emulation of a real
machine). That also means there is nothing to pick the kernel
inside the guest at boot nor something which can e.g. have the
guest network boot, which means direct kernel booting needs to be
used.
The second pitfall was that the current Debian Stretch armhf
kernel isn't built with support for the generic PCI host controller
which the qemu virtual machine exposes, which means no storage and
no network shows up in the guest. Hopefully that will get solved
soonish (Debian
bug 864726) and can be in a Stretch update, until then a custom
kernel package is required using the patch attach to the bug report
is required but I won't go into that any further in this post.
So on the happy assumption that we have a kernel that works, the
challenge left is to nicely manage direct kernel loading. Or more
specifically, how ensure the hosts boots the kernel the guest has
installed via the standard apt tools without having to copy kernels
around between guest/host, which essentially comes down to exposing
/boot from the guest to the host. The solution we picked is to use
qemu's 9pfs support to share a folder from the host and use that as
/boot of the guest. For the 9p folder the "mapped" security mode
seems needed as the "none" mode seems to get confused by dpkg
(Debian
bug 864718).
As we're using libvirt as our virtual machine manager the
remainder of how to glue it all together will be mostly specific to
that.
First step is to install the system, mostly as normal. One can
directly boot into the vmlinuz and initrd.gz provided by normal
Stretch armhf netboot installer (downloaded into e.g /tmp). The
setup overall is straight-forward with a few small tweaks:
At Collabora one of the
many things we do is build Debian
derivatives/overlays for customers on a variety of architectures
including 32 bit and 64 bit ARM systems. And just as Debian does,
our OBS system builds on
native systems rather than emulators.
Luckily with the advent of ARM server systems some years ago
building natively for those systems has been a lot less painful
than it used to be. For 32 bit ARM we've been relying on Calxeda blade servers,
however Calxeda unfortunately tanked ages ago and the hardware is
starting to show its age (though luckily Debian Stretch does
support it properly, so at least the software is still fresh).
On the 64 bit ARM side, we're running on Gigabyte MP30-AR1 based
servers which can run 32 bit arm code (As opposed to e.g. ThunderX
based servers which can only run 64 bit code). As such running
armhf VMs on them to act as build slaves seems a good choice, but
setting that up is a bit more involved than it might appear.
The first pitfall is that there is no standard bootloader or
boot firmware available in Debian to boot on the "virt" machine
emulated by qemu (I didn't want to use an emulation of a real
machine). That also means there is nothing to pick the kernel
inside the guest at boot nor something which can e.g. have the
guest network boot, which means direct kernel booting needs to be
used.
The second pitfall was that the current Debian Stretch armhf
kernel isn't built with support for the generic PCI host controller
which the qemu virtual machine exposes, which means no storage and
no network shows up in the guest. Hopefully that will get solved
soonish (Debian
bug 864726) and can be in a Stretch update, until then a custom
kernel package is required using the patch attach to the bug report
is required but I won't go into that any further in this post.
So on the happy assumption that we have a kernel that works, the
challenge left is to nicely manage direct kernel loading. Or more
specifically, how ensure the hosts boots the kernel the guest has
installed via the standard apt tools without having to copy kernels
around between guest/host, which essentially comes down to exposing
/boot from the guest to the host. The solution we picked is to use
qemu's 9pfs support to share a folder from the host and use that as
/boot of the guest. For the 9p folder the "mapped" security mode
seems needed as the "none" mode seems to get confused by dpkg
(Debian
bug 864718).
As we're using libvirt as our virtual machine manager the
remainder of how to glue it all together will be mostly specific to
that.
First step is to install the system, mostly as normal. One can
directly boot into the vmlinuz and initrd.gz provided by normal
Stretch armhf netboot installer (downloaded into e.g /tmp). The
setup overall is straight-forward with a few small tweaks:
virt-install --name armhf-vm --arch armv7l --memory 512 \
--disk /srv/armhf-vm.img,bus=virtio
--filesystem /srv/armhf-vm-boot,virtio-boot,mode=mapped \
--boot=kernel=/tmp/vmlinuz,initrd=/tmp/initrd.gz,kernel_args="console=ttyAMA0,root=/dev/vda1"
virtio-boot /boot 9p trans=virtio,version=9p2000.L,x-systemd.automount 0 0
vm=$1
action=$2
bootdir=/srv/$ vm -boot
if [ $ action != "prepare" ] ; then
exit 0
fi
if [ ! -d $ bootdir ] ; then
exit 0
fi
ln -sf $(basename $(cat $ bootdir /vmlinuz)) $ bootdir /virtio-vmlinuz
ln -sf $(basename $(cat $ bootdir /initrd.img)) $ bootdir /virtio-initrd.img

 The above picture is the blend of the two communities from foss community and mozilla India. And unless you were there you wouldn t know who is from which community which is what FOSS is all about. But as always I m getting a bit ahead of myself.
Akshat, who works at NCRA as a programmer, the standing guy on the left shared with me in January this year that this year too, we should have two stalls, foss community and mozilla India stalls next to each other. While we had the banners, we were missing stickers and flyers. Funds were and are always an issue and this year too, it would have been emptier if we didn t get some money saved from last year minidebconf 2016 that we had in Mumbai. Our major expenses included printing stickers, stationery and flyers which came to around INR 5000/- and couple of LCD TV monitors which came for around INR 2k/- as rent. All the labour was voluntary in nature, but both me and Akshat easily spending upto 100 hours before the event. Next year, we want to raise to around INR 10-15k so we can buy 1 or 2 LCD monitors and we don t have to think for funds for next couple of years. How will we do that I have no idea atm.
The above picture is the blend of the two communities from foss community and mozilla India. And unless you were there you wouldn t know who is from which community which is what FOSS is all about. But as always I m getting a bit ahead of myself.
Akshat, who works at NCRA as a programmer, the standing guy on the left shared with me in January this year that this year too, we should have two stalls, foss community and mozilla India stalls next to each other. While we had the banners, we were missing stickers and flyers. Funds were and are always an issue and this year too, it would have been emptier if we didn t get some money saved from last year minidebconf 2016 that we had in Mumbai. Our major expenses included printing stickers, stationery and flyers which came to around INR 5000/- and couple of LCD TV monitors which came for around INR 2k/- as rent. All the labour was voluntary in nature, but both me and Akshat easily spending upto 100 hours before the event. Next year, we want to raise to around INR 10-15k so we can buy 1 or 2 LCD monitors and we don t have to think for funds for next couple of years. How will we do that I have no idea atm.
 Me and Akshat did all the printing and stationery runs and hence had not been using my lappy for about 3-4 days.
Come to the evening before the event and the laptop would not start. Coincidentally, or not few months or even last at last year s Debconf people had commented on IBM/Lenovo s obsession with proprietary power cords and adaptors. I hadn t given it much thought but when I got no power even after putting it on AC power for 3-4 hours, I looked up on the web and saw that the power cord and power adaptors were all different even in T440 and even that under existing models. In fact I couldn t find mine hence sharing it via pictures below.
Me and Akshat did all the printing and stationery runs and hence had not been using my lappy for about 3-4 days.
Come to the evening before the event and the laptop would not start. Coincidentally, or not few months or even last at last year s Debconf people had commented on IBM/Lenovo s obsession with proprietary power cords and adaptors. I hadn t given it much thought but when I got no power even after putting it on AC power for 3-4 hours, I looked up on the web and saw that the power cord and power adaptors were all different even in T440 and even that under existing models. In fact I couldn t find mine hence sharing it via pictures below.

 I knew/suspected that thinkpads would be rare where I was going, it would be rarer still to find the exact power cord and I was unsure whether it was the power cord at fault or adaptor or whatever goes for SMPS in laptop or memory or motherboard/CPU itself. I did look up the documentation at support.lenovo.com and was surprised at the extensive documentation that Lenovo has for remote troubleshooting.
I did the usual take out the battery, put it back in, twiddle with the little hole in the bottom of the laptop, trying to switch on without the battery on AC mains, trying to switch on with battery power only but nothing worked. Couple of hours had gone by and with a resigned thought went to bed, convincing myself that anyways it s good I am not taking the lappy as it is extra-dusty there and who needs a dead laptop anyways.
Update After the event was over, I did contact Lenovo support and within a week, with one visit from a service engineer, he was able to identify that it was a faulty cable which was at fault and not the the other things which I was afraid of. Another week gone by and lenovo replaced the cable. Going by service standards that I have seen of other companies, Lenovo deserves a gold star here for the prompt service they provided. I probably would end up subscribing to their extended 2-year warranty service when my existing 3 year warranty is about to be over.
Next day, woke up early morning, two students from COEP hostel were volunteering and we made our way to NCRA, Pune University Campus. Ironically, though we were under the impression that we would be the late arrivals, it turned out we were the early birds. 5-10 minutes passed by and soon enough we were joined by Aniket and we played catch-up for a while. We hadn t met each other for a while so it was good to catch-up. Then slowly other people starting coming in and around 07:10-07:15 we started for GMRT, Khodad.
Now I had been curious as had been hearing for years that the Pune-Nashik NH-50 highway would be concreted and widened to six-lane highways but the experience was below par. Came back and realized the proposal has now been pushed back to 2020.
From the mozilla team, only Aniket was with us, the rest of the group was coming straight from Nashik. Interestingly, all the six people who came, came on bikes which depending upon how you look at it was either brave or stupid. Travelling on bikes on Indian highways you either have to be brave or stupid or both, we have more than enough accidents due to quality of road construction, road design, lane-changing drivers and many other issues. This is probably not the place for it hence will use some other blog post to rant about that.
We reached around 10:00 hrs. IST and hung around till lunch as Akshat had all the marketing material, monitors etc. The only thing we had were couple of lappies and couple of SBC s, an RPI 3 and a BBB.
I knew/suspected that thinkpads would be rare where I was going, it would be rarer still to find the exact power cord and I was unsure whether it was the power cord at fault or adaptor or whatever goes for SMPS in laptop or memory or motherboard/CPU itself. I did look up the documentation at support.lenovo.com and was surprised at the extensive documentation that Lenovo has for remote troubleshooting.
I did the usual take out the battery, put it back in, twiddle with the little hole in the bottom of the laptop, trying to switch on without the battery on AC mains, trying to switch on with battery power only but nothing worked. Couple of hours had gone by and with a resigned thought went to bed, convincing myself that anyways it s good I am not taking the lappy as it is extra-dusty there and who needs a dead laptop anyways.
Update After the event was over, I did contact Lenovo support and within a week, with one visit from a service engineer, he was able to identify that it was a faulty cable which was at fault and not the the other things which I was afraid of. Another week gone by and lenovo replaced the cable. Going by service standards that I have seen of other companies, Lenovo deserves a gold star here for the prompt service they provided. I probably would end up subscribing to their extended 2-year warranty service when my existing 3 year warranty is about to be over.
Next day, woke up early morning, two students from COEP hostel were volunteering and we made our way to NCRA, Pune University Campus. Ironically, though we were under the impression that we would be the late arrivals, it turned out we were the early birds. 5-10 minutes passed by and soon enough we were joined by Aniket and we played catch-up for a while. We hadn t met each other for a while so it was good to catch-up. Then slowly other people starting coming in and around 07:10-07:15 we started for GMRT, Khodad.
Now I had been curious as had been hearing for years that the Pune-Nashik NH-50 highway would be concreted and widened to six-lane highways but the experience was below par. Came back and realized the proposal has now been pushed back to 2020.
From the mozilla team, only Aniket was with us, the rest of the group was coming straight from Nashik. Interestingly, all the six people who came, came on bikes which depending upon how you look at it was either brave or stupid. Travelling on bikes on Indian highways you either have to be brave or stupid or both, we have more than enough accidents due to quality of road construction, road design, lane-changing drivers and many other issues. This is probably not the place for it hence will use some other blog post to rant about that.
We reached around 10:00 hrs. IST and hung around till lunch as Akshat had all the marketing material, monitors etc. The only thing we had were couple of lappies and couple of SBC s, an RPI 3 and a BBB.
 Our find for the event was Aarti Kashyap who you can see above. She is a third-year student at COEP and one of the rare people who chose to interact with hardware rather than software. From last several years, we had been trying, successfully and unsuccessfully to get more Indian women and girls interested into technology. It is a vicious circle as till a girl/woman doesn t volunteer we are unable to share our knowledge to the extent we can which leads them to not have much interest in FOSS or even technology in general.
While there are groups are djangogirls, Pyladies and railgirls and even Outreachy which tries to motivate getting girls into computing but it s a long road ahead.
We are short of both funds and ideas as to how to motivate more girls to get into computing and then to get into playing with hardware. I don t know where to start and end for whoever wants to play with hardware. From SBC s, routers to blade servers the sky is the limit. Again this probably isn t the place for it, hence probably we can chew it on more at some other blog post.
This year, we had a lowish turnout due to the fact that the 12th board exams 1st paper was on the day we had opened. So instead of 20-25k, we probably had 5-7k fewer people pass through. There were two-three things that we were showing, we were showing Debian on one of the systems, we were showing the output from the SBC s on the other monitor but the glare kept hitting the monitors.
While the organizers had done exemplary work over last year. They had taped the carpets on the ground so there was hardly any dust moving around. However, I wished the organizers had taken the pains to have two cloth roofs over our head instead of just one, the other roof head could be say 2 feet up, this would have done two things
a. It probably would have cooled the place a bit more as
b. We could get diffused sunlight which would have lessened the glare and reflection the LCD s kept throwing back. At times we also got people to come to our side as can be seen in Aarti s photo as can be seen above.
If these improvements can be made for next year, this would result in everybody in our Pandal would benefit, not just us and mozilla. This would be benefiting around 10-15 organizations which were within the same temporary structure.
Of course, it depends very much on the budget they are able to have and people who are executing, we can just advise.
The other thing which had been missing last year and this year is writing about Single Board Computers in Marathi. If we are to promote them as something to replace a computer or something for a younger brother/sister to learn computing upon at a lower cost, we need leaflets written in their language to be more effective. And this needs to be in the language and mannerisms that people in that region understand. India, as probably people might have experienced is a dialect-prone country. Which means every 2-5 kms, the way the language is spoken is different from anywhere else. The Marathi spoken by somebody who has lived in Ravivar Peth for his whole life and a person who has lived in say Kothrud are different. The same goes from any place and this place, Khodad, Narayangaon would have its own dialect, its own mini-codespeak.
Just to share, we did have one in English but it would have been a vast improvement if we could do it in the local language. Maybe we can discuss about this and ask for help from people.
Outside, Looking in
Our find for the event was Aarti Kashyap who you can see above. She is a third-year student at COEP and one of the rare people who chose to interact with hardware rather than software. From last several years, we had been trying, successfully and unsuccessfully to get more Indian women and girls interested into technology. It is a vicious circle as till a girl/woman doesn t volunteer we are unable to share our knowledge to the extent we can which leads them to not have much interest in FOSS or even technology in general.
While there are groups are djangogirls, Pyladies and railgirls and even Outreachy which tries to motivate getting girls into computing but it s a long road ahead.
We are short of both funds and ideas as to how to motivate more girls to get into computing and then to get into playing with hardware. I don t know where to start and end for whoever wants to play with hardware. From SBC s, routers to blade servers the sky is the limit. Again this probably isn t the place for it, hence probably we can chew it on more at some other blog post.
This year, we had a lowish turnout due to the fact that the 12th board exams 1st paper was on the day we had opened. So instead of 20-25k, we probably had 5-7k fewer people pass through. There were two-three things that we were showing, we were showing Debian on one of the systems, we were showing the output from the SBC s on the other monitor but the glare kept hitting the monitors.
While the organizers had done exemplary work over last year. They had taped the carpets on the ground so there was hardly any dust moving around. However, I wished the organizers had taken the pains to have two cloth roofs over our head instead of just one, the other roof head could be say 2 feet up, this would have done two things
a. It probably would have cooled the place a bit more as
b. We could get diffused sunlight which would have lessened the glare and reflection the LCD s kept throwing back. At times we also got people to come to our side as can be seen in Aarti s photo as can be seen above.
If these improvements can be made for next year, this would result in everybody in our Pandal would benefit, not just us and mozilla. This would be benefiting around 10-15 organizations which were within the same temporary structure.
Of course, it depends very much on the budget they are able to have and people who are executing, we can just advise.
The other thing which had been missing last year and this year is writing about Single Board Computers in Marathi. If we are to promote them as something to replace a computer or something for a younger brother/sister to learn computing upon at a lower cost, we need leaflets written in their language to be more effective. And this needs to be in the language and mannerisms that people in that region understand. India, as probably people might have experienced is a dialect-prone country. Which means every 2-5 kms, the way the language is spoken is different from anywhere else. The Marathi spoken by somebody who has lived in Ravivar Peth for his whole life and a person who has lived in say Kothrud are different. The same goes from any place and this place, Khodad, Narayangaon would have its own dialect, its own mini-codespeak.
Just to share, we did have one in English but it would have been a vast improvement if we could do it in the local language. Maybe we can discuss about this and ask for help from people.
Outside, Looking in
 What had been interesting about the whole journey were the new people who were bringing all their passion and creativity to the fore. From the mozilla community, we had Akshay who is supposed to be a wizard on graphics, animation, editing anything to do with the visual medium. He shared some of the work he had done and also shared a bit about how blender works with people who wanted to learn about that.
Mayur, whom you see in the picture pointing out something about FOSS and this was the culture that we strove to have. I know and love and hate the browser but haven t been able to fathom the recklessness that Mozilla has been doing the last few years, which has just been having one mis-adventure after another.
For instance, mozstumbler was an effort which I thought would go places. From what little I understood, it served/serves as a user-friendly interface to a potential user while still sharing all the data with OSM . They (Mozilla) seems/seemed to have a fatalistic take as it provided initial funding but then never fully committing to the project.
Later, at night we had the whole free software and open-source sharings where I tried to emphasize that without free software, the term open-source would not have come into existence. We talked and talked and somewhere around 02:00 I slept, the next day was an extension of the first day itself where we ribbed each other good-naturedly and still shared whatever we could share with each other.
I do hope that we continue this tradition for great many years to come and engage with more and more people every passing year.
What had been interesting about the whole journey were the new people who were bringing all their passion and creativity to the fore. From the mozilla community, we had Akshay who is supposed to be a wizard on graphics, animation, editing anything to do with the visual medium. He shared some of the work he had done and also shared a bit about how blender works with people who wanted to learn about that.
Mayur, whom you see in the picture pointing out something about FOSS and this was the culture that we strove to have. I know and love and hate the browser but haven t been able to fathom the recklessness that Mozilla has been doing the last few years, which has just been having one mis-adventure after another.
For instance, mozstumbler was an effort which I thought would go places. From what little I understood, it served/serves as a user-friendly interface to a potential user while still sharing all the data with OSM . They (Mozilla) seems/seemed to have a fatalistic take as it provided initial funding but then never fully committing to the project.
Later, at night we had the whole free software and open-source sharings where I tried to emphasize that without free software, the term open-source would not have come into existence. We talked and talked and somewhere around 02:00 I slept, the next day was an extension of the first day itself where we ribbed each other good-naturedly and still shared whatever we could share with each other.
I do hope that we continue this tradition for great many years to come and engage with more and more people every passing year.  There s a pattern that comes up from time to time in the release management of free software projects.
To allow for big, disruptive changes, a new development branch is created. Most of the developers focus moves to the development branch. However at the same time, the users focus stays on the stable branch.
As a result:
There s a pattern that comes up from time to time in the release management of free software projects.
To allow for big, disruptive changes, a new development branch is created. Most of the developers focus moves to the development branch. However at the same time, the users focus stays on the stable branch.
As a result:
Before the 2.6 series, there was a stable branch (2.4) where only relatively minor and safe changes were merged, and an unstable branch (2.5), where bigger changes and cleanups were allowed. Both of these branches had been maintained by the same set of people, led by Torvalds. This meant that users would always have a well-tested 2.4 version with the latest security and bug fixes to use, though they would have to wait for the features which went into the 2.5 branch. The downside of this was that the stable kernel ended up so far behind that it no longer supported recent hardware and lacked needed features. In the late 2.5 kernel series, some maintainers elected to try backporting of their changes to the stable kernel series, which resulted in bugs being introduced into the 2.4 kernel series. The 2.5 branch was then eventually declared stable and renamed to 2.6. But instead of opening an unstable 2.7 branch, the kernel developers decided to continue putting major changes into the 2.6 branch, which would then be released at a pace faster than 2.4.x but slower than 2.5.x. This had the desirable effect of making new features more quickly available and getting more testing of the new code, which was added in smaller batches and easier to test. Then, in the Ruby community. In 2007, Ruby 1.8.6 was the stable version of Ruby. Ruby 1.9.0 was released on 2007-12-26, without being declared stable, as a snapshot from Ruby s trunk branch, and most of the development s attention moved to 1.9.x. On 2009-01-31, Ruby 1.9.1 was the first release of the 1.9 branch to be declared stable. But at the same time, the disruptive changes introduced in Ruby 1.9 made users stay with Ruby 1.8, as many libraries (gems) remained incompatible with Ruby 1.9.x. Debian provided packages for both branches of Ruby in Squeeze (2011) but only changed the default to 1.9 in 2012 (in a stable release with Wheezy 2013). Finally, in the Python community. Similarly to what happened with Ruby 1.9, Python 3.0 was released in December 2008. Releases from the 3.x branch have been shipped in Debian Squeeze (3.1), Wheezy (3.2), Jessie (3.4). But the python command still points to 2.7 (I don t think that there are plans to make it point to 3.x, making python 3.x essentially a different language), and there are talks about really getting rid of Python 2.7 in Buster (Stretch+1, Jessie+2). In retrospect, and looking at what those projects have been doing in recent years, it is probably a better idea to break early, break often, and fix a constant stream of breakages, on a regular basis, even if that means temporarily exposing breakage to users, and spending more time seeking strategies to limit the damage caused by introducing breakage. What also changed since the time those branches were introduced is the increased popularity of automated testing and continuous integration, which makes it easier to measure breakage caused by disruptive changes. Distributions are in a good position to help here, by being able to provide early feedback to upstream projects about potentially disruptive changes. And distributions also have good motivations to help here, because it is usually not a great solution to ship two incompatible branches of the same project. (I wonder if there are other occurrences of the same pattern?) Update: There s a discussion about this post on HN
 I started buying vinyl records about 16 years ago, but recently I've become a
bit uncomfortable being identified as a "vinyl lover". The market is ascendant,
with vinyl album sales growing for 8 consecutive years, at least in the UK. So
why am I uncomfortable about it?
A quick word about audio fidelity/quality here. I don't subscribe to the school
of thought that audio on vinyl is inherently better than digital audio, far
from it. I'm aware of its limitations. For recordings that I love, I try to
seek out the best quality version available, which is almost always digital.
Some believe that vinyl is immune to the "loudness war" brickwall mastering
plaguing some modern releases, but for some of the worst offenders (Depeche
Mode's Playing The Angel; Red Hot Chili Pepper's Californication) I haven't
found the vinyl masterings to sound any different.
16 years ago
Let's go back to why I started buying vinyl. Back when I started, the world
was a very different place to what it is today. You could not buy most music
in a digital form: it was 3 more years before the iTunes Store was opened, and
it was Mac-only at first, and the music it sold was DRM-crippled for the first
5 or so years afterwards. The iPod had not been invented yet and there was no
real market for personal music players. Minidiscs were still around, but Net-MD
(the only sanctioned way to get digital music onto them from a computer) was
terrible.
Buying vinyl 16 years ago was a way to access music that was otherwise much
harder to reach. There were still plenty of albums, originally recorded and
released before CDs, which either had not been re-issued digitally at all, or
had been done so early, and badly. Since vinyl was not fashionable, the second
hand market was pretty cheap. I bought quite a lot of stuff for pennies at
markets and car boot sales.
Some music such as b-sides and 12" mixes and other mixes prepared especially
for the format remains unavailable and uncollected on CD. (I'm a big fan of
the B-side culture that existed prior to CDs. I might write more about that
one day.)
10 years ago
Fast forward to around 10 years ago. Ephemeral digital music is now much more
common, the iPod and PMPs are well established. High-street music stores start
to close down, including large chains like MOS, Our Price, and Virgin.
Streaming hasn't particularly taken off yet, attempts to set up digital radio
stations are fought by the large copyright owners. Vinyl is still not
particularly fashionable, but it is still being produced, in particular for
singles for up-and-coming bands in 7" format. You can buy a 7" single for
between 1 and 4, getting the b-side with it. The b-side is often exclusive to
the 7" release as an incentive to collectors. I was very prepared to punt 1-2
on a single from a group I was not particularly familiar with just to see what
they were like. I discovered quite a lot of artists this way. One of the songs
we played at our wedding was such an exclusive: a recording of the Zutons'
covering Jackie Wilson's "Higher and Higher", originally broadcast once on
Colin Murray's Evening Session radio show.
Now
So, where are we now?
Vinyl album sales are a huge growth market. They are very fashionable. Many
purchasers are younger people who are new to the format; it's believed many
don't have the means to play the music on the discs. Many (most?) albums are
now issued as 12" vinyl in parallel with digital releases. These are usually
exactly the same product (track listing, mixes, etc.) and usually priced at
exactly twice that of the CD (with digital prices normally a fraction under
that).
The second hand market for 12" albums has inflated enormously. Gone are the
bargains that could be had, a typical second hand LP is now priced quite
close to the digital price for a popular/common album in most places.
The popularity of vinyl has caused a huge inflation in the price of most 7"
singles, which average somewhere between 8- 10 each, often without any b-side
whatsoever. The good news is from my observations the 2nd hand market for 7"
singles hasn't been affected quite as much. I guess they are not as desirable
to buyers.
The less said about Record Store Day, the better.
So, that's all quite frustrating. But most of the reasons I used to buy vinyl
have gone away anyway. Many of the rushed-to-market CD masterings have been
reworked and reissued, correcting the earlier problems. B-side compilations are
much more common so there are far fewer obscure tracks or mixes, and when the
transfer has been done right, you're getting those previously-obscure tracks in
a much higher quality. Several businesses exist to sell 2nd hand CDs for rock
bottom prices, so it's still possible to get popular music very cheaply.
The next thing to worry about is probably streaming services.
I started buying vinyl records about 16 years ago, but recently I've become a
bit uncomfortable being identified as a "vinyl lover". The market is ascendant,
with vinyl album sales growing for 8 consecutive years, at least in the UK. So
why am I uncomfortable about it?
A quick word about audio fidelity/quality here. I don't subscribe to the school
of thought that audio on vinyl is inherently better than digital audio, far
from it. I'm aware of its limitations. For recordings that I love, I try to
seek out the best quality version available, which is almost always digital.
Some believe that vinyl is immune to the "loudness war" brickwall mastering
plaguing some modern releases, but for some of the worst offenders (Depeche
Mode's Playing The Angel; Red Hot Chili Pepper's Californication) I haven't
found the vinyl masterings to sound any different.
16 years ago
Let's go back to why I started buying vinyl. Back when I started, the world
was a very different place to what it is today. You could not buy most music
in a digital form: it was 3 more years before the iTunes Store was opened, and
it was Mac-only at first, and the music it sold was DRM-crippled for the first
5 or so years afterwards. The iPod had not been invented yet and there was no
real market for personal music players. Minidiscs were still around, but Net-MD
(the only sanctioned way to get digital music onto them from a computer) was
terrible.
Buying vinyl 16 years ago was a way to access music that was otherwise much
harder to reach. There were still plenty of albums, originally recorded and
released before CDs, which either had not been re-issued digitally at all, or
had been done so early, and badly. Since vinyl was not fashionable, the second
hand market was pretty cheap. I bought quite a lot of stuff for pennies at
markets and car boot sales.
Some music such as b-sides and 12" mixes and other mixes prepared especially
for the format remains unavailable and uncollected on CD. (I'm a big fan of
the B-side culture that existed prior to CDs. I might write more about that
one day.)
10 years ago
Fast forward to around 10 years ago. Ephemeral digital music is now much more
common, the iPod and PMPs are well established. High-street music stores start
to close down, including large chains like MOS, Our Price, and Virgin.
Streaming hasn't particularly taken off yet, attempts to set up digital radio
stations are fought by the large copyright owners. Vinyl is still not
particularly fashionable, but it is still being produced, in particular for
singles for up-and-coming bands in 7" format. You can buy a 7" single for
between 1 and 4, getting the b-side with it. The b-side is often exclusive to
the 7" release as an incentive to collectors. I was very prepared to punt 1-2
on a single from a group I was not particularly familiar with just to see what
they were like. I discovered quite a lot of artists this way. One of the songs
we played at our wedding was such an exclusive: a recording of the Zutons'
covering Jackie Wilson's "Higher and Higher", originally broadcast once on
Colin Murray's Evening Session radio show.
Now
So, where are we now?
Vinyl album sales are a huge growth market. They are very fashionable. Many
purchasers are younger people who are new to the format; it's believed many
don't have the means to play the music on the discs. Many (most?) albums are
now issued as 12" vinyl in parallel with digital releases. These are usually
exactly the same product (track listing, mixes, etc.) and usually priced at
exactly twice that of the CD (with digital prices normally a fraction under
that).
The second hand market for 12" albums has inflated enormously. Gone are the
bargains that could be had, a typical second hand LP is now priced quite
close to the digital price for a popular/common album in most places.
The popularity of vinyl has caused a huge inflation in the price of most 7"
singles, which average somewhere between 8- 10 each, often without any b-side
whatsoever. The good news is from my observations the 2nd hand market for 7"
singles hasn't been affected quite as much. I guess they are not as desirable
to buyers.
The less said about Record Store Day, the better.
So, that's all quite frustrating. But most of the reasons I used to buy vinyl
have gone away anyway. Many of the rushed-to-market CD masterings have been
reworked and reissued, correcting the earlier problems. B-side compilations are
much more common so there are far fewer obscure tracks or mixes, and when the
transfer has been done right, you're getting those previously-obscure tracks in
a much higher quality. Several businesses exist to sell 2nd hand CDs for rock
bottom prices, so it's still possible to get popular music very cheaply.
The next thing to worry about is probably streaming services.
 After I took care of parking the plane, I went to find the car. Except the car was missing. Some other pilot had flown in the same day and was using it, according to the logbook on the desk. I called the number on a sign which rang to the sheriff s office and they confirmed it. According to the logbook, this was only the third time that car had been driven since Thanksgiving. Were we stuck at the airport a few miles out of down?
Nope. Mom called the people we were going to meet, a wonderful couple in their upper 80s. They drove out to pick us up. I m rather glad the car was gone, because I had such a great time visiting with them. Norris told me about the days when the state highways were gravel how they d have to re-blade them every few days due to all the traffic. I heard about what happened when the people in that community heard of some folks in Africa in need of car equipment they modified a tractor to fit in a shipping container and shipped it to Africa, along with a lot of books, blankets, supplies, and anything else needed to fill up a huge shipping container. Sounds like something people around here would do.
We drove around a couple of the small towns. The town my mom grew up in has seen better days. Its schools closed years ago, the old hotel whose owner gave her piano lessons is condemned, and many houses have been lost. But the town lives on. A new community center was built a few years ago. The grain elevator is expanding. Every time a business on Main Street closes, the grocery store expands a little bit: it s now a grocery store with a little hardware store and a little restaurant mixed in. The mall , as the locals jokingly call it. And, of course, two beautiful small churches still meet every Sunday. Here s the one my mom attended as a child.
After I took care of parking the plane, I went to find the car. Except the car was missing. Some other pilot had flown in the same day and was using it, according to the logbook on the desk. I called the number on a sign which rang to the sheriff s office and they confirmed it. According to the logbook, this was only the third time that car had been driven since Thanksgiving. Were we stuck at the airport a few miles out of down?
Nope. Mom called the people we were going to meet, a wonderful couple in their upper 80s. They drove out to pick us up. I m rather glad the car was gone, because I had such a great time visiting with them. Norris told me about the days when the state highways were gravel how they d have to re-blade them every few days due to all the traffic. I heard about what happened when the people in that community heard of some folks in Africa in need of car equipment they modified a tractor to fit in a shipping container and shipped it to Africa, along with a lot of books, blankets, supplies, and anything else needed to fill up a huge shipping container. Sounds like something people around here would do.
We drove around a couple of the small towns. The town my mom grew up in has seen better days. Its schools closed years ago, the old hotel whose owner gave her piano lessons is condemned, and many houses have been lost. But the town lives on. A new community center was built a few years ago. The grain elevator is expanding. Every time a business on Main Street closes, the grocery store expands a little bit: it s now a grocery store with a little hardware store and a little restaurant mixed in. The mall , as the locals jokingly call it. And, of course, two beautiful small churches still meet every Sunday. Here s the one my mom attended as a child.
 We drove past the marker at the geographic center of the contiguous United States. Norris saw some other visitors, rolled down his windows, and treated them and us to an unexpected story of the time thousands of people banded together to completely build a house in a single day, just down the road. Smiles all around.
So here I was, nearly 200 miles from home, in an unfamiliar town but one where I could just feel the goodness. After spending a few hours with these people, I felt like they were old friends.
As I flew us home, I spotted one of my favorite Kansas sights: a beautiful sunset. From the plane, it almost looks like the land at the horizon turns blue like the ocean, and above it the last hint of sun paints the canvas-sky.
In this week of controversy, politics, and reports of violence, it reminds me that we all get the privilege of sharing this beautiful Earth. I didn t ask anybody on that trip about their politics, religion, or opinions on any of the divisive issues of the day. Whether they agree with me on those things or not is irrelevant. I got to spend a day with good-hearted and delightful people, so I flew back with a smile.
We drove past the marker at the geographic center of the contiguous United States. Norris saw some other visitors, rolled down his windows, and treated them and us to an unexpected story of the time thousands of people banded together to completely build a house in a single day, just down the road. Smiles all around.
So here I was, nearly 200 miles from home, in an unfamiliar town but one where I could just feel the goodness. After spending a few hours with these people, I felt like they were old friends.
As I flew us home, I spotted one of my favorite Kansas sights: a beautiful sunset. From the plane, it almost looks like the land at the horizon turns blue like the ocean, and above it the last hint of sun paints the canvas-sky.
In this week of controversy, politics, and reports of violence, it reminds me that we all get the privilege of sharing this beautiful Earth. I didn t ask anybody on that trip about their politics, religion, or opinions on any of the divisive issues of the day. Whether they agree with me on those things or not is irrelevant. I got to spend a day with good-hearted and delightful people, so I flew back with a smile.

% time ./bin/eierskap-dotty 958033540 > dagbladet.dot real 0m2.841s user 0m0.184s sys 0m0.036s %The script accept several organisation numbers on the command line, allowing a cluster of companies to be graphed in the same image. The resulting dot file for the example above look like this. The edges are labeled with the ownership percentage, and the nodes uses the organisation number as their name and the name as the label:
digraph ownership rankdir = LR; "Aller Holding A/s" -> "910119877" [label="100%"] "910119877" -> "998689015" [label="100%"] "998689015" -> "958033540" [label="99%"] "974530600" -> "958033540" [label="1%"] "958033540" [label="AS DAGBLADET"] "998689015" [label="Berner Media Holding AS"] "974530600" [label="Dagbladets Stiftelse"] "910119877" [label="Aller Media AS"]To view the ownership graph, run "dotty dagbladet.dot" or convert it to a PNG using "dot -T png dagbladet.dot > dagbladet.png". The result can be seen below:
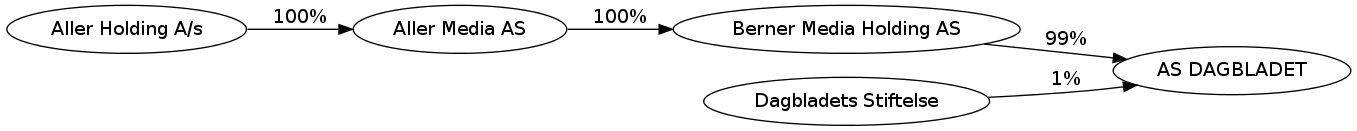 Note that I suspect the "Aller Holding A/S" entry to be incorrect
data in the official ownership register, as that name is not
registered in the official company register for Norway. The ownership
register is sensitive to typos and there seem to be no strict checking
of the ownership links.
Let me know if you improve the script or find better data sources.
The code is licensed according to GPL 2 or newer.
Update 2015-06-15: Since the initial post I've been told that
"Aller
Holding A/S" is a Danish company, which explain why it did not
have a Norwegian organisation number. I've also been told that there
is a web
services API available from Br nn ysundsregistrene, for those
willing to accept the terms or pay the price.
Note that I suspect the "Aller Holding A/S" entry to be incorrect
data in the official ownership register, as that name is not
registered in the official company register for Norway. The ownership
register is sensitive to typos and there seem to be no strict checking
of the ownership links.
Let me know if you improve the script or find better data sources.
The code is licensed according to GPL 2 or newer.
Update 2015-06-15: Since the initial post I've been told that
"Aller
Holding A/S" is a Danish company, which explain why it did not
have a Norwegian organisation number. I've also been told that there
is a web
services API available from Br nn ysundsregistrene, for those
willing to accept the terms or pay the price.
 Over the past week I've mailed many of the people who had signed my previous GPG key and who had checked my ID as part of that process. My intention was to ask "Hey you trusted me before, would you sign my new key?".
So far no replies. I may have to be more dedicated and do the local-thing with people.
In other news Bytemark, who have previously donated a blade server, sponsored Debconf, and done other similar things, have now started offering free hosting to Debian-developers.
There is a list of such offers here:
I think that concludes this months blog-posting quota. Although who knows? I turn 39 in a couple of days, and that might allow me to make a new one.
Over the past week I've mailed many of the people who had signed my previous GPG key and who had checked my ID as part of that process. My intention was to ask "Hey you trusted me before, would you sign my new key?".
So far no replies. I may have to be more dedicated and do the local-thing with people.
In other news Bytemark, who have previously donated a blade server, sponsored Debconf, and done other similar things, have now started offering free hosting to Debian-developers.
There is a list of such offers here:
I think that concludes this months blog-posting quota. Although who knows? I turn 39 in a couple of days, and that might allow me to make a new one.
Next.