Birger Schacht: Another round of rust
carl
The first thing I did was updating carl. I updated all
the dependencies and switched the dependency that does coloring from
ansi_term, which is
unmaintained, to
nu-ansi-term. When I then updated the
clap dependency to version 4 I realized that
clap now depends on the anstyle crate for
text styling - so I updated carls coloring code once again so it now uses
anstyle, which led to less dependencies overall. Implementing this change I
also did some refactoring of the code.
carl how also has its own website as well as a
subdomain1.
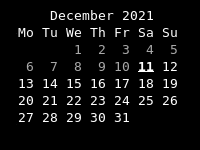
I also added a couple of new date properties to carl, namely all weekdays as
well as odd and even - this means it is now possible choose a separate color
for every weekday and have a rainbow calendar:
 This is included in version 0.1.0 of carl, which I published on
crates.io.
This is included in version 0.1.0 of carl, which I published on
crates.io.
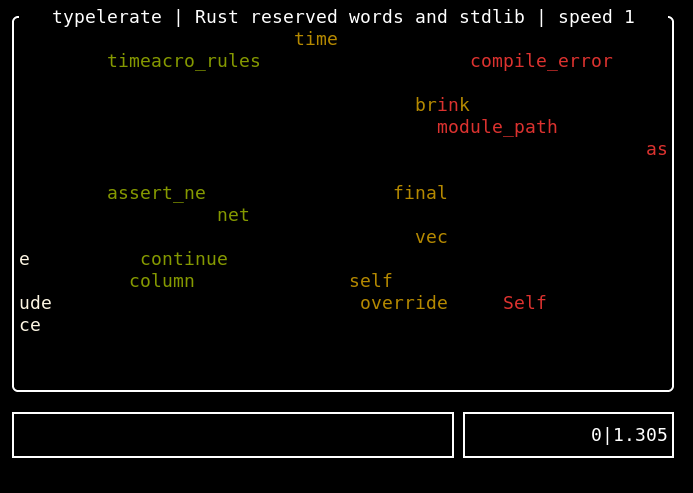
typelerate
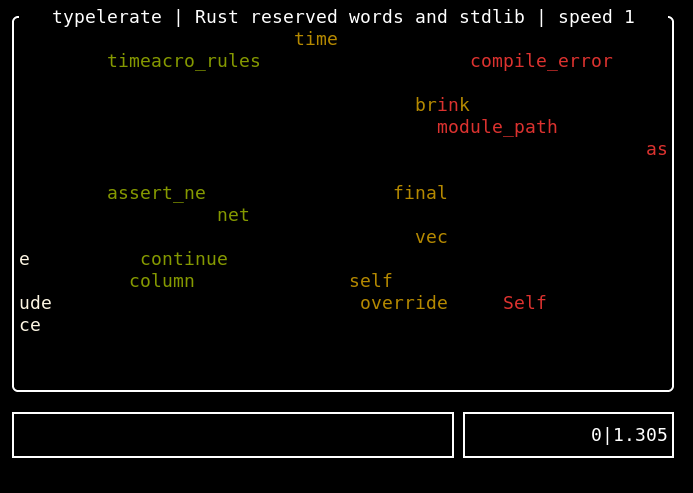
Then I started writing my first game -
typelerate. It is a copy of the great
typespeed, without the multiplayer
support.
To describe the idea behind the game, I quote the typespeed website:
Typespeed s idea is ripped from ztspeed (a DOS game made by Zorlim). The
Idea behind the game is rather easy: type words that are flying by from left
to right as fast as you can. If you miss 10 or more words, game is over.
Instead of the multiplayer support, typelerate works with UTF-8 strings and
it also has another game mode: in typespeed you only type whats scrolling
via the screen. In typelerate I added the option to have one or more
answer strings. One of those has to be typed instead of the word flying
across the screen. This lets you implement kind of an question/answer game. To
be backwards compatible with the existing wordfiles from typespeed2, the
wordfiles for the question/answer games contain comma separated values. The
typelerate repository contains
wordfiles with Python and Rust keywords as well as wordfiles where you are
shown an Emoji and you have to type the corresponding Github shortcode. I m
happy to add additional wordfiles (there could be for example math
questions ).
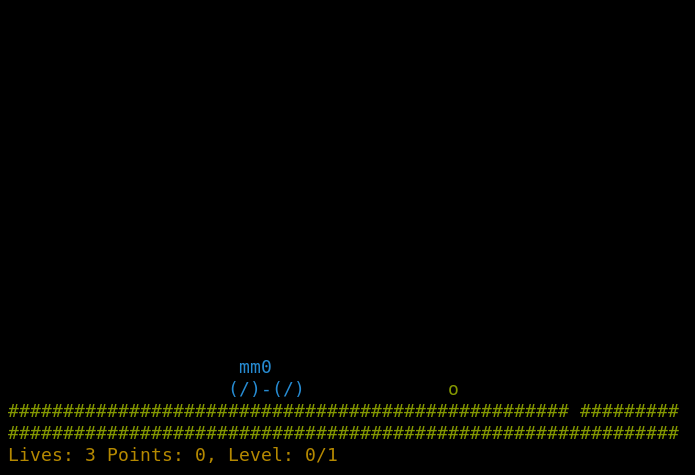
marsrover
Another commandline game I really like, because I am fascinated by the animated
ASCII graphics, is the venerable
moon-buggy. In this game you have to
drive a vehicle across the moon s surface and deal with obstacles like craters or
aliens.
I reimplemented the game in rust and called it marsrover:
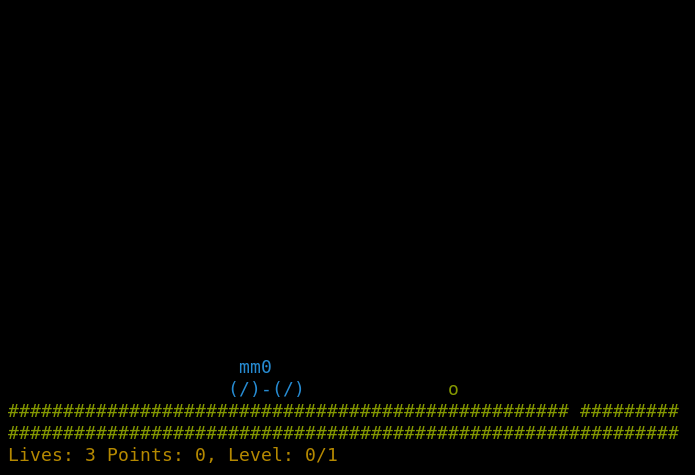 I published it on crates.io, you can find
the repository on github. The game uses
a configuration file in
I published it on crates.io, you can find
the repository on github. The game uses
a configuration file in $XDG_CONFIG_HOME/marsrover/config.toml - you can
configure the colors of the elements as well as the levels. The game comes with
four levels
predefined,
but you can use the configuration file to override that list of levels with
levels with your own properties. The level properties define the probabilities
of obstacles occuring on your way on the mars surface and a points setting that
defines how many points the user can get in that level (=the game switches to
the next level if the user reaches the points).
[[levels]]
prob_ditch_one = 0.2
prob_ditch_two = 0.0
prob_ditch_three = 0.0
prob_alien = 0.5
points = 100
After the last level, the game generates new ones on the fly.
-
thanks to the service from https://cli.rs.
-
actually,
typelerate is not backwards compatible with the typespeed
wordfiles, because those are not UTF-8 encoded
Typespeed s idea is ripped from ztspeed (a DOS game made by Zorlim). The Idea behind the game is rather easy: type words that are flying by from left to right as fast as you can. If you miss 10 or more words, game is over.Instead of the multiplayer support,
typelerate works with UTF-8 strings and
it also has another game mode: in typespeed you only type whats scrolling
via the screen. In typelerate I added the option to have one or more
answer strings. One of those has to be typed instead of the word flying
across the screen. This lets you implement kind of an question/answer game. To
be backwards compatible with the existing wordfiles from typespeed2, the
wordfiles for the question/answer games contain comma separated values. The
typelerate repository contains
wordfiles with Python and Rust keywords as well as wordfiles where you are
shown an Emoji and you have to type the corresponding Github shortcode. I m
happy to add additional wordfiles (there could be for example math
questions ).
marsrover
Another commandline game I really like, because I am fascinated by the animated
ASCII graphics, is the venerable
moon-buggy. In this game you have to
drive a vehicle across the moon s surface and deal with obstacles like craters or
aliens.
I reimplemented the game in rust and called it marsrover:
 I published it on crates.io, you can find
the repository on github. The game uses
a configuration file in
I published it on crates.io, you can find
the repository on github. The game uses
a configuration file in $XDG_CONFIG_HOME/marsrover/config.toml - you can
configure the colors of the elements as well as the levels. The game comes with
four levels
predefined,
but you can use the configuration file to override that list of levels with
levels with your own properties. The level properties define the probabilities
of obstacles occuring on your way on the mars surface and a points setting that
defines how many points the user can get in that level (=the game switches to
the next level if the user reaches the points).
[[levels]]
prob_ditch_one = 0.2
prob_ditch_two = 0.0
prob_ditch_three = 0.0
prob_alien = 0.5
points = 100
After the last level, the game generates new ones on the fly.
-
thanks to the service from https://cli.rs.
-
actually,
typelerate is not backwards compatible with the typespeed
wordfiles, because those are not UTF-8 encoded
[[levels]]
prob_ditch_one = 0.2
prob_ditch_two = 0.0
prob_ditch_three = 0.0
prob_alien = 0.5
points = 100
- thanks to the service from https://cli.rs.
-
actually,
typelerateis not backwards compatible with thetypespeedwordfiles, because those are not UTF-8 encoded
 The default output of
The default output of 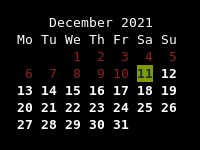 You can change the foreground color, background color and/or style of a date
using a combination of various stylenames like
You can change the foreground color, background color and/or style of a date
using a combination of various stylenames like 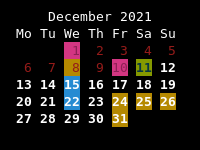 Using the
Using the  I recently bought a Pinebook Pro. This was mainly out of general interest,
but also because I wanted to have a spare portable computer. When I was
recently having some difficulty with my laptop not charging, I realised that I
am dependent on having access to Emacs, notmuch.el and my usual git
repositories in the way that most people are dependent on their smartphones
all the info I need to get things done is in there, and it s very disabling
not to have it. So, good to have a spare.
I decided to get the machine running the hard way, and have been working to
add a facility to install the device-specific bootloader to
I recently bought a Pinebook Pro. This was mainly out of general interest,
but also because I wanted to have a spare portable computer. When I was
recently having some difficulty with my laptop not charging, I realised that I
am dependent on having access to Emacs, notmuch.el and my usual git
repositories in the way that most people are dependent on their smartphones
all the info I need to get things done is in there, and it s very disabling
not to have it. So, good to have a spare.
I decided to get the machine running the hard way, and have been working to
add a facility to install the device-specific bootloader to
 The following contributors got their Debian Developer accounts in the last two months:
The following contributors got their Debian Developer accounts in the last two months: