
I mentioned this briefly yesterday, but now I'll try to summarize the
story of a great surprise and a big moment for me.
All this started when my wife
Elizabeth and my son Jean-Baptiste wanted to do something special for
my 50th birthday. So, it indeed all started months ago, probably early
March or something (I don't yet have all the details).
Jean-Baptiste described this well on the web site, so I won't go again
into details, but basically, this was about getting birthday
wishes from my "free software family" in, as you might guess, as many
languages as possible.
Elizabeth brought the original idea and JB helped her by setting up
the website and collecting e-mail addresses of people I usually work
with: he grabbed addresses from PO files on Debian website, plus some
in his own set of GPG signatures and here we go. And then he started poking
dozens of you folks in order to get your wishes for this birthday.
Gradually, contributions accumulated on the website, with
many challenges for them: be sure to get as many people as possible,
poking and re-poking all those FLOSS people who keep forgetting
things... It seems that poking people is something that's probably in
the Perrier's genes!
And they were doing all this without me noticing.
As usually in Debian, releasing on time is a no-no. So, it quickly
turned out that having everything ready by April 2nd wouldn't be
possible. So, their new goal was offering this to me on Pentecost
Sunday, which was yesterday. And...here comes the gift.
Aha, this looks like a photo album. Could it be a "50 years of
Christian" album?
But, EH, why is that pic of me, with the red Debconf5 tee-shirt (that
features a world map) and a "bubulle" sign, in front of the book?
But, EH EH EH, what the .... are doing these word by H0lger, then Fil,
then Joey doing on the following pages?
And only then, OMG, I discover the real gift they prepared. 106, often
bilingual, wishes from 110 people (some were couples!). 18 postcards
(one made of wood). 45 languages. One postcard with wishes from nearly every distro
representatives at LinuxTag 2011. Dozens of photos from my friends all
around the world. All this in a wonderful album.
I can't tell what I said. Anyway, JB was shooting a video, so...we'll see. OK, I didn't cry...but it wasn't that far and
emotion was really really intense.
Guys, ladies, gentlemen, friends....it took me a while to realize what
you contributed to. It took me the entire afternoon to realize the
investment put by Elizabeth and JB (and JB's sisters support) into
this. Yes, as many of you wrote, I have an awesome family and they
really know how to share their love. I also have an awesome virtual
family all around the world. Your words are wholeheartedly appreciated
and some were indeed much much much appreciated.
Of course, I'll have the book in Banja Luka so that you can see the
result. I know (because JB and Elizabeth told me) that many of you
were really awaiting to see how it would be received (yes, that
includes you, in Germany, who I visited in early May!!!).
Again, thank you so much for this incredible gift. Thank you Holger Levsen, Phil Hands, Joey Hess, Lior Kaplan, Martin
Michlmayr, Alberto Gonzalez Iniesta, Kenshi "best friend" Muto,
Praveen Arimbrathodiyil, Felipe Augusto van de Wiel, Ana Carolina
Comandulli (5 postcards!), Stefano Zacchiroli (1st contribution
received by JB, of course), Gunnar Wolf, Enriiiiiico Zini, Clytie Siddall,
Frans Pop (by way of Clytie), Tenzin Dendup, Otavio Salvador, Neil
McGovern, Konstantinos Margaritis, Luk Claes, Jonas Smedegaard, Pema
Geyleg, Meike "sp tzle queen" Reichle, Alexander Reichle-Schmehl,
Torsten Werner, "nette BSD" folks, CentOS Ralph and
Brian, Fedora people, SUSE's Jan, Ubuntu's Lucia Tamara, Skolelinux'
Paul, Rapha l Hertzog, Lars Wirzenius, Andrew McMillan (revenge in
September!), Yasa Giridhar Appaji Nag (now I know my name in Telugu),
Amaya Rodrigo, St phane Glondu, Martin Krafft, Jon "maddog" Hall (and
God save the queen), Eddy Petri or, Daniel Nylander, Aiet Kolkhi,
Andreas "die Katze geht in die K che, wunderbar" Tille, Paul "lets
bend the elbow" Wise, Jordi "half-marathon in Banja Luka" Mallach,
Steve "as ever-young as I am" Langasek, Obey Arthur Liu, YAMANE
Hideki, Jaldhar H. Vyas, Vikram Vincent, Margarita "Bronx
cross-country queen" Manterola, Patty Langasek, Aigars Mahinovs
(finding a pic *with* you on it is tricky!), Thepittak
Karoonboonyanan, Javier "nobody expects the Spanish inquisition"
Fern ndez-Sanguino, Varun Hiremath, Moray Allan, David Moreno Garza,
Ralf "marathon-man" Treinen, Arief S Fitrianto, Penny Leach, Adam
D. Barrat, Wolfgang Martin Borgert, Christine "the mentee overtakes
the mentor" Spang, Arjuna Rao Chevala, Gerfried "my best contradictor"
Fuchs, Stefano Canepa, Samuel Thibault, Eloy "first samba maintainer"
Par s, Josip Rodin, Daniel Kahn Gillmor, Steve McIntyre, Guntupalli
Karunakar, Jano Gulja , Karolina Kali , Ben Hutchings, Matej Kova i ,
Khoem Sokhem, Lisandro "I have the longest name in this list" Dami n
Nicanor P rez-Meyer, Amanpreet Singh Alam, H ctor Or n, Hans
Nordhaugn, Ivan Mas r, Dr. Tirumurti Vasudevan, John "yes, Kansas is
as flat as you can imagine" Goerzen, Jean-Baptiste "Piwet" Perrier,
Elizabeth "I love you" Perrier, Peter Eisentraut, Jesus "enemy by
nature" Climent, Peter Palfrader, Vasudev Kamath, Miroslav "Chicky"
Ku e, Mart n Ferrari, Ollivier Robert, Jure uhalev, Yunqiang Su,
Jonathan McDowell, Sampada Nakhare, Nayan Nakhare, Dirk "rendez-vous
for Chicago marathon" Eddelbuettel, Elian Myftiu, Tim Retout, Giuseppe
Sacco, Changwoo Ryu, Pedro Ribeoro, Miguel "oh no, not him again" Figueiredo, Ana Guerrero,
Aur lien Jarno, Kumar Appaiah, Arangel Angov, Faidon Liambotis, Mehdi
Dogguy, Andrew Lee, Russ Allbery, Bj rn Steensrud, Mathieu Parent,
Davide Viti, Steinar H. Gunderson, Kurt Gramlich, Vanja Cvelbar, Adam
Conrad, Armi Be irovi , Nattie Mayer-Hutchings, Joerg "dis shuld be
REJECTed" Jaspert and Luca Capello.
Let's say it gain:
- Danke
- Thank you
- (RTL or not?) / toda
- Gracias
- / arigat
- / n ndi
- Obrigado
- Grazie
- C m n
- Kadin chey la
- / Efharisto
- Dank je wel
- Tak
- D ngge
- Merci
- Kiitos
- Tika hoki
- / dhanyavaadhamulu
- Thank you and God save the Queen
- Mul umesc
- Tack
- / didi madloba
- Gr cies
- Dakujem
- / Aabhar
li> / Dhanyavadagalu
- Paldies
- / kop khun krap
- Terima kasih
- Hvala (hr)
- / Dhanyavad
- / Hvala (sr)
- Hvala (sl)
- / Akun
- / Sukriya
- Takk
- / Nandri
- Maki biyen jianbakik
- D kuji
- / Xiexie
- / Aabhari aahe
- Faleminderit
- / Kam sah ham ni da
- / Blagodaram
- / Xiexie
- Hvala (bs)
 Debian Stretch feels like an excellent release by the Debian project.
The final stable release is about to happen in the short term.
Among the great things you can do with Debian, you could set up a VPN using
the openvpn software.
In this blog post I will describe how I ve deployed myself an openvpn server
using Debian Stretch, my network environment and my configurations & workflow.
Before all, I would like to reference my requisites and the characteristics of
what I needed:
Debian Stretch feels like an excellent release by the Debian project.
The final stable release is about to happen in the short term.
Among the great things you can do with Debian, you could set up a VPN using
the openvpn software.
In this blog post I will describe how I ve deployed myself an openvpn server
using Debian Stretch, my network environment and my configurations & workflow.
Before all, I would like to reference my requisites and the characteristics of
what I needed:
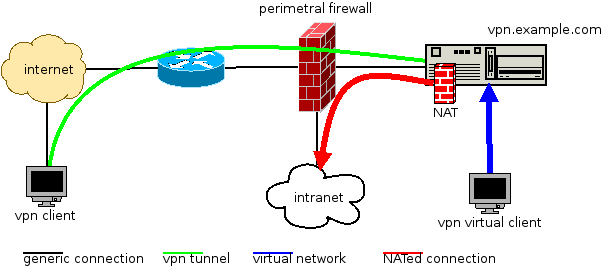 (DIA source file)
So, it works like this:
(DIA source file)
So, it works like this:
 (DIA source file)
In the nftables git tree, you should put a ruleset like this (a single file
named
(DIA source file)
In the nftables git tree, you should put a ruleset like this (a single file
named  I mentioned this briefly yesterday, but now I'll try to summarize the
story of a great surprise and a big moment for me.
I mentioned this briefly yesterday, but now I'll try to summarize the
story of a great surprise and a big moment for me.
 We escorted Sarge to its last home. 3.1r8 is done, thanks to all the
people who made it possible. A big thanks goes to James Troup, our
ftpmaster of the day doing all the grunt work of getting a new point
release out of the door.
To bring in a more personal feeling of who makes this all possible,
here is a list of people contributing uploads to 3.1r8 (mostly
people from our fabulous Security Team):
We escorted Sarge to its last home. 3.1r8 is done, thanks to all the
people who made it possible. A big thanks goes to James Troup, our
ftpmaster of the day doing all the grunt work of getting a new point
release out of the door.
To bring in a more personal feeling of who makes this all possible,
here is a list of people contributing uploads to 3.1r8 (mostly
people from our fabulous Security Team):